
Would you like to know how easy it is for your information to be stolen over Open Wi-Fi?
Joe Smith (very original name) and his friends are socializing at their local coffee shop when they remember that their friend’s birthday is this weekend. Their friend’s name is Sarah, and Sarah LOVES hibachi. So, Joe uses his phone and the cafe’s open Wi-Fi to navigate to a local hibachi Web site, called Quickway Hibachi. Joe wants to know if the restaurant will serve 10 or more people for Sarah’s birthday, so he leaves a message along with his contact information.

If you’re having trouble reading the image above, I can show you a closer-view of what Joe has submitted to Quickway Hibachi. Here is what he’s typed:

Unfortunately for Joe, I was sniffing the network in the back corner and was able to see his activity on my screen. I noticed that Joe made an http POST request to a web server, and I knew right away that I probably got some good information. Let’s see exactly what I was able to find:
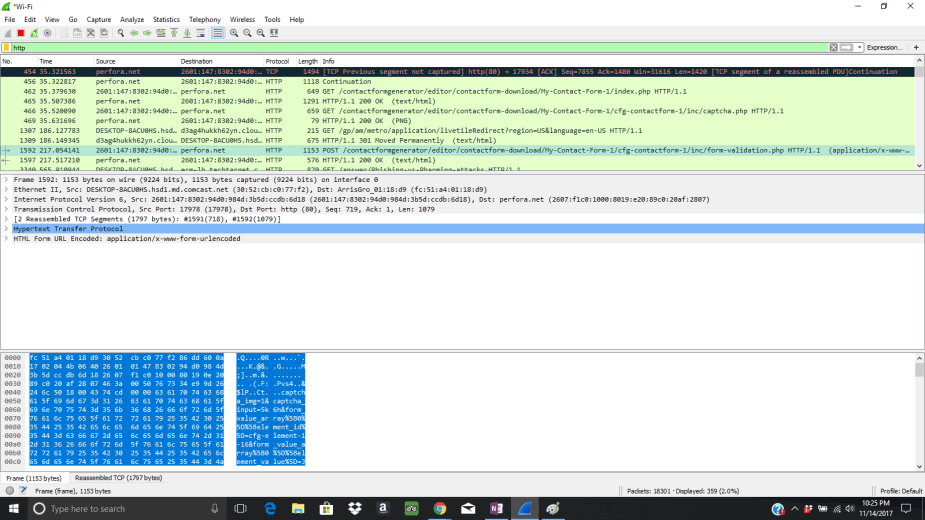
Hmm…not that great, but I know something useful is in this POST request. After digging deeper in the Details pane, I find exactly what I’m looking for:

Here’s a closer view of what I caught:

I was able to get Joe’s full name, his phone number, his email address, and the message he provided to Quickway Hibachi.
So, what can a hacker do with this information? How about we perform some spear phishing? Spear phishing is like regular phishing, except in this case, we are targeting a specific person. That’s why it’s called “spear” phishing. In a general sense, however, spear phishing refers to targeting groups of specific users in a corporate environment. Phishing, on the other hand, typically entails sending out mass phishing emails indiscriminately. Spear phishing emails can be well-thought-out and attentive emails, or they can be unsophisticated. Here’s a pretty unsophisticated example:

Within a few minutes, I’ve crafted a spear phishing email specifically made to fool Joe. It even includes some trust and familiarity because I’ve referenced his personal message regarding his friend’s birthday. More likely than not, Joe is going to click that link at the end of the email. Bitly is a URL shortener that allows hackers to evade security filters. As you can see, it also hides the real destination of the URL address.
What Joe doesn’t know is that that bitly link does not navigate to Quickway Hibachi. Instead, it navigates to my own malicious Web site, which contains harmful script that automatically exploits vulnerabilities in the Web browser and downloads malware onto his system. Err…I neglected to mention you’ll need to create a malicious Web site. It is much easier than you think. What that malware specifically does is completely up to me. For example, I could have a Trojan embedded in my Web site’s code.
If I was a more patient hacker, I could create a Web site that looked exactly like Quickway Hibachi’s Web site, and possibly….maybe….fool him into entering his credit card information. That’s not likely, but it’s certainly possible.
Another thing I could do is “smishing,” which is another name for SMS text message phishing.
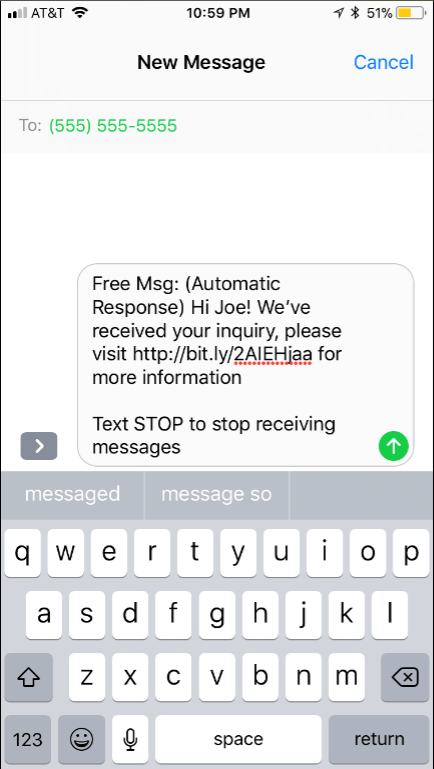
If I send this text message to Joe, he is also likely to click the malicious link and navigate to my malicious Web site.
But, both spear phishing emails and smishing messages don’t HAVE to be malicious. Sometimes, hackers will attach links to their legitimate Web sites simply to increase traffic to their Web site. For example, I might include the link http://www.quickwayhibachi.com/, but it ACTUALLY navigates to one of my latest posts that discusses click-bait protection! Joe might think he’s going to Quickway Hibachi, but he’s really going to get educated on click-bait ;).

