Introduction:
Ever wonder what lurks on the Dark Web? Hear any scary stories about contract killings? Weapons trading? Sex trafficking? Red rooms? These are all very real (with the exception of “red rooms.” They are, by and large, more of a myth).
At the surface, we have the Internet or the World Wide Web (WWW). It is anything indexed by our search engines. A step below that is the Deep Web. If you’re a little confused, I should clear something up. The Dark Web and the Deep Web are often used interchangeably. They are not the same thing. The Deep Web is anything on the World Wide Web (WWW) that is NOT indexed by search engines. With that being said, you probably use the Deep Web everyday. The Dark Web, however, is not part of the WWW at all. You cannot access the Dark Web with typical surface-level Web browsers (e.g., Internet Explorer, Google Chrome, Firefox, Safari, etc.). Henceforth, the Dark Web does will never use the usual “www.” addresses.
Note: If you are not interested in how TOR works, then skip ahead to the “Downloading and Using Tor” section at the bottom.

The Dark Web:
Before you assume the Dark Web is a really bad area of the Internet reserved for the lowest scums of the Earth, it really isn’t all that bad. It has its legitimate purposes. For example, we need the Dark Web for:
- Journalism: in countries where freedom of the press is restricted, journalists can use the Dark Web to document events as they unfold in their countries.
- Whistle Blowing: This can be good or bad depending on your perspective. For example, many see Edward Snowden as a hero while others view him as a traitor. But, in very corrupted countries, the Dark Web can be a safe-haven for whistle blowers who feel the need to expose government cover-ups and atrocities
- Chatrooms and forums: Again, this could be good or bad, but largely dependent on the circumstance. For example, the Dark Web might be a great place for LGBT communities to freely and anonymously express themselves. Or, it can be used for more malicious purposes, such as terrorism forums.
- Government surveillance: This might make you feel uneasy, but before you jump to any conclusions, I am referring to the NSA’s tracking and gathering of evidence on illegal activities on the Dark Web, such as pedophilia, sex trafficking, and drug dealing. The government lurks on the Dark Web too, and most of the time, they are investigating the bad guys. Just recently, they were able to take down Alpha Bay.
- Protection from ISP: If you didn’t already know, your Internet Service Provider (ISP) is able to see everything you do on the Internet. However, TOR can keep you anonymous.
- Circumvent surveillance and censorship: Many countries, such as China, have extremely strict censorship laws on Internet activity. Pretty much all your favorite Web sites are banned in China. No Facebook allowed. Just research the Great Firewall of China if you doubt me. I’m very against Internet censorship; fortunately, the Dark Web can be a good way to skirt these censorship laws.
But, yes, the Dark Web is used for more malicious reasons, such as:
- Child Pornography: The Dark Web hosts sites dedicated to child pornography. Pedophiles use the anonymity of the TOR browser to host these distorted hidden services.
- Weapons trade: Many criminals use the Dark Web to gain access to weapons that they cannot legally obtain.
- Drug trade: Out of all the bad things that occur on the Dark Web, this is perhaps the most common. Some people think of the Dark Web as an underground market area. There, you will find any drug you require. The Silk Road and Alpha Bay were two very popular Dark Web markets used to illegally distribute drugs and other goods and services until they were taken down by the U.S. government. The creator of Alpha Bay shot and killed himself before he could be prosecuted.
- Credit Cards: A lot of hackers will sell stolen credit card numbers on Dark Web market places. If you’ve ever been a victim of identity theft, your personal identifiable information could be stored on the Dark Web, waiting to be sold.
- Botnet and malware sales: Malware can be developed and sold for other hackers to use.
- Hitman-for-Hire: Surf the Dark Web long enough and you may discover areas for contract killings.
- Red Rooms: As I mentioned earlier, red room are a myth, but their existence should not be doubted. Red rooms are hideen sites for “video on-demand.” Visitors typically pay to view victims being tortured or sexually battered.
The Onion Router (TOR):

TOR is a browser used to surf the WWW anonymously, but it can also be used to access the Dark Web. Unlike our typical Web browsers that make direct connections to their destination, TOR uses virtual tunnels to obfuscate your IP address. Web sites cannot track you with cookies.
We use TOR to protect us from traffic analysis. When you access a Web site, the IP packets sent back-and-forth say a lot about who you are communicating with. Your ISP will always be able to see your Internet activity, browsing history, what you do, and the Web sites you visit will surely collect information about you too.
However, with TOR, traffic analysis becomes much more difficult. A TOR user’s traffic will effectually be routed and distributed through several places on the Internet. You see, when you use regular surface-level Web browsers, you make direct links to Web sites by making http GET requests to Web servers. Your IP packets traverse the Internet, hopping from router-to-router until it reaches the Web server hosting that IP address (assuming the hostname is already resolved). The Web server will respond back to you with the Web page you requested. This is a direct link. TOR does not do this. Instead, TOR takes a random pathway through several nodes to cover your tracks. No observer can tell where the data came from or where it is going. It is a twisty, hard-to-follow route.
How TOR Works:
To access a hidden service, TOR clients access a directory server for a list of “TOR nodes.” TOR nodes are systems that act as routers or relays. They basically forward traffic from node-to-node.

As we see in the image below, Alice accesses Bob’s hidden service by creating a random path of TOR nodes to traverse. Each TOR node relays information to the next TOR node in random order. A TOR node only knows two things: which TOR node sent the data and which TOR node to forward the data. No TOR node knows the original source of the data or its destination. A new set of encryption keys are negotiated each hop from TOR node-to-TOR node. Since the communication is encrypted, this will also stop hackers from initiating man-in-the-middle attacks. But, be warned, the communication between the exit TOR node and the hidden service is not encrypted.

A cool feature of TOR is that each time clients access a new hidden service, a new TOR circuit is created. It is just as random and also encrypted. Therefore, when Alice wants to access Jane’s hidden service, she will randomly traverse the TOR nodes in a new path.

Hidden Services:
Hidden services are also called “onion services.” They are exactly like Web sites; however, they are only accessible using the TOR browser. The cool thing about hidden services is that their IP addresses are hidden. This makes it difficult for adversaries to censor it or identify the owners. This is precisely why it is difficult for the U.S. government to take down WikiLeaks.
To access a hidden service, a TOR client must learn its onion address (good luck with that). Onion addresses are like http addresses, except they are typically a random, 16-character name that ends in “.onion.” However, onion services must advertise their existence as well. Therefore, hidden services randomly pick TOR nodes, build circuits with them, and allow them to act as introductory points for by telling them their public key. But, the location of the onion service is not revealed.

The hidden service will assemble what’s called a “hidden service descriptor.” This descriptor contains the onion service’s public key and a summary of the introductory points it selected. The descriptor is signed with the onion service’s private key and uploaded to a hash table.

That way, when a TOR client requests the onion service, the TOR client will download the descriptor from the hash table, and discover the introductory points and the correct public key to use. The TOR client will also create a circuit to a random TOR node and establish it as a rendezvous point by telling it a one-time-secret. The hidden service will present this one-time secret in step 5.

When the rendezvous point is ready, the TOR client will send an “introduce” message to the hidden service by sending it to one of the introductory points and request it be delivered to the hidden service. The introductory point uses the public key to encrypt the message.

The hidden service will then decrypt the TOR client’s “introduce” message with its private key and it also locates the address of the rendezvous point and the one-time secret. The hidden service will use this information to build a random circuit to the rendezvous point by sending it the one-time-secret.

Once the connection is established with the rendezvous point, the TOR client and the hidden service can use their TOR circuits to the rendezvous point to communicate with each other. Neither side knows the other’s IP address.

Downloading and Using TOR:

You can download TOR here. It is freely available for download and supports most operating systems, including Android smart phones.
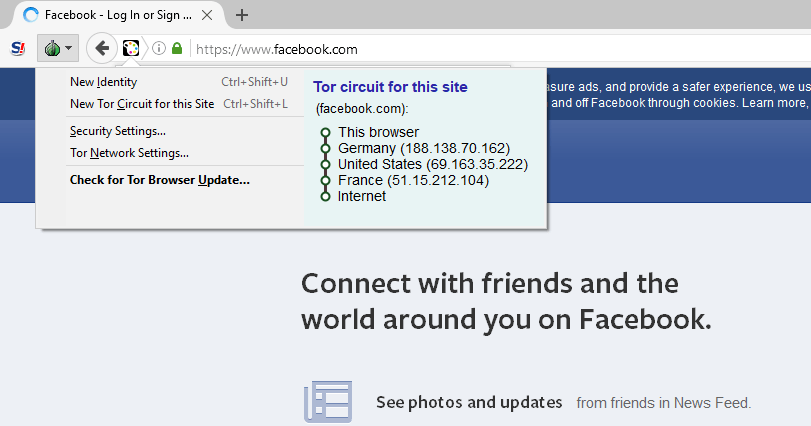
Once you have downloaded and installed TOR on to your desktop, you can use TOR just like any other Web browser. A cool feature of TOR is its “New Identity” and “New TOR Circuit for this Site” option. By selecting the “Onion” icon on the top left of the TOR browser, you can either create a new identity or a new TOR circuit for the current site. A new identity will close ALL of your tabs and windows, clear all private information, and will create new TOR circuits for all your current connections. The New TOR Circuit for this Site option will cause the currently active tab or window to be reloaded over a new TOR circuit.
If you want to access hidden services on the Dark Web, then you will need to know the exact onion address of the hidden service (hint: it’s right under your nose).
It’s highly advised that you do not install any additional add-ons or plug-ins as they can reveal your IP address. Flash is disabled by default because it cannot be easily made to obey the TOR browser’s proxy settings. The rules of safe surfing still apply. You should still use https and not http. If you recall, the traffic leaving the TOR exit node to the Web server is NOT encrypted. This last bit of encryption depends on whether or not the Web site is using SSL/TLS encryption. So, be careful using http Web sites.
I will leave you with the Onion address of DuckDuckGo, the TOR search engine: 3g2upl4pq6kufc4m.onion. You can access many of TOR’s other search engines, like Torch and the uncensored hidden Wiki. There, you can discover a lot of cool and perhaps disturbing things.
Happy surfing 🙂

