Throughout the years of Facebook hacking, hackers have discovered plenty of different methods for stealing Facebook credentials. Some are straightforward; others quite clever. But, just like a cat-and-mouse game, Facebook responds with an additional security feature to protect our accounts. Thus, many of the older and easier methods of acquiring Facebook credentials are going obsolete. This is precisely because Facebook now offers multi-factor authentication, tokens, link shim, geo-location, and encrypted e-mails. Essentially, stealing Facebook credentials has become increasingly difficult for hackers. In this post, I’ll show you exactly how hackers can still steal your Facebook credentials and what you can do to protect yourself.
By the way, It’s illegal to break into another person’s account and access their information without their explicit permission.
Phishing
There’s one, typically successful way of harvesting Facebook credentials: Hackers can go-phish. Social engineering, if done correctly, can work on a case-by-case basis. The best way to do this is to create a fake Facebook login page and send it to the victim. The trick is that it’s got to look exactly like the real one. But first, the hacker needs a Web site that’ll host the fake login page. In order to do that, a domain has to be registered with a domain registrar. Hackers are pretty smart; they aren’t going to use any of their personal information when registering their domain. They will most likely be operating behind a proxy to hide their location. So, anything they enter cannot be traced back to them. The domain is relatively inexpensive and shouldn’t be more than $15. After that, they can craft a Web site to look like an authentic Facebook login page like this one:
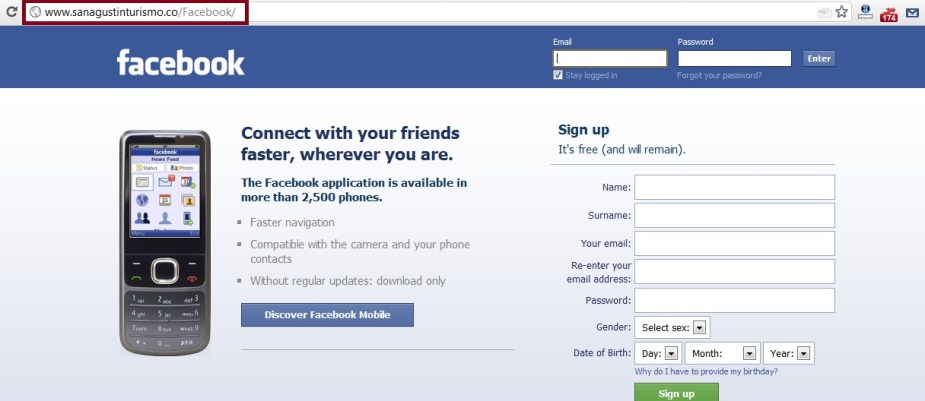
The Fake Facebook login page above looks exactly like the real Facebook login page; in fact, it’s exactly the same! The only difference is what’s in the URL bar. So, hackers try to reserve a similar domain that a victim wouldn’t second-glance.
But, you don’t need to be an expert in Web development and HTML to craft a fake Facebook login page. There are many tutorials online that shows you how to do this, but some leave out a lot of detail. An attacker can simply go to the Facebook login page, right click, and press “view page source.” They can then copy all of it and paste that into a text document:
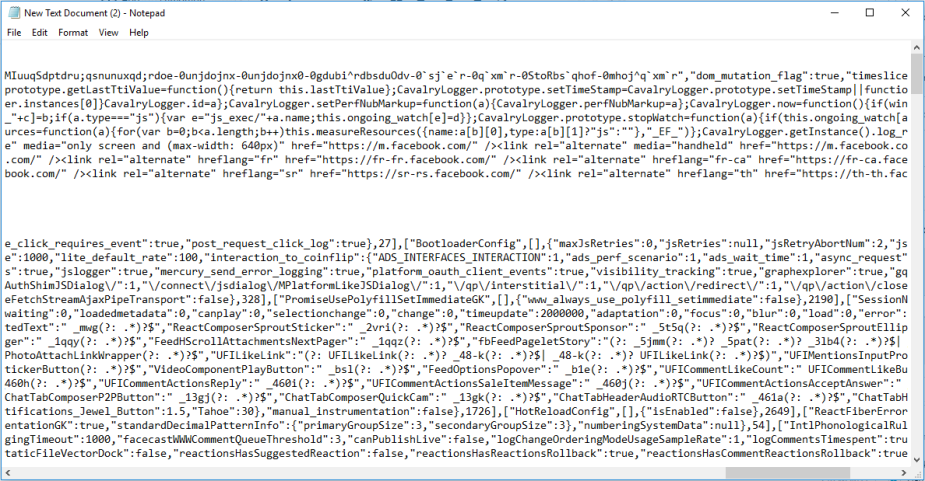
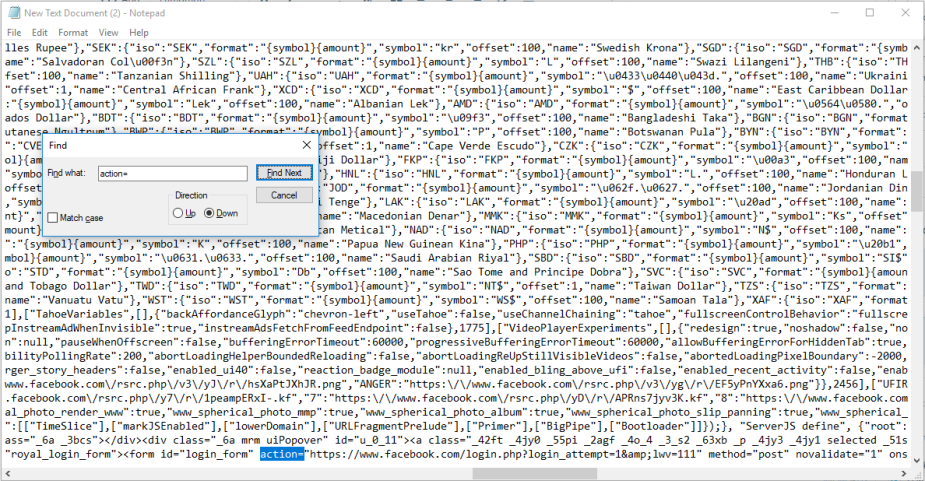
Next, they can press ctrl + f and search for “action=“. Whatever is to the right of “action=”, they can change to “log.php”. Creating the log.php file is in the next step. Attackers also need to change the method from “post” to “get.”
Attackers have to do this a couple times. The “method=” will be nearby. They then save this text file as a .php file. The “Save as Type” should be “All files” and the “Encoding” should be “Unicode.” It will not save if they try to save it in ASCII.
Next, they create a file that will help them export the login credentials. They do this by opening a new text file and pasting this php script into the text file. They can save it as “log.php” or something similar. This file will be used to log the victim’s Facebook login credentials.

After that’s finished, they can go to your web hosting account and upload both .txt files onto your Web site. Hackers can use their anonymous email accounts to deliver their malicious Web site to victims. There are many secure email services out there that they may use. However, some services can identify mass egress spam traffic.
Hackers can create an email account that looks legitimate. I’ll leave that up to your imagination, but again, hackers are never going to use any of their personal information. Many of these secure email providers offer you the option to create aliases that you can use. There are also additional software alternatives hackers use to send mass spam mail.
If hackers are targeting a specific victim, they’ll want to craft a specific email. I’ve crafted an email here for demonstration. It’s a pretty bland phishing email, but you’d be surprised by how many people get fooled by it.

The link to the hacker’s FAKE Facebook login page is hidden in the “Login with Facebook” call-to-action button. Because so many of us post our email addresses on our own Facebook pages, attackers can grab your friend’s email addresses. A tool called “theHarvester” is also worth mentioning. It can be used to collect email addresses in a domain.
Man-in-the-Middle and SSLstripping Attacks
Another way that hackers can obtain your Facebook login credentials is through a man-in-the-middle attack. This is when an attacker sits between you and the Facebook Web server. When you are out in public using Wi-Fi, your communication with Facebook’s Web servers are going through a nearby router. This router acts as the gateway between the local network you’re currently on and the Internet. The router will route your communication to the Web server usually on your behalf. But, a hacker can fool your computer or smartphone into thinking his computer is the router. When this happens, your device is fooled into sending all your traffic to the hacker’s computer. The hackers computer will then forward it to the router, which then travels to the Web server. Any communication coming back from the Web server goes back to the router, to the hacker’s computer, and then back to your device. This is all transparent to the victim, and the process is pretty automated for the hacker. But, if you’re having trouble visualizing this, just know that the hacker is sitting in the middle of the communication.
Man-in-the-middle attacks are set up using ARP poisoning. Our modern day switches, computers, and mobile devices contain an ARP table for easy communication between devices. It’s a table that associates MAC addresses with their corresponding IP addresses.
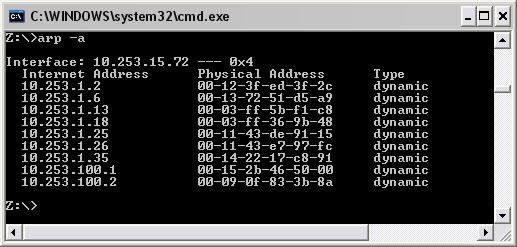
Imagine that this is an ARP table for our wireless router. Also, imagine that your device is the IP address 10.253.1.18 with the MAC address 00-03-ff-36-9b-48. A hacker will poison the gateway’s ARP table and state that your real MAC address is the hacker’s MAC address. The hacker will also poison your device’s ARP table as well by changing the MAC address of the wireless router to his MAC address. That way, all traffic hitting the wireless router coming from the Internet (which is intended for you at 10.253.1.18), will be routed to the hacker’s MAC address. Of course, you’ll receive your traffic too, but only after it passes through the hacker’s computer first. This works in vice versa when you are trying to communicate with the Facebook Web server out on the Internet. The takeaway is that the hacker is sitting in between you and the wireless router (also the Web server).
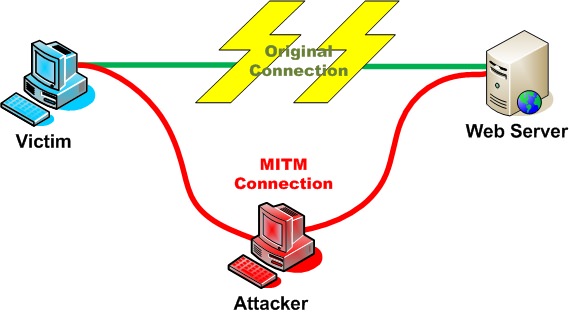
There are many ways to initiate a man-in-the-middle attack. Some hackers will enter ARP poisoning commands in the terminal and, once the machines are poisoned, they can enable IP forwarding and sniff the traffic going back and forth. Another way is to use Cain & Abel.
Cain & Abel can send hundreds of ARP requests over the network asking every host MAC address what their IP address is. On an example network, Cain & Abel returns the following active hosts:

These are all private IP addresses and are therefore not globally routable. We’ll assume that 10.0.0.1 is the wireless router/gateway and 10.0.0.92 is our victim. With Cain & Abel, we can poison both devices and sit between the iPhone and the wireless router by navigating to the APR tab. Once there, we can click the “+” sign and ARP poison the two devices to create a man-in-the-middle attack.
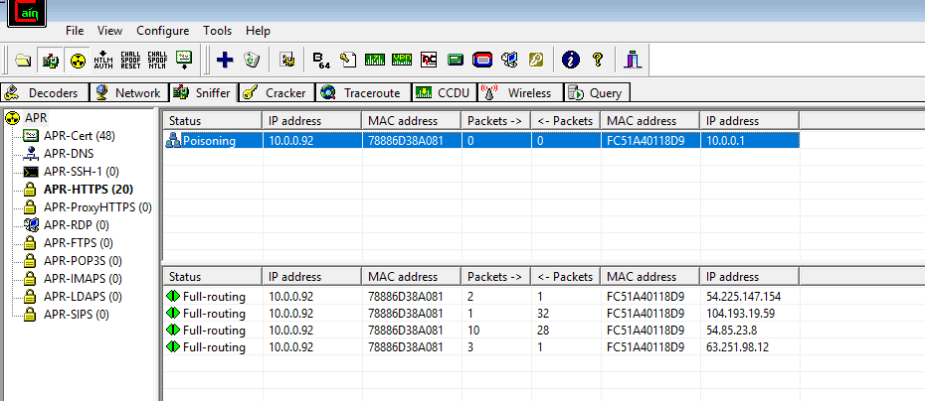
If the victim logs in to Facebook, attackers can capture the credentials in the http password tab. Over time, the password tab will fill with passwords captured in the past.
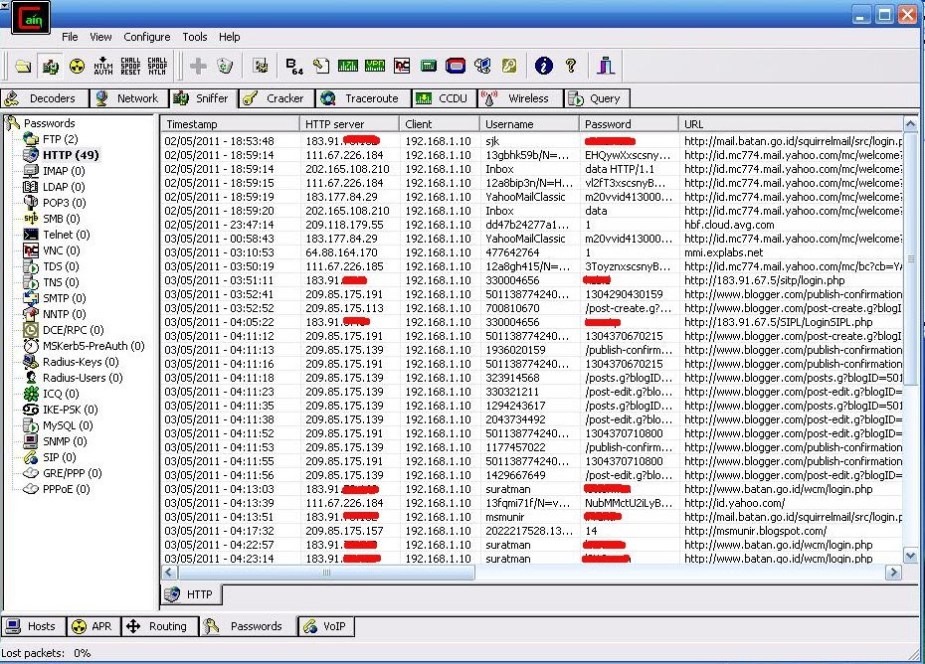
Unfortunately for the hacker, Facebook is using “https” these days to encrypt traffic. So, a favorite in the hacking community tends to be using Ettercap for initiating man-in-the-middle attacks and running sslstrip to decrypt the https traffic. With the traffic downgraded to plaintext, the Facebook credentials can be captured if the victim enters them in during the man-in-the-middle attack. If specified, the sslstripping tool can export the credentials and the encryption keys to a log file. You can see the sslstrip options below.
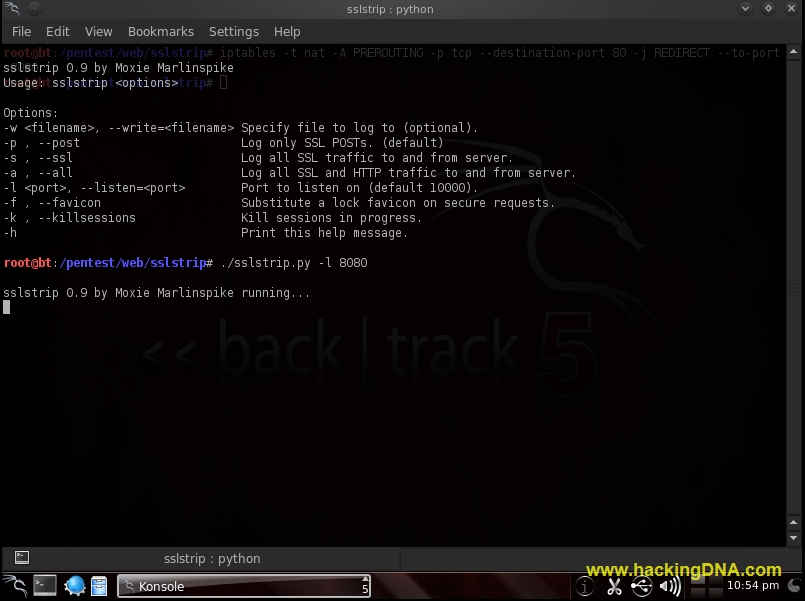
But, as the years go by, cybersecurity professionals are coming up with new ways to thwart hackers. Because of this, SSLstrip won’t always work, especially on popular Web browsers like Google Chrome and Firefox that have additional security features enabled. But, you can try your luck. Either way, hackers will find a new way to downgrade https.
Redirection Attacks
Another way to capture Facebook credentials is to clone the Facebook login page using Ghost Phisher. Ghost Phisher will clone whichever Web site attackers choose, such as the Facebook login page. This will take some configuring to use Ghost Phisher, but it’s nothing a hacker can’t do.
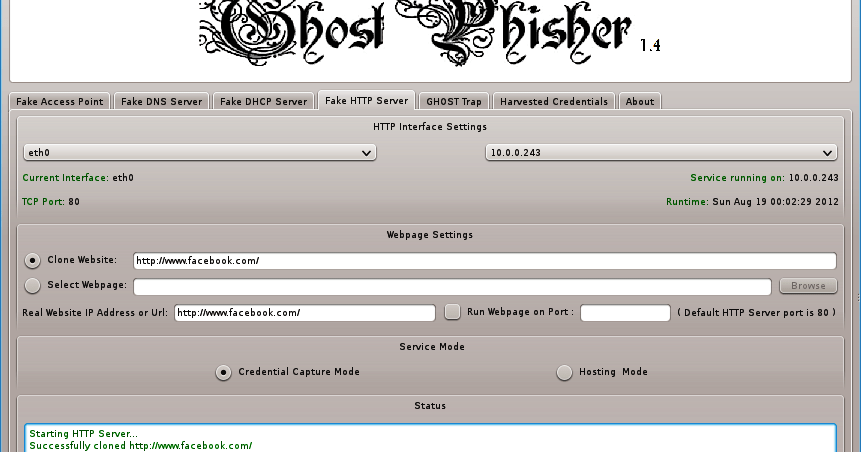
Hackers can send the malicious link to the victim, but will really only work if the hacker and the victim are on the same network. If the victim enters their Facebook credentials, they will show up in Ghost Phisher’s “Harvested Credentials” tab.
Malware
Malware, particularly spyware, has the ability to log credentials entered by the victim and report them to a command-and-control (C2 server) managed by the malware author.
Spyware is typically delivered via Trojan horse programs, which as the name implies, are disguised to look like a legitimate or useful program. In the background, however, is a malicious payload.
Brute Force
And finally, hackers can just brute force the password (if they know your email and no dual-factor authentication is enabled). This can’t be an automated process because Facebook has a lockout policy. Too many failed login attempts in a short period of time will lock out the account. But, if your password is easy to guess, it’s possible.
Protecting Yourself
There are many other ways hackers can access your Facebook account, but I can discuss this in a later post. What sucks is that no matter how long or complex your Facebook password is, it won’t protect your from the attacks described above (expect the brute force option).
So, as always, be careful about what you do on open wireless networks. They are, in essence, playgrounds for hackers. Consider using your cellular network if you’re away from home. If you have to connect to WiFi, keep an eye on the URL bar and make sure that it reads “https.” You want to make sure that your https connections are not being downgraded to http with sslstrip. If you can avoid it at all, it’s preferable not to enter your credentials on WiFi you can’t trust.
Phishing e-mails can sometimes be tricky to spot, but if you’re pretty knowledgeable in security, you’ll be able to spot a bogus email from a real one. Take a look at the source and come to a conclusion if it’s legitimate or not. Additionally, phishing emails can be bland, so that’s something to identity if you receive a suspicious e-mail. Another thing to watch for are any typos. Official e-mails from Facebook are not going to contain any typos. A lot of email services have spam filters, so you already at least inherit some form of protection.
If you’re not running anti-virus software, that’s a shame. It could protect you from all those harmful files you download from shady sites.
Overall, cybersecurity professionals believe that your “awareness” is what will prevent these attacks. By learning how a hacker thinks, you can offer yourself better protection.
Aguilar, N. (2017). 4 Ways to Crack a Facebook Password and How to Protect Yourself From Them. Wonder How to, Inc. Retrieved from https://null-byte.wonderhowto.com/how-to/4-ways-crack-facebook-password-protect-yourself-from-them-0139532/

