Identifying Logical Ports
There are two types of ports: physical and logical ports. Physical ports are the RJ-45 female jacks that are attached to a switch, router, firewall, server, patch panel, or Ethernet outlet. I’ve provided some examples below.
The ports I’m talking about, however, are logical ports.
Understanding Logical Ports
In computer science, a logical port is a number assigned to a “logical” connection. In simpler terms, it is the endpoint to a logical connection that describes a service in TCP/IP and UDP. There are 65,536 TCP ports and 65,536 UDP ports. We count from 0 to 65,536. By including TCP/UDP port 0, the total number becomes 65,536 ports. Port numbers are assigned to a service, which is helpful to TCP/IP in identifying what ports it must send traffic to. For example, TCP port 80 handles http, which is unencrypted Web traffic. Therefore, when ever TCP/IP is handling communication between a client and a Web server, it will be using TCP port 80 (or TCP port 443 for https). The Internet Assigned Number Authority (IANA) maintains a list of official port assignments and divides these ports into 3 ranges:
Well-Known Ports (0-1023)
If you are going for the Network+ or Security+ CompTIA exams, these ports are a must to know. The port numbers in the “well-known” port range are assigned to commonly used protocols or services from ports 0 to 1023. This port range also gets its own nickname, which is “non-ephemeral ports.” The word ephemeral means temporary. By being non-ephemeral, the well-known ports are permanent. The port numbers you will need to know for the exam are displayed below, some of which are a part of the Registered port range, which I’ll discuss next.
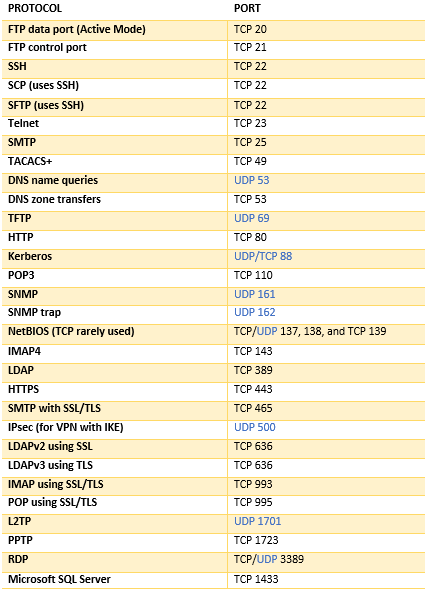
Registered Ports (1024 – 49,151)
The “Registered” port range includes port numbers 1024 through 49,151. IANA has assigned these ports for the convenience of IT companies who wish to register one of these logical ports for a proprietary application. For example, Microsoft SQL server (the last row in the table above), uses TCP port 1433.
Dynamic / Private Ports (49,152 – 65,535)
The last logical port range is called the “Dynamic” or “Private” port range. This covers the remaining logical ports from 49,152 to 65,635. These ports are available to any application. This port range also has a nickname called “Client ports.” This is because when you make a connection with a Web server, your Web browser is making a connection to the Web server over TCP port 80 or 443. Since you’re requesting a Web page from a Web site, your system will search for an unused client-side port on your system from ports 49,152 to 65,535. When it finds an unused port, it will use this port to handle the return traffic. This will be the destination port that the Web server will use to send the web page information to your system. Once you exit your Web browser or close the tab, the client port is free again. This gives the dynamic and private port range ANOTHER nick name called the “ephemeral port range” since the port usage is short-lived.
Logical Port Security
All logical ports are subject to attack, but it’s the well-known port ranges that receive the brunt of the attention from hackers. Hackers use port scanners and vulnerability scanners to identify open ports on servers. By revealing which ports are open, the hacker can identify what kind of services are running and the type of system. For example, if TCP ports 80 and 443 are open, that would indicate that http and https is running. This would be a Web server. If TCP port 20 is open, that would indicate that the FTP service is running, which probably tells us it’s a file server. FTP is unencrypted and hackers can use this to their advantage. Hackers try to find vulnerabilities in these services that they can exploit.
One of the things network and security administrators do is they close unnecessary ports on their servers and other systems. For instance, if you’re running a Web server, the only ports that really should be exposed are TCP ports 80 and 443 (http and https, respectively). It would not make sense to have another port open on a Web server as this is pointless and also increases the attack vector. By leaving a bunch of unused ports open on your systems, hackers can look for ways to exploit them.
Besides closing unnecessary ports, we can also use security devices that filter network traffic. One good example is a firewall. Using our example above, we can put a firewall in between our Web server and the Internet. In our firewall policy, we can create rules that allow http and https traffic on TCP ports 80 and 443, but deny all other traffic from other ports. In some cases, firewalls can prevent hackers from successfully port scanning our Web server too.
References
Gibson, D. (2017). CompTIA SECURITY+ Get Certified Get Ahead SY0401 Study Guide. Virginia Beach, VA: YCDA, LLC




Excellent Article!! Keep It up!!!
LikeLike