Let’s assume you have the architecture of your network already established, but you’d like to able to detect any signs of malicious traffic traversing in and out of your network. One of the things your might want to consider is placing sensors in strategic locations of your network.
Intrusion Detection Systems (IDSs) and Intrusion Prevention Systems (IPSs) are great security systems to recruit for network protection. They can be signature-based, anomaly-based, or heuristics-based. Which flavor you choose depends on your preference, patience, and overall security profile, but most organizations prefer the signature-based approach. Though it requires frequent updating, the signature-based method is less of a challenge to set up and offers a lower false positive rate than the other methods of detection. An IDS or IPS can also be network-based, host-based, or wireless. And, on top of that, some of these systems combine IDS and IPS functionality, making it an IDPS. Therefore, you have to think about what IDS/IPS product you want and how your going to design the architecture (e.g, where sensors or agents are placed, management servers, redundancy, which systems the IDS/IPS needs to interface, accommodations, and the rule sets you wish to configure). This is all something I’ll cover in a later post.

Staying Vigilant. Reprinted from “Ethical Hacker,” by Kennesaw State University, 2018
A “SIEM,” or “Security Information and Event Manager,” might also be something you might want to have. SIEMs centralize logging, making it a lot easier to analyze logs for suspicious activity. Many network devices can use “syslog” as their standard logging format. The SIEM itself is a centralized logging receiver that receives all the logs of your network devices (e.g., firewalls, routers, switches, servers), packages them in syslog format, and stores them for you real-time alerts and future analysis. Obviously, you can’t analyze all these logs by yourself, so the SIEM does this for you by searching for security events, important information, and network metrics of interest. From there, you can make important security decisions, detect malicious activity, identify correlations, or use these logs in a forensic investigation or Incident Response (IR). The downside, however, is you’ll need a lot of storage for this level of log aggregation.
In addition, we have all these nifty tools in our “tool box” that we can use to find the bad guy. We have packet sniffers, protocol analyzers, vulnerability scanners, port scanners, interface monitors, Wi-Fi analyzers, application scanners, built-in utilities, and other types of software that we can use to help us identify network-related symptoms of something bad. So, how do we put it all together?
Use your IDS/IPS to Monitor Malicious Activities
An IDS/IPS possesses a lot of information gathering capabilities, so pay attention to what capabilities your product can provide for you. A good IDS/IPS should be able to identify all the hosts on your network by hostname, IP address, and MAC address; that way, when an unauthorized device connects to your network, you’ll be promptly alerted. Some IDS/IPS will even identify the applications in use on your network. Through application whitelisting, and the proper configuration of your IDS/IPS, you can be alerted when vulnerable or unauthorized applications are in use on your network.
Another neat capability about an IDS/IPS is its ability to detect unauthorized network configuration changes. By keeping track of the hop count between devices, an IDS/IPS can detect when a device has been re-configured or moved on the network. The awesome power of an IDS/IPS is in their extensive logging capabilities, including organizational details, such as timestamps, session IDs, layer 3/4/7 protocols, source/destination IP addresses, source/destination port numbers, the number of bytes transmitted, and state-related information. They even provide you with an alert type, rating (e.g., priority, severity, impact, and confidence), and any prevention action performed.

Various Alerts generated by an IDS/IPS. Reprinted from “En/3.5/Intrusion Prevention System (IDS IPS),” by Zentyal Wiki, 2014.
As for detecting suspicious network activity, an IDS/IPS can detect application layer reconnaissance and attacks, such as banner grabbing, buffer overflows, injection attacks, brute force attacks, malware, and so forth. An IDS/IPS is monitoring multiple TCP/IP protocols and applications as well. At layer 4, they will detect any types of authorized or unauthorized port scanning. At layer 3, they will detect IP address spoofing, IP header manipulation, and ICMP error codes.
In some IDS/IPS, they will alert to unauthorized application services or any security policy violations pertaining to forbidden Web site visits, tunneled protocols, and much more. Ultimately, it comes down to the IDS/IPS administrator to specify what characteristics of activity should not be permitted and what to alert to. Fortunately, since there are many thing to be on guard for, most of these IDS/IPS already come with a rich set of rules that you can apply. And, of course, you can craft your own rules as you see fit! IDS/IPS rules are much more robust than firewall rules.
An IDS/IPS may take some tuning and customization, but they are definitely worth the management. Keep in mind, however, that an IDS/IPS does have its limitations. Be aware that an IDS/IPS will not detect attacks within encrypted traffic. Also, keep in mind that though an IDS/IPS is there to detect and prevent attacks, they are not immune to attacks themselves. For example, an IDS can detect a DoS attack, but the sensor (whether a dedicated hardware appliance or software installed on a network node) can fall prey to a DoS attack too.
Monitor Bandwidth Utilization
A spike in bandwidth on our network might be something normal, but in order to determine what’s normal, you need to either look at your initial baselines or identify the source of the spike and determine if this is acceptable behavior. For instance, a workstation used by a graphics developer who consistently does frequent uploading to a server might cause some spikes in bandwidth. Similarly, one department in your organization might frequently do video streaming, which would also take up valuable bandwidth. This is normal.
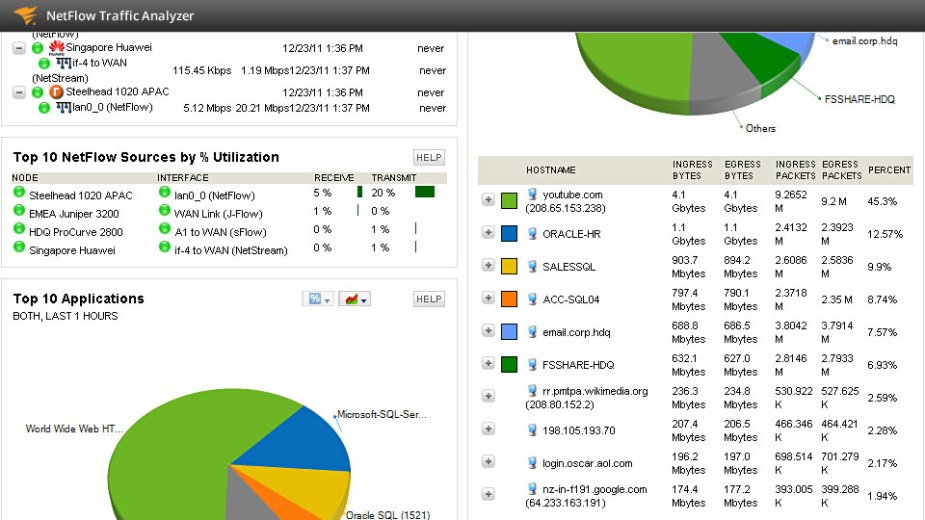
NetFlow Traffic Analyzer, reprinted from “Top 5 Recommended Packet Sniffers,” by Network Management Software, 2018
In cases of suspicious bandwidth consumption, NetFlow and Cacti are your best friend. Cisco routers and switches incorporate NetFlow, and they essentially perform packet flow monitoring. Analyzing the flow of data on your network allows you to build a clear picture of the volume and flow of traffic traversing your network. Besides Cisco, there are other flow monitoring products that provide a GUI, charts, graphs, and visual representations of the packet flow on your network. Graphing programs, like “Cacti,” not only helps with giving you a display of bandwidth utilization, but also CPU and memory usage as well.

Bandwidth spikes can sometimes be caused by something suspicious, such as a compromised workstation infected with malware. As we know, an infected computer tries to engage in lateral movement. Malware will attempt to communicate out to a C2 node and other systems on the network. The point is that a compromised system typically exhibits the symptoms of a “top-talker,” meaning they send out a lot of data. That would be something NetFlow can identify for you.
Beaconing
Speaking of malware, most malicious code is going to try to communicate with a “Command-and-Control (C2)” node through a process called “beaconing.” Many strains of malware follow a predictable, periodic form of beaconing. However, detecting these beacons isn’t easy as these connections are usually brief and can be difficult to identify.

Netstat displays remote malware connection. Reprinted from “Detect and Kill All Remote Connecting Malware using CMD,” by Bhai, N., 2016.
But, on the specific infected system, you can search through the traffic logs to identify the beacon. You can also type the netstat -an command and identify any established or listening connections that look suspicious or unknown to you. This requires research on your part.
Log Monitoring and Analysis
Logging is absolutely useless if you’re not going analyze them. You might have a system being repeatedly brute forced, but if you’re checking your security logs a month later, you’ll be in for a nasty surprise when you see 30 failed login attempts followed by a successful login. Log analysis can be a pain, but there are numerous log analysis tools that make it simple and automatic. As I already addressed earlier, a SIEM is a system of centralized logging. It provides log aggregation from any device for long-time storage. As an added bonus, a SIEM provides advanced reporting features, such as security events, important events, alerts, and trends.

Sherlock Inspection. Reprinted from “he Best Mechanical Keyboards — and Why People LOVE them!,” by Keyboards Guide, 2018.
Some of the things a SIEM can do for you is report suspicious network activity, such as failed login attempts, failed user account validations, access objects, user account changes, user groups changes, and more (all of which could be an indication of something more nefarious).
Rogue Device Detection
Unauthorized connections are a problem. The unauthorized physical connection to a wired network isn’t very common because most of our switches are in a locked closet and we’re implementing some form of switch security or enterprise-level port-based network access control (IEEE 802.1X).
Unauthorized wireless connections, however, are a different story since our wireless networks don’t have the equivalent protections of our wired networks. An attacker doesn’t even have to be in the building or even in the parking lot to connect to your wireless network. Attackers can use high-gain antennas from even a mile away to connect to your wireless network.
As I mentioned before, an IDS would certainly alert to a rogue device since it keeps a list of authorized hosts on your network. But, if you don’t have an IDS, you should be implementing some form of Network Access Control (NAC) to ensure every device wishing to connect to your wireless network is properly authenticated, scanned, and joined to the appropriate network. Cisco’s “Network Admission Control (NAC)” and “posture assessment” would be a viable option. Any unauthorized device that fails to connect to the wireless network will be logged for your review.
Additionally, the aforementioned solutions will detect rogue APs as well. A rogue AP is an unauthorized “Access Point (AP)” in which unsuspecting wireless clients can connect. They may be innocent APs set up by employees or malicious APs set up by attackers for MitM attacks. Additionally, if you are using LWAP-to-WLC communication to manage all your APs, then the wireless LAN controller will detect a rogue AP connecting to your wireless network. From there, you may manually or automatically contain this security event.
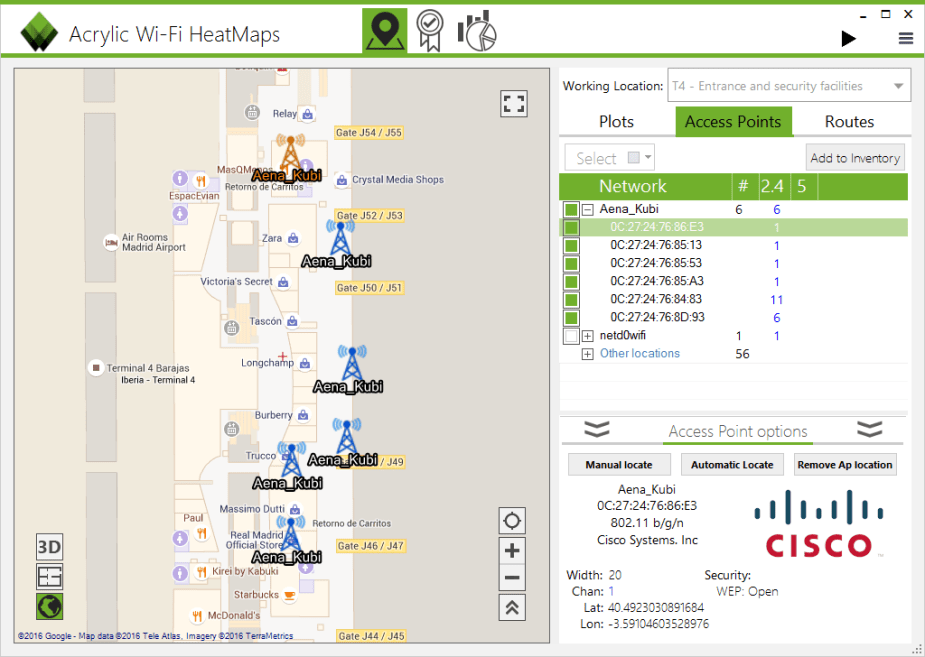
Acrylic Wi-Fi heat map displaying APs. Reprinted from “How to Locate an AP,” by Tarlogic Research, 2015.
Conducting routine “site surveys” of your wireless network will certainly allow you to remain vigilant of rogue devices that shouldn’t be there. Use a good Wi-Fi analyzer to locate any unknown sources of radio frequency emanating on your wireless network. You may detect something worth further investigation.
Detect Scan Sweeps
As a method of active reconnaissance, hackers may perform port scans of your environment in order to map out the network and identify any systems and running services to exploit. On Wireshark, the simpler scans will be pretty obvious. You’ll see a lot of traffic being generated from one source and making hundreds of ARP requests.
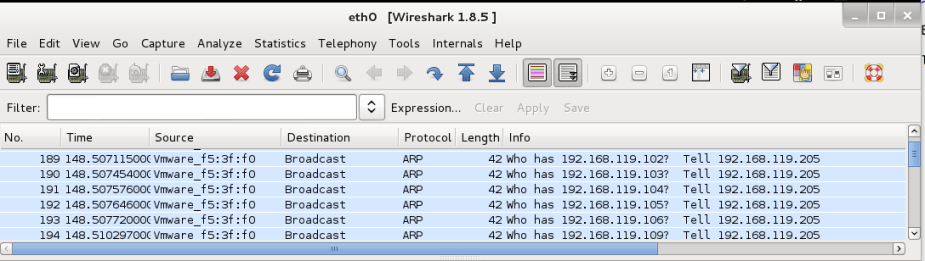
Detecting other scans will require an attention to detail, but your sensors should be able to detect these types of scans. Snort IDS, for example, can examine packets for missing flags. In a TCP SYN Stealth scan, the attacking machine does not send the last ACK packet. A Snort IDS rule, such as Alert tcp 192.168.1.5 any -> 192.168.10.2 any (msg: “SYN flood”; flags:A!; sid:002;) will alert any missing ACK flags in a TCP three-way handshake.
Investigate

Might be something suspicious…
Walk around and look for anything suspicious. If you see someone in the lobby running some sort of dishonest-looking software on their laptop, then ask who they are and what they’re doing! Just being aware could save you from wasting a lot of time and resources with an incident response.
References
Maymi, F. J., Chapman, B. (2018). All-in-One CompTIA CSyA+ Cybersecurity Analyst Certification Exam Guide CS0-001. McGraw-Hill Education: New York, NY.
Meyers, M. (2015). All-in-One CompTIA Network+ Certification Exam Guide N10-006. McGraw-Hill Education: New York, NY.