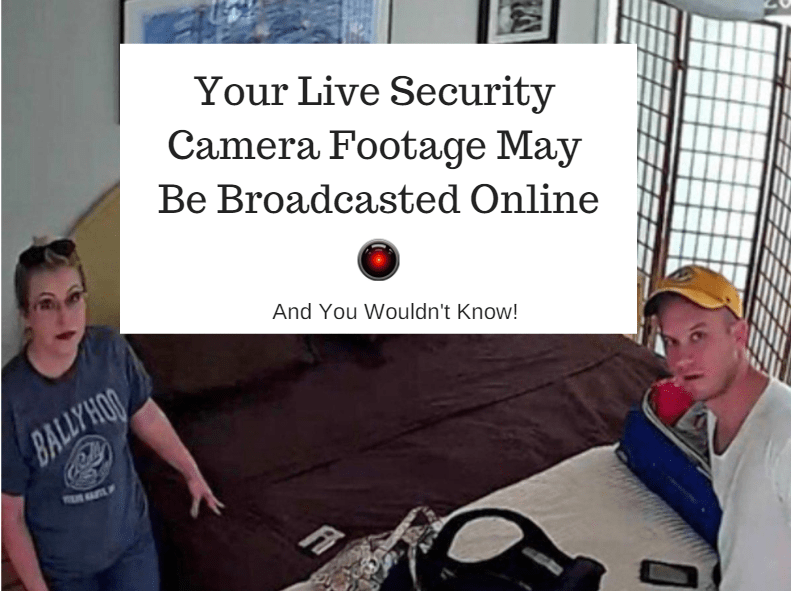
Live video feeds of home and commercial surveillance cameras around the globe are being broadcasted live and without permission on a site called Insecam, which is believed to have originated from Russia. Other sites like Shodan and Nestcamdirectory also provide visitors with the ability to look up IP cameras; however, Insecam aggregates these live video streams all into one central, but creepy place. Webcams are also fair game, leaving millions of concerned laptop owners to cover their camera lens.
Your networked cameras, which may be monitoring bedrooms, bathrooms, family rooms, pool areas, office areas, backyards, front yards, parking garages, hallways, school buildings, busy streets, convenience stores, barber shops, and anything in between could currently be hosted on Insecam. And the worst part is that most of these camera owners have no idea. Right now, Insecam is hosting 5,232 live video feeds in the U.S. alone.
I was in Downtown Alexandria, VA, over the weekend. While I was eating at a local ice cream shop, I pulled up Insecam to see if there were any cameras being broadcasted in my area. It turns out there was a camera just a block down the street from my location. I checked for myself and was able to confirm that the camera was indeed there. I thought about notifying the owner, but couldn’t figure out which building it belonged to.
A barber in Tasmania. Reprinted from “Live security camera footage of private moments stokes privacy fears,” by Mitchelson, A., 2018.
Insecam received a considerable amount of unwanted attention back in 2014 in which popular news and blog sites published reports that a “creepy” site was broadcasting live camera streams from over 73,000 private security cameras around the world. At that time, many of the live streams had “coincidentally” stopped working, but as of April 2018, it doesn’t appear that Insecam has impeded its shady surveillance tactics.
How is Insecam accessing these private cameras? In one way or another, the cameras are connected to the Internet via publicly accessible IP addresses and ports. This means that anybody can “access” the camera if they can bypass its security implementations (e.g., firewall, authentication, or if it has security at all). Remarkably, all of the camera feeds being broadcasted on Insecam still have their default password configuration in place. In many cases, the password is just “admin,” “1234,” “root,” or “pass.”

A skate park in south-east Melbourne. Reprinted from “Live security camera footage of private moments stokes privacy fears,” by Mitchelson, A., 2018.
Sometimes, there isn’t even a password at all! This allows Insecam to access the camera and broadcast the live feed for its thousands of visitors, which highlights the importance of changing default passwords. Typing in the IP address of the camera into the URL bar will display the web console for the camera. For the most part, there will usually be some sort of clue of who the manufacturer is for the camera. Web sites, such as A1securitycameras publish the default usernames and passwords of popular brand security cameras, like Sony, Samsung, Vivotek, LTS Security, and more.
If you can recall back to my post about how refrigerators are being hacked, I believe this all stems from the rise in the Internet of Things (IoT) devices. When we connect ordinary objects and appliances, such as door locks, light bulbs, refrigerators, thermostats, and wrist watches to a network, we are extending its connectivity capabilities by giving it an IP address. Many of these devices are not built with security in mind, which is why cybersecurity specialists are predicting an uptick in the amount of IoT device hackings for the foreseeable future.

A WHOIS search on Insecam’s domain name doesn’t reveal much. It does appear to be a domain registered on GoDaddy, but the registration was made private. GoDaddy is a domain registrar that offers registrants the ability to keep their information confidential if they choose to purchase a private registration option, otherwise their name and contact information will be publicly displayed. GoDaddy denies any responsibility for insecam as its content is hosted on a different web hosting provider.
Is it legal? As mentioned on its FAQ page, Insecam states that “these cameras are not hacked. All cameras listed on the site do not have any password protection.”
Umm…what?
Is Insecam implying that, because these cameras aren’t password protected, they are allowed to access these video streams? I’ll put this into perspective: If your front door doesn’t have a lock, can I walk in? Of course not. Accessing these cameras must in some way violate the U.S. Computer Fraud and Abuse Act (CFAA). I guess the problem with prosecution is that the owner of Insecam is unknown and is most likely somewhere in Russia.
The good news is that if you don’t want your camera feed broadcasted for the world to see, all you have to do is change your password. But even if your camera is password-protected, behind a firewall, and has its own private IP address, all an attacker has to do is crack your network password. That’s not easy unless your password sucks. Then, they can just brute force your camera. Most modern systems would never allow this to happen; however, with IoT on the rise, manufacturers don’t seem to care about a lockout policy.
References
Law, J. (2014). Insecam exposes live feeds of surveillance cameras. News Limited. Retrieved from http://www.news.com.au/technology/online/hacking/insecam-exposes-live-feeds-of-surveillance-cameras/news-story/4fec72d1c1d53fffd79e5d7a2b47b27c
Kirk, J. (2014). Governments hit back against webcam-snooping websites. IDG Communications, Inc. Retrieved from https://www.computerworld.com/article/2850954/governments-hit-back-against-webcam-snooping-websites.html
Mitchelson, A. (2018). Live security camera footage of private moments stokes privacy fears. The New Daily. Retrieved from https://thenewdaily.com.au/life/tech/2018/01/19/security-camera-privacy-insecam/

[…] you’re keeping up with IoT security concerns, or even some of my own posts on IoT hacking, you won’t be surprised by this next piece of news. A mother in South Carolina claims that […]
LikeLiked by 1 person