MikroTik is a Latvian company which was founded in 1996 to develop routers and wireless ISP systems. The company is predominantly known for its RouterOS software system. With distributors located all around the world, including the United States, MikroTik should sound fairly familiar even though this is primarily a Cisco-dominant networking world.

In July, researchers at Trustwave discovered that over 70,000 MikroTik routers in Brazil had been infected with CoinHive cryptojacking malware. Cryptocurrency miners usually inject CoinHive computer code onto websites using JavaScript; however, this mass infection in particular affects MickroTik routers only. An important clue for consideration was that the infected routers were all using the same CoinHive sitekey, which would indicate that these devices were all infected from one source.
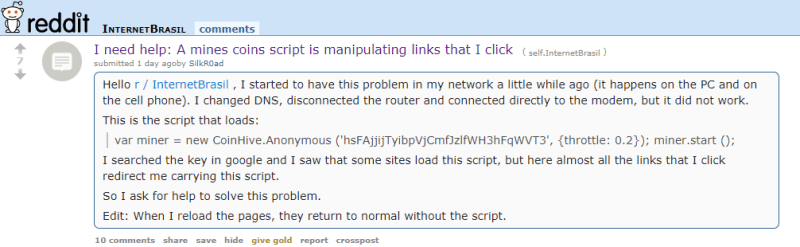
Such a massive and unknown infection would be indicative of a zero-day exploit. Trustwave researchers took to the Internet to find some clues on what exactly was going on with these MikroTik routers in Brazil. A Reddit user complaining about his MikroTik router provided an additional clue.
Reprinted from, “Mass MikroTik Router Infection – First we cryptojack Brazil, then we take the World?,” by Kenin, S., 2018.
In the Reddit post cited above, the user complains that for every webpage he visits, a CoinHive script is loaded with the same sitekey mentioned just a moment ago. Manually changing the DNS settings or reloading the router does not provide any solution.

Reprinted from, “Mass MikroTik Router Infection – First we cryptojack Brazil, then we take the World?,” by Kenin, S., 2018.
The next clue came from a Twitter user who Tweeted that the MikroTik router exploit was actually not a zero day, but rather an exploit for a vulnerability that had a patch developed for it back in April. The vulnerability was assigned CVE identifier CVE-2018-14847. This vulnerability affects Winbox for MikroTik RouterOS through 6.42, which allows remote attackers to bypass authentication and read arbitrary files by modifying a request to change one byte related to a Session ID.

Reprinted from, “Mass MikroTik Router Infection – First we cryptojack Brazil, then we take the World?,” by Kenin, S., 2018.
The attacker uses a script that specifically affects MikroTik routers to modify system settings, enables the RouterOS HTTP proxy, and creates a backdoor into the device. A script redirects all the HTTP proxy requests to a local HTTP 403 error page, which contains the CoinHive minining code. This code is injected into every html page. Of particular importance is that the researchers noticed that the script is continually changing and, at the time of examination, the researchers noticed that other geo-locations are being affected. This suggests that the attacker is moving to a global scale, and that’s exactly what happened.
Not too long ago, Troy Mursch, a cryptojacking researcher, located tens of thousands of new MikroTik router infections all using the same CoinHive site key, but primarily in Moldova, which is an Eastern European country.
But this week, Qihoo 360 Netlab researchers found an additional 7,500 infected MikroTik routers. However, this time, the routers were compromised to allow attackers to eavesdrop on network traffic. The vulnerability being exploited uses the same Winbox vulnerability in addition to a remote code execution vulnerability that exploits Webfig. Both Winbox and Webfig are RouterOS management components that use TCP ports 8291, 80, and 8080.
Despite their already being a patch for CVE-2018-1487, there are 370,000 out of 1.2 million MikroTik routers that are still vulnerable. The malware that is affecting MikroTik routers specifically exploits this vulnerability, and seeing that there is already a patch created to address this vulnerability, the obvious solution is to patch.
The newly found, infected MikroTik routers have Socks4 proxy enabled, which allows the victim’s traffic to be forwarded to IPs controlled by unknown attackers. Netlab researchers have confirmed a total of 239,000 IP addresses to have Socks4 proxy enabled.

Reprinted from, “7,500+ MikroTik Routers Are Forwarding Owners’ Traffic to the Attackers, How is Yours?,” by Network Security Research Lab, 2018.
Because MickroTik routers allow users to capture packets on the router and forward the captured network traffic to a specified server, the attackers are forwarding this captured traffic to IP addresses under their control. Only 7,500 MicroTik routers were discovered to have their network traffic being actively eavesdropped. Aside from port 80 (HTTP) and port 53 (DNS), the attackers are also interested in FTP, SMTP, POP3, and IMAP traffic.

Reprinted from, “7,500+ MikroTik Routers Are Forwarding Owners’ Traffic to the Attackers, How is Yours?,” by Network Security Research Lab, 2018.
MikroTik routers in Russia and Brazil are currently the most affected, but there are still thousands of other infected routers in other locations around the globe, inluding Indonesia, Iran, Italy, Poland, and the United States. The obvious remedy here is to patch MikroTik routers. Users should also verify whether or not http proxy, Socks4 proxy, and the network traffic capture function is being maliciously exploited by attackers. Researchers do not know who the attacker(s) is, but it’s certainly clear that they hold very discernible knowledge in the RouterOS software system.
References
Kenin, S. (2018). Mass MikroTik Router Infection – First we cryptojack Brazil, then we take the World? Trustwave Holdings, Inc. Retrieved from https://www.trustwave.com/Resources/SpiderLabs-Blog/Mass-MikroTik-Router-Infection-%E2%80%93-First-we-cryptojack-Brazil,-then-we-take-the-World-/
Khandelwal, S. (2018). Thousands of MikroTik Routers Hacked to Eavesdrop On Network Traffic. The Hacker News. Retrieved from https://thehackernews.com/2018/09/mikrotik-router-hacking.html
Network Security Research Lab. (2018). 7,500+ MikroTik Routers Are Forwarding Owners’ Traffic to the Attackers, How is Yours? Retrieved from http://blog.netlab.360.com/7500-mikrotik-routers-are-forwarding-owners-traffic-to-the-attackers-how-is-yours-en/


If someone suddenly turns up with massive amounts of bitcoin seemingly out of nowhere, that’s probably your guy.
LikeLike