Security researchers have discovered a new attack that exploits our Wi-Fi networks, both at home and in enterprise environments.
Most of our home networks are using one of the IEEE 802.11 wireless network protocols, such as 802.11b, 802.11g, 802.11n, or perhaps, 802.11ac. Our home Wi-Fi networks can likely support several 802.11 protocols; however, it is not the wireless network protocol that was recently exploited. Rather, it is the WPA2 authentication scheme we use to authenticate to our Wi-Fi.
Most of us are using WPA2 as our encryption scheme for our home Wi-Fi. Or, at least, you SHOULD be as it is our most secure form of wireless authentication. A few weeks ago, a serious vulnerability was discovered in the way WPA2 works, which allow KRACK attacks (Key Re-installation Attacks) to exploit this vulnerability.
With KRACK attacks, hackers can decrypt your network traffic, steal your usernames and passwords to your social media accounts, bank accounts, and other accounts, and much more.
Note to Non-Technical People:
If you don’t want to read about how the KRACK attack technically works, or you feel that you will not understand, then this section is for you.
When you connect to your wireless router or Access Point (AP) on your home network, WPA2 uses a 4-way handshake between your device and the AP. KRACK attacks exploit the third step in the 4-way handshake by tricking you into re-installing encryption keys. When we constantly re-use these keys, it also degrades them and makes them predictable. This allows the attacker to decrypt your data. Any Web sites you go to may allow the attacker to discover your usernames and passwords to your social media accounts, your bank accounts, and other accounts. And this is true even for Web sites that regularly use HTTPS encryption. Attackers can also plant malware on the Web sites you regularly visit in hopes of infecting your device.
KRACK attacks do NOT discover your Wi-Fi passphrase; therefore, changing your passphrase to something more complex will not save you. Also, as it turns out, Android and Linux devices are the most susceptible to KRACK attacks.
Skip to the “How to Protect Your Home Wi-Fi from KRACK Attacks” section at the very end of this post to see how you can better protect yourself.
That’s all for non-technical people :).
A Quick History Lesson:
Back in 1999, we came out with 802.11a. It had a 54Mbps maximum data transfer rate, good channel bandwidth, but limited range. So, that same year, we also came out with 802.11b and it was the first wireless specification to earn the Wi-Fi “seal of approval.” But, we could do better. 2003 saw the creation of 802.11g, which was very similar to 802.11b, but it offered a higher maximum data transfer rate. In 2009, 802.11n was created as a more significant improvement and used MIMO technology. Its maximum data transfer rate was as high as 600Mbps and its range extended 230ft (indoors). The last wireless network protocol we mainly use is 802.11ac, and its the newest and fastest IEEE standard in terms of its throughput (1.3Gbps). Most of our home Wi-Fi networks are supporting 802.11b/g/n and sometimes ac. This will depend on your wireless network adapter and AP. I’ve put together a helpful chart that summarizes each 802.11 standard below:

The Wireless Authentication Schemes:
We needed a way to authenticate to these 802.11 networks, so we created several different wireless authentication schemes since the past several decades.
Wired Equivalent Protocol (WEP):
WEP was created back in 1999. I won’t go into any detail about how WEP works in this post, but the important thing to remember is that WEP is no longer secure. In 2001, WEP was exposed by a serious vulnerability involving the reuse of keys since the Initialization Vectors (IVs) were too small; each were 24-bits in length.
WiFi Protected Access (WPA):
WPA was developed quickly in 2001 to replace WEP because we needed an authentication scheme to temporarily cover us as we developed a more securer version. WPA has two basic modes, which are WPA-PSK and WPA-Enterprise. I wont dive into WPA-Enterprise because this is a mode used for enterprise networks. WPA-PSK, however, stands for “WPA-Pre-Shared Key.” It’s also known as WPA-Personal, since we use it on our personal, home Wi-Fi networks. WPA used Rivest Cipher 4 (RC4) symmetric stream encryption with Temporal Key Integrity Protocol (TKIP). The addition of TKIP made WPA better at managing the encryption keys than WEP. Anyway, I digress. I’m not going to discuss WPA in much detail either because most of our home networks are using WPA2 (or at least it should).
WiFi Protected Access 2 (WPA2):
WPA2 was developed in 2004 as replacement for WPA. It is our most secure wireless authentication standard. We also call it IEEE 802.11i. WPA2 uses stronger cryptography than WEP and WPA. Instead of TKIP and RC4, it uses the Counter Mode with Cipher Block Chaining Message Authentication Code Protocol (CCMP) and it also allows the use of the Advanced Encryption Standard (AES). AES is one of our best encryption algorithms and it creates at least 128-bit keys.
Like WPA, WPA2 uses the same two modes: WPA2-PSK and WPA2-Enterprise (BOTH modes are vulnerable KRACK attacks) All of our home networks are supporting WPA2-PSK and CCMP with AES (at least they should be using WPA2). You should only use WPA when WPA2 is not available.
Before you can understand how WPA2 was cracked, you should first understand how it works.
When you connect a device to your Wi-Fi network using WPA2-PSK, you must enter a password (or a Pre-Shared Key [PSK]) to authenticate. When authenticating clients onto our wireless networks, we often use different terms:
- The Supplicant: This is your device (e.g., you phone, laptop, desktop, tablet, etc.). Your device is running Supplicant software to help you connect to the network
- The AP or Authenticator: This is your Access Point (AP). The AP is likely your wireless router. Your wireless router might double as a your gateway. The AP is responsible for giving Supplicants access to the wireless network.
When you connect your device to your AP, a “Four-Way Handshake” begins. This can be a little tricky to understand, but I’ll discuss and example that uses WPA2 with CCMP and AES.
When you want to connect to your Wi-Fi network, you have to authenticate to
your Access Point (AP). As I said earlier, the “PSK” in WPA2-PSK means “Pre-Shared Key.” This is your Wi-Fi passphrase. Both the Supplicant and the AP know the passphrase, but they wont share it with each other over the network. Instead, they will prove that they both know it by deriving a 256-bit “Pairwise Master Key (PMK)” from the passphrase. So, let’s say for example, you want to connect your laptop (the “Supplicant”) to your Wi-Fi. The Supplicant must therefore authenticate with the AP in a 4-way handshake process:
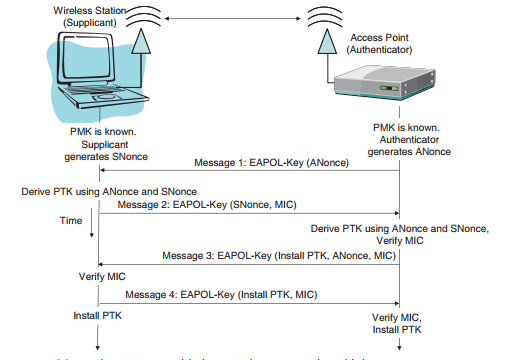
- AP sends an ANonce to the supplicant. An ANonce stands for
“Authenticator Number used Once” and it’s just a pseudo-random
number. There is no hash or encryption of this first message. - The Supplicant receives the ANonce and creates its own SNonce. This stands
for “Supplicant Number used Once,” and it’s also a pseudo-random number.
The Supplicant now has everything needed to derive a Pairwise Transient Key
(PTK). The PTK is used to create temporal keys and will be used to encrypt all unicast (one-to-one) traffic between the Supplicant and the AP. The PTK varies in length from 128-bits to 512-bits, and is split into the required temporal keys. The key length and number of keys are dependent on the algorithm. For TKIP, the PTK is 512-bits and this is split into 5 temporal keys. For CCMP, the PTK is 384-bits and is split into 3 temporal keys (e.g., the MIC Key, KEK, and KCK). It uses the PMK, the ANonce, its SNonce, the AP’s Mac address, and its own MAC address to derive the PTK. The Supplicant goes ahead and sends its SNonce to the AP along with a Message Integrity Code (MIC) using HMAC-MD5 or another hashing algorithm and the CCMP temporal key called the “MIC key.” Remember, this MIC Key is the temporal key derived from the PTK. The purpose of the MIC is
so the AP can verify the message’s integrity or that nothing has been modified in transit. This is to ensure the data’s integrity. - The AP accepts the SNonce from the Supplicant and can now derive the same PTK as well using the PMK, the SNonce, it’s ANonce, the Supplicant’s MAC address, and its own MAC address. It also verifies the MIC that was sent by the Supplicant. The AP now sends a message back to the Supplicant containing the ANonce, the “Group Temporal Key (GTK)”(encrypted with the PTK), and a MIC value. The GTK is used to encrypt all broadcast/multicast traffic between the AP and client stations. You might be wondering where the GTK even came from. Well, all APs have proprietary software the somehow creates a Group Master Key (GMK). The GMK is used to create the GTK, which is passed over to the Supplicant. The AP also sends a flag confirming the installation of the PTK and also instructs the Supplicant to install the “Key Encryption Key (KEK).” Remember, the KEK is one of the 3 temporal keys derived from the PTK and it’s used to encrypt the contents of key management messages.
- The Supplicant verifies the MIC value sent by the AP, and if everything checks out,
the Supplicant sends a message verifying the installation of the KEK along with another MIC value. From that point on, everything is encrypted.
“KRACK-ING” WPA2 Networks:
KRACK stands for “Key Re-installation Attacks.” Last month, security researchers discovered a major flaw in the way WPA2-PSK works. KRACK exploits a vulnerability in the 4-way handshake described above. KRACK will not steal your Wi-Fi passphrase (recall that the passphrase is not even exchanged between the Supplicant and the AP). Instead, KRACK decrypts your data without the passphrase.
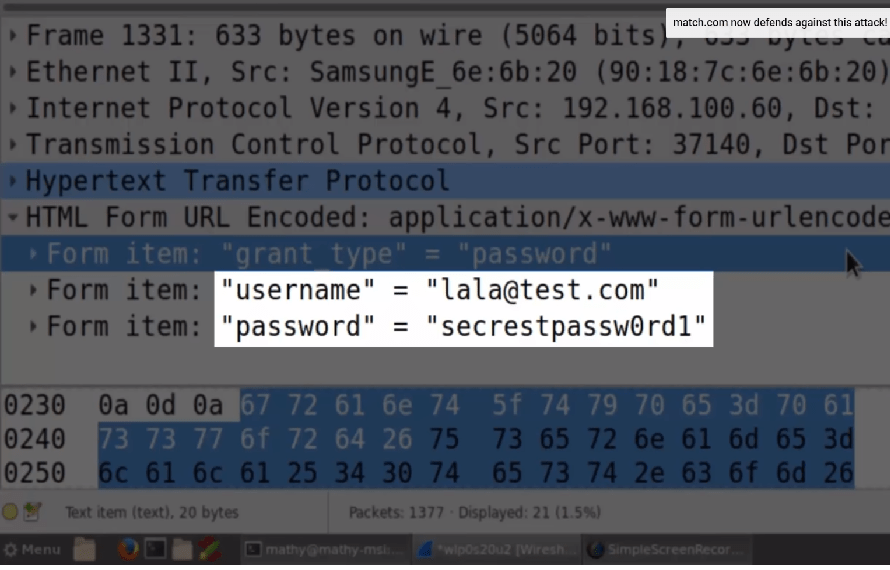
The KRACK attack scans for the wireless network it wants to target. Once the target is identified, it clones the target onto a separate channel. This is called a “Rogue Access Point” or Evil Twin attack. In other words, it creates a malicious clone of the target network. As an added bonus to the attacker, its possible to use the sslstrip tool to attempt to remove the improperly configured SSL/TLS HTTPS protection of encrypted web sites.
Your device, such as your phone, will attempt to connect to your network, but that’s not what the attacker wants. The attacker wants you to connect to his malicious clone network instead. The attacker can easily send spoofed 802.11 management frames to disassociate you from your network and tricks you into connecting to the malicious clone of the target network. Doing so establishes a man-in-the-middle attack for the attacker. This allows the attacker to capture your 4-way handshake and initiate a KRACK attack against this 4-way handshake.
A KRACK attack exploits the third step in the 4-way handshake where encryption keys are negotiated between the Supplicant and the AP, such as the KEK, which protects key management messages. The next step the attacker takes is going to depend on the software running on your device. Windows and iOS are less susceptible to KRACK attacks, but is still 100 percent possible Android devices wither versions >6.0 and Linux devices are the MOST susceptible to KRACK attacks. Right before step 3 begins in the 4-way handshake, if the attacker sends the same forged ANonce sent from the AP to the Supplicant seen in step 1, then the Supplicant can be tricked into re-installing an already-in-use shared key, which also downgrades the key. This can be don multiple times, and makes the key very predictable, which allows the attacker to decrypt your network traffic. Therefore, an usernames and passwords you enter will be discovered in Wireshark by the attacker.
How to Protect Your Home Wi-Fi from KRACK Attacks:
Since the KRACK attack does not actually steal your Wi-Fi passphrase, simply changing your passphrase to something more complex will not work. Attackers do not even need to be connected to your network. As mentioned in the section above, attackers create an Evil Twin, or malicious clone, of your network, which you unknowingly attach to.
Since Android devices are more susceptible to the severe versions of KRACK attacks, people with Android phones should not connect to open Wi-Fi networks.
Make sure you are using WPA2 with CCMP and AES…not TKIP. AES is more secure than TKIP. This does not prevent the attack, but it does prevent the more severe versions of KRACK attacks.
Patch your devices, such as your wireless router, computers, and mobile devices when patches do become available.
Pay attention to the HTTPS “lock” icon in URL bar. Attackers are using sslstrip to stop you from encrypting your network traffic on secure Web sites.
References
Gibson, D. (2017). CompTIA SECURITY+ Get Certified Get Ahead SY0401 Study Guide. Virginia Beach, VA: YCDA, LLC
Vanhoef, M. (2017). Key Reinstallation Attacks: Breaking WPA2 by Forcing Nonce Reuse. Retrieved from https://www.krackattacks.com/


[…] susceptible to the recent Wi-Fi KRACK attacks. You can read more about that in my earlier post, All Wi-Fi Networks are Currently Vulnerable to Attack. Anyway, it seems like almost every other day, The Hacker News is publishing something about the […]
LikeLike
[…] Hypertext Transfer Protocol over SSL (https) is classified as being 100 percent secure. This is because https uses the Secure Sockets Layer (SSL) encryption scheme to pass keys over the Internet. These days, most of our Web servers are utilizing Transport Layer Security (TLS), which is an updated version of SSL. Therefore, we refer to TLS as SSL version 3 (SSLv3). But, SSL is not as safe as we originally thought it was. As we’ve seen with the latest KRACK attacks, it is entirely possible to decrypt a victim’s https traffic. You can read more about KRACK attacks here. […]
LikeLiked by 1 person