Wi-Fi Hot Spots:
Just how easy is it for a hacker to steal your personal information over an open Wi-Fi network? The answer is that it’s painfully simple. Nowadays, we have https, which uses SSL/TLS encryption to encrypt our traffic between our device and the Web server hosting our favorite Web sites. But, not all Web sites are utilizing these encryption solutions to protect you. And, just to be clear, using https does not mean your are 100 percent safe from hackers. There are ways to circumvent this protection.
In case you don’t already know, an open Wi-Fi network is a network that does not use any wireless authentication scheme (e.g., WPA or WPA2). This means there is no password required to access these wireless networks. Although you may be prompted with a captive portal that requires you agree to the organization’s terms and conditions, there is still no authentication mechanism. ANYBODY can access these networks with you, including hackers. Locations that commonly use Wi-Fi hot spots are Starbucks, Cafes, gyms, airports, libraries, restaurants, hotels, and so forth.
I am going to show you how hackers steal passwords on open wireless networks with Wireshark.
Stealing Passwords Using Wireshark:
Wireshark is an opensource tool available to anyone. It’s a protocol analyzer, but it goes by the generic name “sniffer.” In layman’s terms, it “sniffs” the network for packets of information that computers send over the same local network and out onto the Internet.
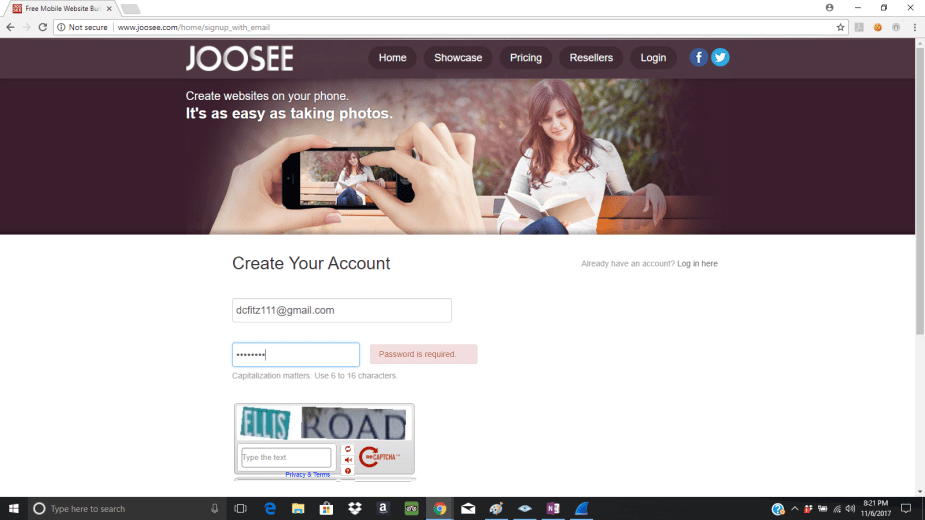
Let’s say Dan goes to Starbucks to quietly work on building his new Web site he’s been creating for work. Dan orders his latte, sits, down, and opens his laptop to connect to the open Wi-Fi network. Before using Starbuck’s free Wi-Fi, he is prompted to agree to the terms and service before he’s granted access.

Dan clicks “accept” and logs on to his Web site builder to begin editing his Web site for work. His login is his email and password.
Little does Dan know, there is a hacker sniffing the open wireless traffic across the room using Wireshark. The hacker has been patiently waiting for an unsuspecting victim to enter an unsecured Web site and enter their credentials.
To the average person, the information being collected on Wireshark will be complete gibberish. But, if you’re a hacker, you’ll know exactly what to look for. The hacker will target Dan’s IP address and filter his http traffic. The hacker knows he has caught something of value when he sees an http POST request in the Wireshark Packet list pane. This indicates that Dan has inserted/submitted “something” to a Web server.
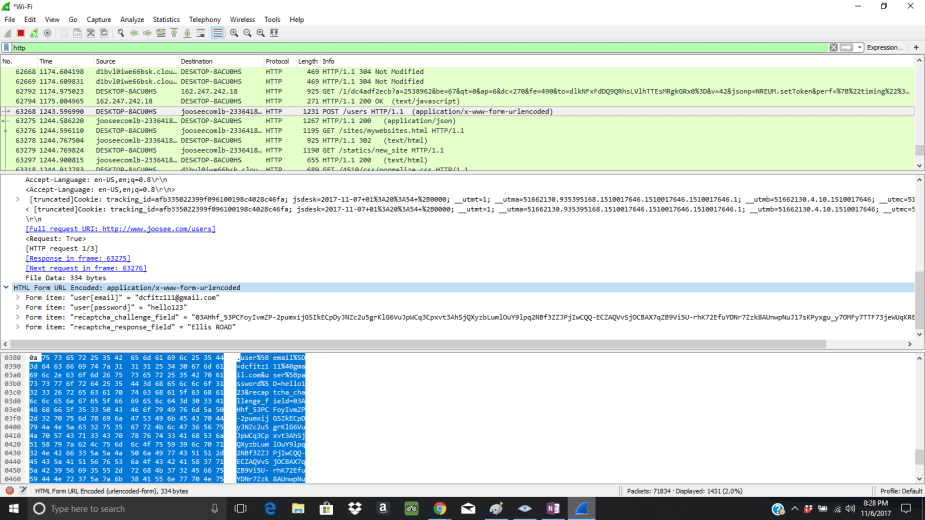
The hacker captures the web traffic communication between Dan’s laptop and his web builder site. Upon closer inspection in the Packet Details pane, the hacker rejoices to find that he has captured Dan’s credentials.
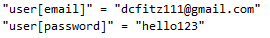
The hacker now knows the username and password to access Dan’s Web site. The hacker now has a few options he can choose from. He can now infiltrate Dan’s Web site and steal or manipulate information. Even worse is that the hacker can now craft phishing emails (even specially crafted ones) to Dan’s gmail account.
And, here’s something pretty interesting that we catch people doing..Often times, people enter the same password for the Web site as their ACTUAL email address password. This is a huge mistake. Any smart hacker will check to see if Dan uses the same password for both the web site builder and his email account. If he did, then the hacker now has access to Dan’s emails in which he can now start the process of accessing his more important accounts, such as his bank accounts, healthcare accounts/portals, alternative email accounts, and social media accounts. All he has to do is reset some passwords and he’s in.

