Malware is the term we’ve assigned to describe all the different classes of malicious code out in the wild. As you’ll see, there are several different classes of malware. One popular type of malware that most people are aware of is a virus. As you’ll come to find, there are actually many different sub-classes of viruses. After reading this, I hope you’ll have a completely new understanding of malware.
Viruses
Viruses are the first class of malware I’ll discuss since they are the most popular in pop-culture. When someone’s computer is acting strange, the first thing that pops in their head is, “I have a virus.”
A virus is a malicious code that attaches itself to a program. Malware writers like to inject malicious code inside of the applications we use, the applications we download off the Internet, the files we download from suspicious emails, and other threat vectors. When the application is executed to run, so does the malicious code. With the virus in memory, it will attempt to replicate and spread to other files/programs on your computer. Therefore, viruses depend on human interaction to spread.
What the virus does depends on the malicious code. We refer to this as the virus’s “payload.” Most payloads will slow your computer and freeze it. Others will be a little more damaging, such as deleting files or frequent and annoying reboots. And some payloads are bit scarier. You might find viruses out there that join your computer to botnets or installs a backdoor into your computer. But, not all payloads are malicious. Some just happen to be minor inconveniences.
As with the different classes of malware, we also have different classes of viruses: boot sector, program, script, macro, multi-partite, and armored.
Boot Sector Virus
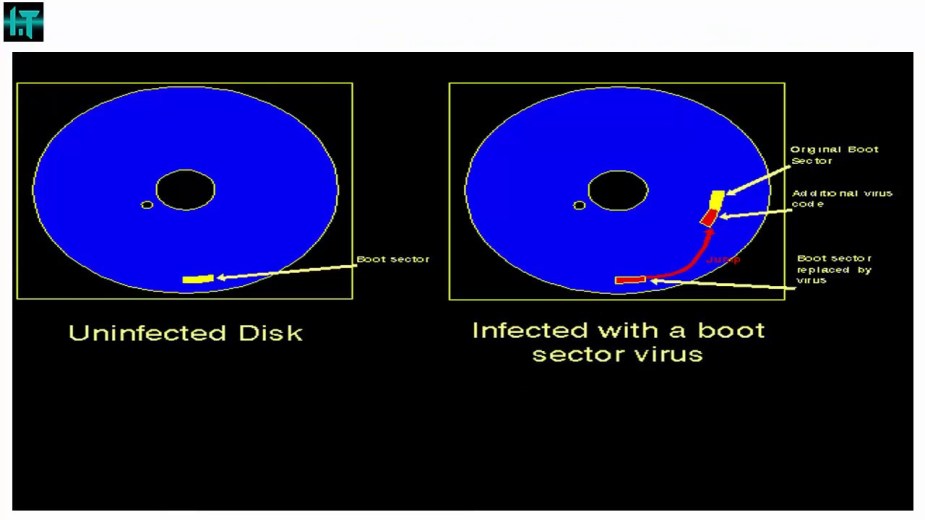
Here’s a virus that’s been around for a long time. As the name implies, this virus sits in the boot sector of your HDD. When your operating system starts up, the virus spreads right into the operating system as well. Boot sector viruses can be a challenge to remove because we most likely aren’t going to have direct access to our boot sector.
Program Virus

This is the virus we most frequently see out in the wild. It’s a virus that’s embedded in programs or applications. For example, some utility applications that we download off the Internet might be infected with a virus like this.
Script Virus

These types of viruses are used in stored XXS attacks and drive-by downloads. With these attacks, an attacker writes malicious Javascript or HTML code in a social network or forum. XXS attacks take advantage of how Javascript or another code communicates with our Web browsers. In some instances, the script can allow access to other parts of your computer that you might not want anyone to have access to. The script virus you see above will infinitely open new tabs in your Web browser, which will freeze your computer.
Macro Virus

The macro virus began to shine when Microsoft Office Suite enabled macro-instructions. For example, if you opened a Word document with malicious macros inside, you might’ve just infected your computer. Fortunately, macros are disabled by default. But, often times, attackers will try to trick you into enabling them. As you can see in the window below, the attacker is attempting to fool his victim into enabling macros.

Would you be fooled?
Multi-Partite Virus

This is a class of virus that utilizes two or more of the classes discussed above. For example, there could be a program virus and a macro virus working in conjunction with each other.
Armored Virus

This is a very nasty virus. Nasty in that it is hard to analyze. Malware analysts study different types of malware by reverse engineering them. Once they find the malicious code, they can analyze it, and then figure out exactly what it does. When they are finished, they can create a “signature” or “definition” for that malware. The signatures are uploaded into a database for our anti-virus and anti-malware software on our computer. When you download a file, your anti-virus software scans the file and inspects it for any known signatures. If it finds a match, it warns you that the file is harmful and either tosses it or quarantines it.
Armored viruses, however, attempt to make reverse engineering difficult for malware analysts. Virus authors will use confusing and complex code in an attempt to mask what the virus actually does. Other viruses encrypt their code, making it impossible to decompile. There’s also polymorphic viruses that mutate their code every time they replicate. Virus authors often encrypt their polymorphic viruses as an additional armor. Often times, the virus will re-encrypt itself each time it replicates, thus allowing it to evade anti-virus signatures. And finally, some viruses will try to hide their location from malware analysts by fooling them into thinking the malicious file is located somewhere else.
Worms

Worms are self-replicating, malicious code. They spread through the Internet through different transport protocols, which require no human interaction to spread. That’s a key difference from our virus counterpart. A worm resides in memory and tries to replicate as much as it possibly can until every device on the network is infected. And of course, it will spread onto the Internet if it can. We’ve had several different worms released both intentionally and accidentally onto the Internet over the years. The consequence were very damaging.
Take the Morris worm, for example. This worm was released onto the Internet in 1988 for the simple purpose of just seeing how big the Internet really was. Unfortunately, a coding flaw turned it into a damaging piece of malware that infected many, many computers worldwide.
Trojan Horses

Trojan horses are the third class of malware we often hear a lot. Trojan horses are programs that look beneficial, such as a nice screensaver, game, or free antivirus, but in actuality, they do something malicious. As you can already guess, Trojan horses get their name from the tale of the Trojan War in which the Greeks disguised a huge, wooden horse as a victory trophy for the Trojans. The Trojans, fooled by this gift, heaved it into the city of Troy and celebrated. But, what the Trojans didn’t know was that Greek soldiers were hiding inside the wooden horse. When the time was right, the Greek soldiers climbed out and destroyed the city.
Trojans can have payloads similar to viruses, but many times, Trojans will deliver spyware and logic bombs. I’ll get into those classes of malware soon.
There are also different types of Trojans too
Rogueware

Rogueware masquerades as a free trial antivirus program. How it typically works is you’ll go to a malicious site that pops up a window stating your computer is infected. It’ll do a fake scan and it’ll display different types of infections on your computer.
The infections are bogus, but they are displayed to scare you. The fake antivirus program will tell you that it found several infections, but you will have to download or buy the full version to fix your computer. Once the victim is tricked into downloading the fake anti-virus program, their computer then becomes infected.
Ransomware
We’ve been hearing about ransomware a lot in the past year or so. Ransomware is a specific type of Trojan that takes control of your computer. The Trojan might freeze/lock your computer or it might encrypt the contents of your computer. To gain back control, you have to pay a ransom to the attacker, usually in bitcoin.
The “Police Virus” is a type of ransomware that usually pops up when victims are searching for pornography Web sites. Typically, a pop-up window will display a fake message from the FBI accusing the user of illegally downloading child pornography. Sometimes, it will hijack the victim’s webcam and display the activity in the victim’s room. At the end of the message, the victim is required to pay a fine to gain access back to their computer.

Another form of ransomware is called “Cryptolocker.” This type of Trojan takes control of the victim’s computer and encrypts all the files. It is impossible to decrpyt the files without the decryption key. Victims are usually prompted to pay a ransom within 72 hours, or they will lose the decryption key forever.

Ransomware is pretty serious. It’s cost organizations a lot of money to fix this issue. The damage of ransomware is expected to exceed $5 billion by the end of 2017.
Spyware
Spyware is pretty scary. It is the fourth class of malware discussed here. Spyware is installed on a victim’s computer without their knowledge or consent. Spyware usually installs a search engine on your Web browser tool bar, which also acts as a key logger. This means that whatever the victim types on his or her computer, it will be reported back to the spyware author. One symptom of spyware is a slower computer.
Spyware is often delivered through Trojans.
 Key loggers can also be installed manually onto someone’s computer.
Key loggers can also be installed manually onto someone’s computer.
Adware

This is a type of malware that isn’t really malicious, but rather an inconvenience to the victim. Adware displays constant pop-ups and advertisements that eventually slow down your computer.
Rootkits

Rootkits suck. They are groups of programs that avoid detection from the computer and anti-virus programs by hiding their running processes. Rootkits are known for modifying system files, like the Windows Registry. The Windows Registry is where the computer stores important information detailing OS configurations, software and hardware settings, and user preferences. Rootkits get their name from the fact that they have “root-level” or “system-level” access to your system. Rootkits can be used to install backdoors onto your computer
Backdoors

Backdoors provide an alternative route into your computer. Often times, application developers will code backdoors into their applications. This is usually intended for maintenance purposes, but some developers can use it for more malicious reasons. We see this a lot in Android devices where many malicious applications find their way into the GooglePlay store.
Logic Bombs

Logic bombs execute in response to an event, such as a time or date. It may be next week or next year. Whatever the case, the event is what triggers the logic bomb to execute its malicious code or script. Logic bombs are popular amongst disgruntled employees. Before they leave their company for good, they install a logic bomb on the system. After a certain amount of time, the logic bomb executes and infects the rest of the devices on the network. By having the logic bomb go off when the employee has long since left the company, digital forensic experts are less likely to suspect him or her.
Botnets

Botnets are a large network of infected computers. They get their name by combining “robot” and “network” Each infected computer in a botnet is called a “zombie.” The botnet responds to the commands of the person who manages the botnet, the bot herder. Botnets are used to carry out DDoS attacks, mass spam, or spread more malware.
That’s All for Malware
And that’s it! So far, I’ve discussed various classes of malware, including viruses, worms, Trojans, spyware, adware, rootkits, logic bombs, and botnets. I hope this gives you a better understandings of these threats.
References
Gibson, D. (2017). CompTIA SECURITY+ Get Certified Get Ahead SY0401 Study Guide. Virginia Beach, VA: YCDA, LLC

