Introduction
The biggest vulnerability confronting cybersecurity professionals today is one we aren’t even fully prepared to handle. This vulnerability requires cybersecurity specialists to be armed with the latest technology in network and information security in order to safeguard US critical assets. The FBI and CIA acknowledge its existence and its significant risk to critical and critical information infrastructures, yet the U.S. government lacked any adopted policies to protect against it only until recent years.
Cyberterrorism is the newest impending threat that may eventually exploit the vulnerabilities of the US’s critical information infrastructure, Because a cyberterrorist attack has yet to occur, there is not too much information concerning the subject at hand. Fortunately, there are a minority of well-informed scholars that appreciate the significance of this vulnerability and the impact it could have if cyberterrorists successfully exploit these vulnerabilities.
What is Cyberterrorism?

It is difficult to define a term as ambiguous as “cyberterrorism.” Scholars and government agencies have all formulated definitions of what cyberterrorism is defined as; however, no such definition has been officially adopted. According to the FBI, cyberterrorism is the, “premeditated, politically motivated attack against information, computer systems, computer programs, and data which results in violence against non-combatant targets by sub-national groups or clandestine agents.” An additional definition offered by Joe Valacich and Christoph Schneider, two prolific scholars in the fields of computer science and information systems, define cyberterrorism as, “the use of computer and network technologies against persons or property to intimidate or coerce governments, civilians, or any segment of society in order to attain political, religious, or ideological goals” (Valacich & Schneider, 2014, p. 412). Cyberterrorism is also defined as the use of “computer networks and technologies as a means for conducting attacks, and targets critical national infrastructures or governmental assets, has a psychological, social, political or religious motive, causes harm to individuals or groups, or physically damages infrastructures or assets” (Mazari, Anjariny, Habib, & Nyakwende, 2015, p. 12). The above definitions imply that the ambiguous definition of cyberterrorism, although very indistinct, encompasses similar themes. Each definition covers universally accepted principles that cyberterrorism comprises of a political, social, religious, and/or ideological attack against a government entity that uses computer technology maliciously against Information Systems (IS) and computer technology itself.
Unbeknownst to most people, cyberterrorism has never actually occurred yet, and we can’t be assured it won’t happen. Since 9/11, the U.S. government has taken necessary precautions in defending valuable assets in its Information Systems (IS) and critical infrastructure by protection and enforcement policies. In the wake of the US Department of Homeland Security’s creation of the Office of Infrastructure Protection and the USCYBERCOM, we’ve begun to see the government take an active role in national security, safety, and economic vitality. Although these precautions reduce the likelihood of a successful cyberterrorist attack it does not however, suggest that the U.S. is one-hundred percent secured. The U.S. infrastructure contains complex, interdependent networks and systems that include industries and delivery capabilities, which provide consistent dispenses of products and services. Each component of this infrastructure is essential to our defense and economic security.

Two sub categories of infrastructure are critical infrastructure and critical information infrastructure. The U.S. critical infrastructure contains systems and facilities so vital to our defense that if any component were to be compromised, it would likely result in a debilitating impact on national and economic security. Think of critical infrastructure as the nation’s banks, power plants, water and gas pipe lines, electric utilities, and so on. Critical information infrastructure, on the other hand, is the electronic technological components of critical infrastructure. These components allow nations the ability to exchange information needed to produce essential goods and services for which populations greatly depend (Maimon, 2014). This includes networks, wireless networks, satellites, and so on.
Why Are We Vulnerable?

Due to the globalization of infrastructure and the fact that the U.S. heavily depends on these assets, I would argue that the US is 100 percent dependent on it’s critical infrastructure. The bad news is that our critical and critical information infrastructures are vulnerable to cyberterrorist attacks. Much of the critical infrastructure industrial facilities and utilities that allow the U.S. to perform its everyday routines for its citizens are owned and managed by the private sector. Each of these private companies handles its own security of industrial control systems. Many of the systems implemented in these facilities were installed with little-to-no cybersecurity elements. Some of these systems are purely static computing environments; devices with their OS and hardware tightly coupled together. The past decades, however, have revealed the dangers of not having secure systems. Unfortunately, some of these vital networks connect to the Internet, making them susceptible to hacking. So, it is within the best interest of the U.S. government to collaborate with the private sector.
It almost seems as if we are in a Cyber Cold War with China and Russia. We can expand on this from the fact that most specialists concur China and Russia regularly prowl around in U.S. critical information infrastructure and government databases to gather information and vulnerabilities to use in the event of a future dispute between our nations. James Lewis, a cybersecurity expert working for the Center for Strategic and International Studies (CSIC), explains that this is an effective military tactic. Currently, terrorist groups like ISIS do not have the capability of waging large-scale cyberterrorist attacks against the US, but they will get better as the years go on. China, on the other hand, certainly has the capability to administer a state-sponsored cyberterrorist attack against the US. Will they do it? Not likely.

Interference with critical and critical information infrastructure could quite possible cripple the US. Take for example, “Supervisory Control and Data Acquisition (SCADA)” Systems that inspect and regulate the operations of most critical infrastructure. Based on digitized feedback collected from SCADA sensors, these computers monitor and adjust switching, manufacturing, and other processes in large industrial facilities. It is these SCADA systems that regulate electricity, power generation, water, oil and gas pipelines, and so on. If SCADA systems were compromised by a cyberterrorist attack, for instance, we could picture potential mass blackouts, communication disruptions, power plant meltdowns. Leave it to your imagination. Regardless what the threat vector is, it will result in public harm and mass hysteria.
In January of 2008, a CIA analyst unintentionally leaked confidential information that hackers managed to hack into the municipal utilities of multiple locations outside of U.S. boundaries and disrupted electrical equipment, which resulted in the complete power outages of multiple cities. The CIA has yet to disclose any information about where the blackouts occurred, but the alarming part of this real-life scenario is that the hackers got away (Derene, 2009).

The U.S. critical and critical information infrastructures are just as vulnerable to hacking since its critical infrastructure has been known to suffer from various glitches. In August 2006, a nuclear power plant in Alabama experienced a glitch when its plant’s administrators failed to regain control of one of its recirculation pumps. It turns out that there was excess data traffic on the control system network, resulting in the plant to go offline. Since nuclear power plants generate twenty percent of the nation’s power, a hacker could conceivably exploit this vulnerability and cut off a good portion of U.S. power supply.
In June of 1999, in Washington, a pipeline of the Olympic Pipe Line Company ruptured and released 237,000 gallons of gasoline into a nearby creek in Bellingham. Soon afterward, the gasoline ignited an area over a mile long and killed three people along with damaging the city’s water treatment facility. All of this destruction was the result of a simple typo entered into the company database by an employee. These relatively simple and seemingly minor glitches are all it takes to cause major, and often times, catastrophic events. To a cyberterrorist hacker, it’s a walk in the park if they somehow gain access.

Back in 2007, a video leaked from the U.S. Department of Homeland Security depicted a project sponsored at the Idaho National Laboratory. The experiment, nicknamed the “Aurora Experiment,” demonstrated how an over-the-internet- cyberattack could wipe out large essential machinery. Derene (2009) specifies the details of the video by stating that the video panicked those in the utilities industry. Statements given by the Dept. of Homeland Security described the experimental hack as a spoofing or man-in-the-middle attack. Spoofing and man-in-the-middle attacks are EASY to perform. The director of control systems security, Sean McGurk, stated that this type of vulnerability is commonplace in assets of critical infrastructure. Hacking vulnerabilities such as this should not be an accepted common occurrence for assets upon which the nation relies.

One of the most popular stories involving the vulnerability of critical and critical information infrastructure took place in Queensland, Australia in 2000. A computer expert named Vitek Boden was disqualified from a job in the municipal government, and with a newfound appetite for revenge, Boden resolved to hack into Queensland’s computerized waste-water management system. Boden hacked into the system forty-six times over two months instructing the system to spill over one-hundred thousand gallons of waste water and sewage into public parks and rivers. Dubbed the “Maroochy Shire Incident,” this event demonstrates how relatively easy it is for determined hackers to hack into and seriously disrupt critical information infrastructure. Because cyberterrorists are likely to target the already vulnerable and crucial assets of the nation’s critical information infrastructure, it is a good idea that IT managers educate themselves on how to protect these complex systems.
Why Do Cyberterrorists Use Cyberspace?
Cyberspace can be considered a safe haven for cyberterrorists since it is rather an effortless task for a cybercriminal to evade detection. Just open up the Tor browser and perhaps use a VPN. Voila, your Internet activity and location are hidden from your ISP. Intelligent intruders who manage to break into a targeted system can selectively delete event logs using “rootkit” software in the Windows’ Operating System (OS), thus effectively covering his/her tracks of any malicious processes or programs (Vacca, 2013, p. 84). Using these perks, Goodman et al. (2007) suggest that cyberterrorists use cyberspace for three reasons discussed below.
The first reason concerns cyberspace’s anonymity. Because cyberspace is inherently an anonymous network to begin with, it is relatively easy to gather intelligence, collaborate with other cyberterrorists, conduct research, acquire skills, and create communication networks without being tracked. It is painlessly simple to disguise an IP address or communicate over encrypted tunnels. Communication tools, such as chat rooms, blogs, and e-mail are being used by terrorists for recruitment, funding, and communication. In addition, various Web sites contain volumes of easy-to-obtain illegal information with reference to building explosives and other weapons, obtaining false identification, and much more. Many of these are sure to be found on the dark web.
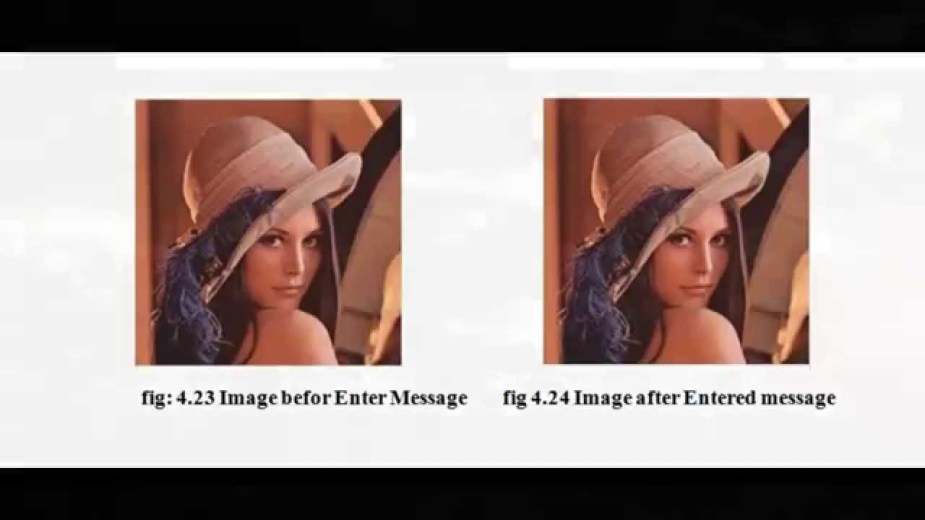
The second reason involves the confidentiality of cyberspace. Commercial encryption tools offer cyberterrorists a system of communication through concealed channels. With these encryption tools, cyberterrorists recognize that detection of their covert communication is highly unlikely (Goodman et al., 2007). There is also the possibility of creating covert channels through transport protocols, like TCP. By setting certain bits in TCP headers, cyberterrorists or spies can transmit secret messages back-and-forth. Cyberterrorists have also been known to communicate via “steganography” techniques, which involve concealing messages inside pictures. Cyberterrorists can even use Web sites in what’s called “electronic dead drops,” which comprises changing the byte count to embed messages in images.
And finally, the last reason Goodman et al. (2007) explains why cyberterrorists use cyberspace pertains to its accessibility. The accessibility of cyberspace allows individuals worldwide to experience greater access to the internet through three factors. Number one, cyberspace’s widespread web-based tool development enables worldwide communication. Think of the Internet as a globally routable network. Number two, computers are ubiquitous, allowing for improved productivity and collaboration. And number three, globalization and the expansion of the world market allow for greater accessibility worldwide.
Information Warfare

Although the threat of cyberterrorism has been reduced since 9/11, a variant of cyberterrorism known as information warfare (also referred to as “cyber warfare”) remains an ongoing dilemma. The data breach of the Office of Personal Management (OPM) in June of 2015, which compromised over 4 million people’s personal information is the most recent example of information warfare. An attack on confidential government information, such as social security numbers, job assignments, clearances, and performance evaluations will most certainly impact political and societal stability. Nevertheless, Wall (2007) stresses that it is not just the threat to Information Assurance (IA) that impacts society, but the results of a large scale attack (e.g., the OPM data breach) that undermine public confidence in the systems being attacked.

Another recent example of information warfare was the cyberattack against Sony Pictures on November 24, 2014. On that historic Monday morning, Sony employees logged in to their computers to the sound of gunfire and a picture of a fiery skeleton looming over the heads of the studio’s executives (Elkind, 2015, p. 67). After stealing most of Sony’s confidential information, the malware created by the Sony hackers spread from machine-to-machine, erasing every bit of stored information on 3,362 of Sony’s 6,797 personal computers and 837 of its 1,555 servers. As unforgiving as these hackers were, they additionally added a special deleting algorithm that overwrote Sony’s data over seven different ways. Afterwards, the malware crashed every computer’s startup software, rendering them completely useless p. 65). It is speculated that the Sony hackers responsible for the company’s downfall were connected to North Korea in protest to a movie called The Interview, which was scheduled for release the following month of December of 2014. A North Korean spokesman explained that the release of the movie would be an act of war and terrorism and threatened with a “merciless countermeasure” if the movie were to be released (p.74). North Korea had been responsible for the “DarkSeoul” attack in March 2013, which cost South Korean banks over $700 million in damages as well as freezing ATM machines and 30,000 erased hard drives. It is worth noting that, in this instance, the North Korean hackers involved in the cyberattack against South Korea also posted warning notices with skeletons; therefore, it could be safe to assume that North Korea was behind the cyberattack against Sony Pictures (p. 75). Although the assistant director of the FBI’s cyber division at the time, Joseph Demarest, claimed that the malware used by the Sony hackers was sophisticated enough to penetrate 90% of the defenses available in today’s private industry, it does not change the fact that the company’s electronic security failed to employ basic safeguards to prevent the attack (p. 67). Edit: I believe the Sony hack was actually an insider working in Japan.
A final example of information warfare occurred during the 2000, U.S. presidential election. A series of Web attacks that changed information on targeted Web sites involved intruders with various political motives. The attackers snooped on political sites and launched several Denial-of-Service (DoS) attacks (Valacich & Schneider, 2014, p. 414).
What Do We Anticipate Cyberterrorists to Do?

Goodman et al. (2007) believes cyberterrorists seek several opportunities in cyberspace. Technology helps facilitate attacks as well as fast communication and recruitment, thus cyberterrorists seek cyberspace as a support tool. Their main targets, however, are critical and critical information infrastructures, as well as other vulnerable targets. Cyberterrorists also seek membership via “networked terrorism forums,” which are anonymous Web sites that provide a sanctuary for those pursuing to conduct business in cyberterrorist agendas. Prior to 9/11, Al-Qaeda used these forums as well as other Internet communication tools to communicate, recruit, and coordinate their terrorist operations (para. 21). Known terrorist Web sites also tend to incorporate fundraising through electronic money transfers and money laundering. Some of these terrorists Web sites put up what are called “fronts,” such as Islamic charities, hospitals, and humanitarian projects, which trick computer illiterate users into donating money to these terrorist organizations (para. 23). As mentioned earlier, cyberterrorists also research knowledge in constructing weapons, especially explosive devices. They also seek information on how to create fraudulent identification, such as passports (something I’ve noticed on the dark Web).
Defending Critical and Critical Information Infrastructure

There are a multitude of useful approaches and techniques that can be implemented by cybersecurity professionals to defend critical and critical information infrastructures. A considerable area of concern is defending against the threat of insiders. Insiders are those persons with authorized access to a business, organization, agency, or company that have the potential to do harm. Goodman et al. (2007) suggests that there are two methods to deal with the threat of insiders. The first method involves deep pre-employment investigations of applicants in order to adequately remove possible untrustworthy future employees. The second method incorporates sturdier forms of “containment and compartmentalization of access” in companies and organizations. What Goodmen et al. (2017) is referring to is better access control, identity management, authorization, and authentication.
Because it is prudent to expect cyberterrorist attacks against critical and critical information infrastructure in the near future, it is important to understand how these attacks should be handled. Two types of defenses to cyberterrorism are active defense and passive defense. Active defense imposes serious forms of penalties against the attacker, which includes identifying and exposing the attacker, investigation, prosecution, or even pre-emptive attacks and counterattacks (para. 30). Passive defense is more laid back since it involves incorporating various technologies and procedures to protect IT assets of critical infrastructure (para. 31). Firewalls, UTMs, Web security gateways, Intrusion Detection Systems, Intrusion Prevention Systems, and honeypots, are just some of the many technologies used in passive defense.

In addition to the two types of defenses, there are also three stages of defense that will aid against a cyberterrorist attack. The first stage is prevention. Prevention seeks to identify the attacker as well as persuade him/her that retaliation and punishment is highly probable. Goodman et al. (2007) states that effective prevention procedures can be accomplished by banning cyberattacks by law, deterring attackers through policies that provide a high possibility of punishment and detection, and launching pre-emptive attacks (para. 33-38).
The second stage of defense includes a combination of incident management, mitigating an attack, and damage limitation. These three procedures help IT managers prepare for and conduct a suitable defense strategy, defeat the attack, and identify and limit the damage of the attack. This can all be accomplished in a number of ways. Indications and warnings of an attack can be detected by Intrusion Detection Systems (IDSs), which could notify network administrators of an occurring cyberattack against critical and critical information infrastructure. It is also a good idea to harden the organization or company’s system via stronger password policies,, state-of-the-art firewalls (e.g., 3rd and next generation), biometric technologies, multi-factor authentication, and improved physical protection strategies (para. 39-41). Supplementing the company or organization with a shutdown and reallocation policy might be beneficial as well. Goodman et al. (2007) suggests that a partial shutdown would allow the system to erect internal cyber barriers that is not typically tolerable under normal operations. This could allow isolation of certain chunks of the system that are compromised, which is similar to how antivirus software quarantines files that have been infected on personal computers (para. 43). Preserving information should also be considered through backup policies that also help allow an organization continue its operations at designated backup sites. Therefore, better BCPs and DRPs are a must.
In terms of actively defending against cyberterrorist attacks, however, performing strong and regular audits is critical to identifying an attacker (para. 44-45). Valacich and Schneider (2014) suggest managing Information Security (IS) through an IS security plan, which involves well-thought out security policies and procedures. These policies and procedures must detail what action is to be taken when security is breached. In other words, important questions to be considered include: how will sensitive information be stored, handled, transmitted, or destroyed? What defines appropriate computer use in the organization (e.g., Internet surfing, social networking, e-mail, etc.)? What kinds of technical security controls should be implemented, such as access limitations software, firewalls, audit software, and so on? It is vital that employees not only read, but acquire a deep understanding of these policies and procedures. It might be a good idea to require bi-annual testing of employees on computer safety, or at most, require a course that tests whether employees have a strong grasp for information security. An example would be the “Certified Information Systems Security Professional (CISSP)” certification that keeps employees up-to-date on information security (Vacca, 2013, p. 11). Other good certifications that expand the employees knowledge in cybersecurity is the CompTIA Security+ certification. As the saying goes, humans are the weakest link in a security system.

The last stage of defense is known as consequence management. In this stage, Goodman et al. (2007) describes the actions that should be taken after an attack has occurred. One action includes recovery, or the reconstructing of IT assets in order for the organization to continue its normal operations. It’s just like Incident Response (IR). The shutdown of defective machines and a damage assessment survey are great examples of recovery options that help a company or organization’s system repair (para. 48). Other responses include identification of the incident, containment of the incident, evidence gathering, investigation, eradication, recovery, and documenting/reporting. Another action comprises a proper retaliatory response. This particular response is concerned with identifying or punishing the attackers involved and learning valuable lessons that will aid in more effectively defending the organization from future cyberterrorist attacks. A counterattack, such as a DDoS attack or worm, may deter the attackers as well as other attackers from attempting another cyberattack against critical infrastructure. Then again, it may escalate the attack as well.
Fortunately, there is an assortment of technical resources that can safeguard IT assets in critical infrastructure without the need of an active defense. Physical access restrictions are just one of the many safeguards, which include various forms of authentication, such as passwords, physical locks, tokens, smartcards, biometric technology, AAA servers, and other access-control software (Valacich & Schneider, 2014, p. 419). Firewalls are another important resource as they are crucial to protecting a network from unwanted intrusions. Firewalls are hardware- or software-based and can be either packet-filtering firewalls, stateful firewalls, proxy firewalls, and so on (p. 421). Though the next generation firewalls will be the best option since they cover more layers of the OSI model. Let’s also not forget the important of NIDS, NIPS, and HIDS. They are similar to firewalls, but they are needed for an additional layer of security.
Encryption, which encodes messages via an encryption key before it enters the network, is also a useful method that might halt an eavesdropping cyberterrorist from conducting successful man-in-the-middle attacks on critical information infrastructure as observed in the Aurora Experiment. Cryptography can be “symmetric” in which one key is used for both encryption and decryption of plaintexts and ciphertexts. Or, encryption can be “asymmetric” in which there are two keys (e.g., a public key and a private key) used for encryption and decryption of plaintexts and ciphertexts (Goodrich & Tamassia, 2011, p. 388). For example, SSL and TLS use asymmetric encryption to encrypt http traffic. We can also use various encryption tunneling protocols for point-to-point connections. It goes without saying that anti-virus, anti-spyware, and anti-adware software are the most rudimentary safeguards to an unprotected system and should be implemented if an organization wishes to employ a strong system that can withhold a cyberterrorist attack. These types of software applications are crucial as malware can cause catastrophic damage to computers as seen in the Sony Pictures hack. Audit-control software, which was briefly mentioned earlier, is another crucial technological resource that can safeguard IT assets in critical infrastructure. Audit-control software allows system administrators the ability to automatically review event logs to spot suspicious activity and take appropriate action. Every computer user leaves an electronic footprint, which creates what is known as an audit-trail for the auditor to review. In addition, most of our network devices (e.g., firewalls, routers, IDSs) are logging events. This means network and security administrators are going to have to read a LOT of logs throughout the week. Thus, having some automation in the process is a bit of a relief. It is good idea for IT managers to stock their “toolbox” with up-to-date technology if they wish to successfully safeguard critical and critical information infrastructure.
Conclusion
With the world so heavily dependent on computers and information systems, there is no doubt that we are living in the age of technology. Although humans greatly benefit to what IT offers, such as our personal computers, landlines, Internet, mobile phones, transaction systems, and software, there are those out there who will use it with malicious intent. Although there are no reported events of cyberterrorism yet, we can’t assume this will remain the same 10 or even 20 years from now. Cyberterrorists understand that the technology we take for granted and heavily rely on can be used against us. Though terrorist groups don’t currently possess the resources to conduct a large-scale cyberterrorist attack, they will continue to recruit new members well-versed in exploiting vulnerabilities and forge alliances with hacking groups. Until then, we will continue to see more traditional terrorist attacks…for now. Right now, the U.S.’s biggest vulnerability is its critical and critical information infrastructure. For that reason, it is central to the safety of the nation’s way of life that cybersecurity professionals continue to educate themselves on protecting these systems from cyberterrorism. It is also crucial that the U.S. government continue in its investment in protecting its critical infrastructure and collaboration with the private sector. Companies must also be willing to invest in the latest security technologies and cannot be complacent when it comes to the protection of their assets.
Bibliography
Derene, G. (2009). How Vulnerable is U.S. Infrastructure to a Major Cyberattack? Popular Mechanics. Retrieved from: http://www.popularmechanics.com/military/a4096/4307521/
Elkind, P. (2015). Inside the Hack of the Century. (Cover story). Fortune, 172(1), 64-89. Retrieved from: http://eds.b.ebscohost.com.ezproxy.umuc.edu/eds/pdfviewer/pdfviewer?vid=1&sid=30042636-adda-40c4-890b-299543a2c72b%40sessionmgr115&hid=112
Goodman, E. S., Kirk, J., Kirk, M. (2007). Cyberspace as a Medium for Terrorists. Elsevier, 74 (2). Retrieved from: http://www.sciencedirect.com.ezproxy.umuc.edu/science/article/pii/S004016250600148X
Goodrich, T. M., & Tamassia R. (2011). Introduction to Computer Security. Boston, MA: Pearson Education Inc.
Maimon, D. (2014). Cyberterrorism [PowerPoint]. Retrieved from Lecture Notes Online Website: https://myelms.umd.edu/courses/1130298/files/
Mazari, A. A., Anjariny, A., Habib, S., & Nyakwende, E. (2015). Cyber Terrorism Taxonomies: Definition, Targets, Patterns and Mitigation Strategies. Proceedings Of The European Conference On E-Learning, 11-18. Retrieved from: http://eds.a.ebscohost.com.ezproxy.umuc.edu/eds/pdfviewer/pdfviewer?vid=1&sid=c969fc94-3158-429b-af6e-72af85733d52%40sessionmgr4001&hid=4208
Rouse, M. (2010). Cyberterrorism Definition. TechTarget. Retrieved from: http://searchsecurity.techtarget.com/definition/cyberterrorism
Tereshchenko, E. (2013). U.S. Foregin Policy Challenges: Cyber Terrorism & Critical Infrastructure. E-International Relations Students. Retrieved from: http://www.e-ir.info/2013/06/12/us-foreign-policy-challenges-of-non-state-actors-cyber-terrorism-against-critical-infrastructure/
Vacca, R. V. (2013). Computer and Information Security Handbook (2nd Ed.). Waltham, MA: Elsevier Inc.
Valacich, J. & Schneider, C. (2014). Information Systems Today: Managing in the Digital World (6th ed.). Upper Saddle River, NJ: Pearson Education Inc.
Wall, S. D. (2007). Cybercrime. Malden, MA: Polity Press.




