Many people confuse authentication with authorization. They both start with “auth,” so I can see how these terms might be mistakenly used interchangeably. The reality is authentication comes before authorization.
Authentication is simply proving you are who you say are. For example, you provide your identity, such as a username or E-mail, and then you must prove that identity belongs to you. There are 5 factors of authentication that can prove our identification.
Something You Know
The something you know factor is a shared secret between you and whoever you are authenticating to. A PIN number, for instance, is a shared secret between you and your bank. By providing your PIN number to an ATM, you are proving that you are the owner of the bank account.

Besides a PIN number, another example would be a password. Only you should know the passwords to your accounts.
Not surprisingly, the something you know factor of authentication is the weakest form of authentication, primarily because people use weak passwords and write them down where people can see them in plain view.
Something You Have
The second factor of authentication is something you have, such as a smart card. Smart cards look like credit cards, except we use them to gain access to systems. Every smart card contains a microchip and a certificate that contains the user’s private key (used for PKI). When the microchip is exposed to the electromagnetic field of a card reader, the microchip is powered on and data transfer can occur. Two popular smart cards we use are Common Access Cards (CACs) and Personal Identity Verification (PIV) cards.

A token, sometimes referred to as a “fob,” is another form of something you have. These are electronic devices that project a random number onto an LCD screen. The number on the screen usually changes every 30-60 seconds. When logging on to your account with your password, you may also be required to enter the random number as well. Once it’s used, you cannot use it again to login. This makes it a one-time password. By adding the password (something you know) and the token number (something you have), you are combining two factors of authentication; therefore, we call this “two-factor authentication.”

Tokens that are in USB form are called USB tokens. They too have a random number displayed on them at certain times.
The last example of something you have are “HMAC-based One-Time Passwords (HOTP).” This is an open-standard used to create one-time passwords similar to what we use in tokens. When you need to login, you can request an HOTP number. The security challenge with HOTP is that the number never expires. Once the HOTP number is generated, it will not expire until you use it. Thus, the risk of using HOTP is that a shoulder surfer could use the HOTP number too. As a result, it’s highly recommended to use “Time-based One Time Passwords (TOTP)” that expires after 30 seconds.
Something You Are

The something you are factor of authentication is just that —something you are. So, your fingerprint, retina or iris image, palm print, or another physical characteristic can be used to identify you. We call these biometric systems. For example, if you want to gain entry into a secure area of a building, you would scan your thumbprint into the biometric scanner. The biometric scanner would then compare our thumbprint to the thumbprint in its database when you first registered with the biometric scanner. If the two thumbprints match, it proves your identity and you’re then granted access.
Something You Do
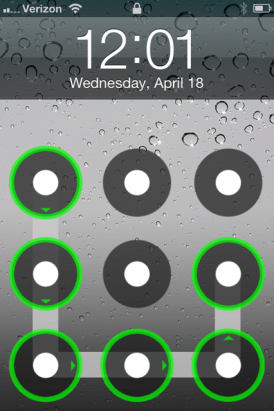
Most people aren’t familiar with the something you do factor of authentication. Have you unlocked your phone by swiping your thumb in a series of patterns? That is an example of something you do. This is called a “gesture.” Windows 8 possesses a feature that allows the user to tap or circle specific areas of a picture on a picture chosen by the user. It’s called “picture passwords.”
Somewhere You Are

The final factor of authentication is somewhere you are. This factor of authentication depends on geo-location technologies to track your IP address. Facebook, for example, tracks your IP address whenever you login to your Facebook account. If you were to login from another state, you might be notified of a suspicious login.
References
Gibson, D. (2017). CompTIA SECURITY+ Get Certified Get Ahead SY0401 Study Guide. Virginia Beach, VA: YCDA, LLC

