The “Ping of Death” abuses the “Internet Control Message Protocol,” which we rely on for troubleshooting and reporting utilities on our network, such as the “Ping” command. Network folks usually “ping” another host or system, either on the local network or on the Internet, to test its reachability. For example, you could ping a Web server, as the example below depicts. 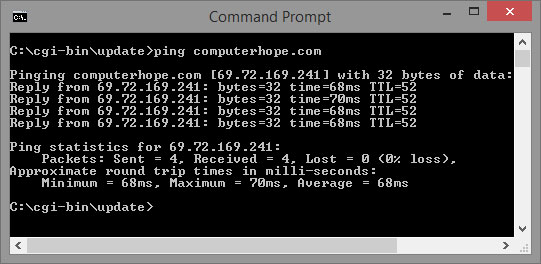
Pings are actually “ICMP echo requests.” Windows systems send out a maximum of 4 pings, but you can change this default setting if you wish. When a system receives an ICMP echo request, it should (unless configured not to) reply with an “ICMP echo reply.” Notice in the image above how the Web server for computerhope.com (69.72.169.241) replies to each of the 4 pings. The average response time is 68 milliseconds. Also, by default, ping waits 4 seconds for each response to be returned from the target system. If the target system does not reply, there will be either a “Request Timed Out” or “Destination net Unreachable.” This may happen for several reasons; however, it’s usually because there a router along the way dropping ICMP packets (which is a typical configuration on many routers), there’s a firewall blocking the ping, or there is no route to the target system.
The ping of death creates an over-sized ping. When an over-sized ping hits a system, a lot of weird things happen, such as crashing, freezing, and rebooting. Ultimately, it was a form of Denial of Service (DoS).
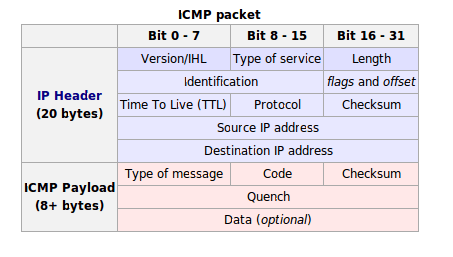
One important thing to remember is that any IPv4 packet (including a ping) has a maximum size of 65,535 bytes. There’s a 20-byte IP header and an additional 8-byte ICMP header in a ping. That leaves a remainder of 65,507 bytes. So, all an an attacker had to do was make sure the data area of the IP packet was at least 65,508 bytes. When the over-sized ping packet was fragmented, it would reassemble on the target system and the operating system wouldn’t know what to do.
Image Courtesy of teachweb
Through IP spoofing, attackers could hide their real IP address, effectively evading discovery. Some attackers even used a botnet to send hundreds and thousands of over-sized pings to just one system, which was essentially an overkill. By 1997, most operating systems were patched for this “Ping of Death” vulnerability. Because of that, many modern firewalls and routers block ICMP packets from getting into a network, making the ping utility a sometimes questionable troubleshooting utility. Luckily, we have other tools that can supplement a ping.
References
Juniper Networks. (2018). Understanding Ping of Death Attacks. Retrieved from https://www.juniper.net/documentation/en_US/junos/topics/concept/denial-of-service-os-ping-of-death-attack-understanding.html

[…] “Ping of Death” was mentioned in one of my earlier posts. It is an older-style DoS attack that also exploits ICMP. What it does is it sends out a an […]
LikeLiked by 1 person