Endpoints are end-user devices (think mobile, desktop, peripherals, or otherwise). Mobile smartphones, especially, are common attack vectors. Here, I’ll discuss the more predominant vulnerabilities facing our endpoints and what we can do to prevent and mitigate these problems.
Malicious E-Mail Attachments
Malicious e-mail attachments are always concerning because many employees click on them and end up downloading malware onto their system. This is big problem because malware doesn’t just stay on one system; it wants to re-infect more files and spread to other systems on the network. They also likely communicate out to a C2 node, which takes up out bandwidth. A good way to stop this is through user-awareness training. After all, humans are the weakest link in security.
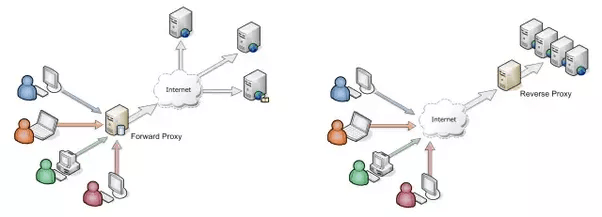
A forward proxy sits on the internal network, intercepting users’ traffic and forwarding on their behalf.
But, besides operational controls, we can use technical controls to thwart any malicious e-mails from getting inside our organization. We could use a forward proxy that performs content filtering (e.g., e-mail filtering). In this case, the proxy will inspect e-mails for malicious attachments. We could also use a Web Security Gateway, which is a type of Unified Threat Management (UTM) device for content filtering. The most obvious technical control, however, would be a SPAM filter.
Malicious Web sites and links
When employees get bored, they might do some “surfing.” Surfing the WWW isn’t something that should necessarily be prohibited, but it should definitely be restricted. Believe it or not, there are employees who surf to pornography and gambling sites. It may not be common; but nevertheless, you should be prepared to prevent that. These sites can be dangerous because they may hold malicious Drive-By Downloads. On top of that, while some users think they’re going to a legitimate site (perhaps to download some useful software or utility), they end up downloading a Trojan instead.
To prevent these types of incidents, you can use the same methods discussed above (e.g., a proxy server or a stand alone content filtering device). Some of these systems will inspect the Web sites that users attempt to visit for anything deemed unacceptable. You may also consider blacklisting known bad Web sites.
Lack of up-to-date Anti-Malware

Reprinted from “What Is The Difference: Viruses, Worms, Ransomware, Trojans, Bots, Malware, Spyware, Etc?,” by Tiwari, A, 2015.
Every node on your network should be running anti-malware. Most forms of anti-malware are signature-based and therefore require constant updating of new definitions (pretty much every day). Cloud-based technology makes this process more automated. You can expect lack-of-update vulnerabilities on your endpoints. Always follow a strict schedule of updating these anti-malware definitions. New malicious code is being discovered literally everyday and your anti-malware software cannot protect your endpoints from malware it doesn’t know.
Misconfigurations
Sometimes, we misconfigure an endpoint or we don’t harden it to our specified security standards. We can prevent this from happening by creating configuration and security baselines, which are used to ensure systems are deployed consistently by identifying the configuration and security settings of each system. These baselines contain the correct application settings, TCP/IP settings, and security settings for each endpoint. If you suspect a misconfiguration, you can compare the endpoint’s configuration to the baseline to identify any discrepancies.
Default Configurations
Default configurations are always frowned upon cybersecurity because their are usually online databases of them. Default passwords and user accounts should be changed and disabled, respectively. You can also use a configuration baseline discussed a moment ago to confirm your endpoints have the correct settings in place.
Also, consider comducting periodic user access reviews. These reviews examine what users have accessed over time to detect any sort of malicious activities. They also detect any unused accounts that should have been deleted long ago. User rights and permissions reviews also go a long way. They identify the privileges (rights and permissions) granted to users and compares them to what they should be. Sometimes, you might find an account with unnecessary privileges, such as access to a resource the user does not need to perform his or her job. Remember, always keep the principle of least privileges in mind.
If you are in a directory services environment and are implementing Active Directory, you can use Group Policy to apply configurations to every system in a particular Windows domain. This really saves system administrators time and effort.
Lack of Patching
Some systems may be lacking in the patch department. Most organizations are following a patch management schedule of when to update their systems, that is, until their vulnerability feed notifies them of a critical update. In that case, you’d want to make an Out-of-Band (OOB) patch.
References:
Maymi, F. J., Chapman, B. (2018). All-in-One CompTIA CSyA+ Cybersecurity Analyst Certification Exam Guide CS0-001. McGraw-Hill Education: New York, NY.

[…] as our endpoints contain a lot of common vulnerabilities, it makes sense to build a good defense in this layer as well. Workstations and other endpoints are […]
LikeLiked by 1 person