Kismet is a type of passive 802.11 (wireless) data-link layer packet sniffer and network detector. As long as you possess a network adapter that supports Monitor mode, you can sniff and identify 802.11a/b/g/n networks. Kismet is available for Linux, FreeBSD, NetBSD, OpenBSD, and Mac OS X. Although you can download and install it on a Windows system, it will only work for specific wireless hardware. If you have Kali Linux, Kismet already comes pre-packaged.
You may be wondering if it’s okay to display the SSIDs and BSSIDs of other networks. To be honest, anyone can open up their laptop and find the same information. It’s even freely available on Wigle.net. However, I won’t display anybody’s WEP or WPS networks since they are very vulnerable to attack.
Features
As a packet sniffer, Kismet has the ability to detect networks, even networks purposely hiding their existence by disabling the broadcast of their SSID. It does this by “channel-hopping,” which is a process of scanning each channel in the 2.4 GHz frequency band. Unlike other wireless sniffing programs, such as NetStumbler, Kismet is a “passive” sniffer, hence the need for Monitor mode. The wireless interface you choose to use can’t be associated with any Access Point (AP) while Kismet is in use and, as a result, the user cannot connect to a network, but can listen for all probes and 802.11 management frames. This allows Kismet to identify all wireless networks in range. Technically, networks that hide their existence do still send out broadcasts of their network; however, the SSID is blanked out. Kismet will detect these probes and display a “Hidden Network.”
By identifying networks in range, Kismet will display the AP, its MAC address (BSSID), the SSID (network name), the channel in use, encryption type, the number of packets transmitting on the network, the data the network was last seen, and even the MAC addresses of clients associated to a particular AP. Believe it or not, Kismet also supports Intrusion Detection System (IDS) capabilities. Various plug-ins even allow you to detect cordless telephones and Bluetooth!
Uses
Kismet can be used to identify and audit wireless networks and their configuration. They can also be used to identify wireless networks that are misconfigured or even unauthorized rogue APs. They can somewhat give you an idea of bandwidth, though that would be better suited for a different tool, like NetFlow Analyzer. Kismet also allows the user to save packet captures in a capture file compatible with tcpdump and Wireshark for further analysis. Hackers will use Kismet to identify hidden networks or networks that are vulnerable to exploitation.
Components
Kismet comes with the Kismet server (kismet_server) and the Kismet client (kismet_client). The Kismet server is what performs the packet sniffing and network detection, while the Kismet client is the GUI. If you need to do any additional configurations, you can modify the Kismet.conf file in /etc/kismet/.
Starting Kismet
Before you start Kismet, you need to add a packet source. This would be your wireless adapter. As I mentioned, Kismet requires that your wireless adapter be put in Monitor mode. Open up a terminal window and type airmon-ng start wlan0. This switches your wireless interface from Managed mode to Monitor mode (you can also accomplish this step in Kismet too).
You’ll be prompted to start the Kismet server, at which point you press Enter for “Yes.” Kismet will then start a connection at 127.0.0.1 by default.
Kismet will then ask you to identify the packet source in the “Add Source” window. Type in “wlan0mon” and press Enter for “Add.” If you didn’t already set your wireless interface to Monitor mode, you can type the name of your interface, which is probably “mon0.”
Already, you should see Kismet detecting networks. Click the “Close Console Window” option.
The Basics
Displayed in the Network pane will be a list of color-schemed networks detected by Kismet. The networks will all be displayed in a random order. Depicted below are the networks my wireless adapter has detected. There’s even a hidden network (“Hidden SSID”) that was captured. We may not have that particular network’s name, but we do have its BSSID and any clients associated with it.

Kismet displayed the networks it has detected
You’re probably wondering what the different colors mean. My color schemes are left in default. Note: Color schemes can be changed, so don’t rely on my color scheme. Your colors are probably different, but it isn’t hard to figure out what they mean. Navigate to Kismet > Preferences > Colors to find what your colors mean. Mine are:
- Yellow = Encrypted via WPA/WPA2
- Red = Encrypted via WEP
- Green = No Encryption (Open)
- Hi-Magenta = Decrypted
- Blue = Group
- White = Client list unknown
Change the color scheme to whatever you want it to be. Usually, users prefer green to mean “encrypted” and red to mean “unencrypted.”
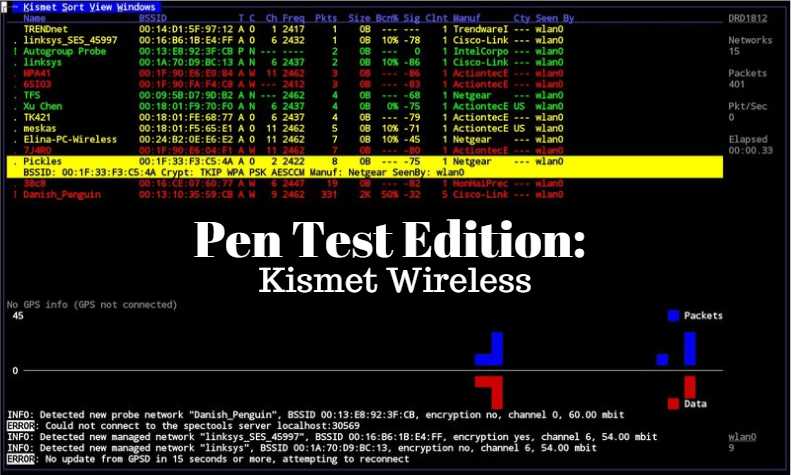
If you want to sort the networks in a particular order, you can navigate to the toolbar and click on “Sort” and choose an option from the drop down menu. As you can see from the image below, we can sort the networks by type, channel, encryption type, first seen, latest seen, BSSID, SSID, and number of packets. It’s up to how you want to sort all these networks out.

Sorting out the networks
The Network, Info, and Status Pane
Kismet is divided into 3 panes: Network, Info, and Status Pane, as depicted in the image below.

Kismet Panes. Reprinted from https://openmaniak.com/kismet_platform.php
Network Pane
The network pane gives you the following information:
- Name = SSID
- T = Type (e.g., AP, probe request, Ad hoc, Group, etc.)
- W = WEP (e.g., “W” for WEP; “N” for No encryption; and “O” for Other encryption in use).
- Ch = Channel number
- Pkts = Captured packets
- Size = Data captured by Kismet
- IP
Info Pane
The Info pane will give you the following information:
- Elapsed = The time elapsed since Kismet was launched
- Networks = Total number of networks seen
- Packets = Total number of packets captured
- Crypted = Total number of encrypted networks
- Weak = Initialization Vectors that reveal information about the WEP key
- Discard = Total number of discarded packets
- Pkt/sec = The total number of packets per second
Status Pane
The Status pane is always updating with new information, so it’s pretty much just a log of wireless events. For example, you’ll see the detection of new probes and networks, client associations, and alerts.
Identify the Particular Settings of a Network
Double-click on any particular networks of interest to display the specific settings of that network. As you can see below, we are able to obtain a lot of information about this one particular network. Let’s take a look at what we found.

Kismet allows us to view the following information about a particular network:
- SSID (Network name)
- BSSID (MAC address of Access Point)
- The AP manufacturer
- Timestamp when the network was first seen
- Timestamp when the network was last seen
- The mode of the AP (ad hoc or Managed/Infrastructure)
- Channel in use
- Frequency
- Advertising or Hidden SSID
- Encryption type (if any)
- Signal strength
- Noise
- Total packets captured
- Total data packets captured
- Total management packets captured
Identify Clients Associated to a Network
You can double-click on a network to bring up the specific settings of the network. After that, navigate to the toolbar and click “View.” From the drop down menu, select “Clients.” This will display all the devices currently connected to this network.
Kismet will display the MAC address, manufacturer, and additional information about the client devices. Network and security administrators can use this feature to identify known and unknown nodes connected to their network for auditing and security purposes. Attackers can target these clients in de-authentication attacks in an attempt to crack wireless passwords.
Additional Features
If you have any plug-ins you want to use, you can load them and select them by navigating to through the toolbar: Kismet > Preferences > Plug-ins. This is how you would be able to detect Bluetooth and cordless phones.
If you have a USB GPS Dongle, you can record the GPS coordinates of where you’ve located different networks. This would be great for war driving. “War driving” is the act of searching for Wi-Fi wireless networks by a person usually in a moving vehicle, using a laptop or smartphone (mostly Android). Wigle.net is a big war driving site that has been documenting GPS locations of wireless networks and cell towers since 2001.
Another feature you can do is look up the channel details for a specific network, which gives you a little more detail on signal and noise. Other features of Kismet include network statistics, tracking alerts, viewing packets per second, and viewing wireless packets.