When determining the impact of a computer security incident, it helps to classify the threat encountered, which usually occurs before the actual Incident Response (IR) process begins. Determining the impact will also determine whether the incident should even be considered an “incident.”
Think about what vulnerability the threat exploited. If this was an unknown vulnerability to your organization and the vendor, it would be a Zero Day exploit. Zero Days are extremely dangerous because no patch exists to fix this vulnerability. A Zero Day would constitute something serious and the information should be shared with the organization’s dependencies and the vendors so that they can create a patch as soon as possible. In the mean time, the organization should then work on an immediate compensatory control. For example, if a piece of code exploits a zero day in the organization’s perimeter firewall, they should replace that firewall with another firewall from a different vendor. A known threat, however, could be less serious in the fact that a patch probably exists for remediation, but the economic impact of the incident could still be severe. Is the computer security incident the result of an APT, or
“Advanced Persistent Threat?” APTs are very focused hacking groups that are usually state-sponsored. They would most certainly indicate a severe incident.
Preparing for computer security incidents is critical in mitigating its effects and reducing downtime. I suggest that most organizations familiarize themselves with several of the NIST Special Publications that cover these areas, such as SP 800-53, the “Security and Privacy Controls for Federal Information Systems and Organizations. SP 800-53 isn’t strictly reserved for organizations that manage federal information systems. Any organization can follow these guidelines. SP 800-53 helps organizations inventory their assets by categorizing them into a specific control category and then into a specific class (e.g., technical, operational, or management). During a Business Impact Analysis (BIA), organizations can then use these classifications along with FIPS 199 to assign their critical systems and processes a security objective along with the potential impact if they were compromised. Both the security objective and the potential impact create a “security categorization” for the asset, which helps organizations reveal what assets they should prioritize. If you want to read more about NIST SP 800-53 and FIPS 199, I cover them here. Another NIST special publication is SP 800-61 (revision 2). This publication contains the best practices for responding to computer security incidents. It includes a good preparation section, which I cover here. Yesterday, I published a blog post about the new version of the cybersecurity framework. This document would also be a good resource for preparation. Even though it’s aimed towards organizations and industries that are a part of the critical infrastructure, it will still help organizations prepare for cybersecurity incidents by being more risk-aware.
An additional resource is the SANS Institute Storm Center. The SANS Institute Storm Center updates daily on new and emerging threats or vulnerabilities. They keep a daily “diary” of the threats for the day and you can even listen in on their podcasts. As of April 20, 2018, the SANS Institute Storm Center reports vulnerabilities in Drupal web sites, which can be remediated with an update. The SANS Institute Storm Center also has an interactive threat map, which you can check out here. Proactively researching threats will keep you a step-ahead of cyber-criminals. The more prepared you are, the more likely hackers will go for other low-hanging fruit.
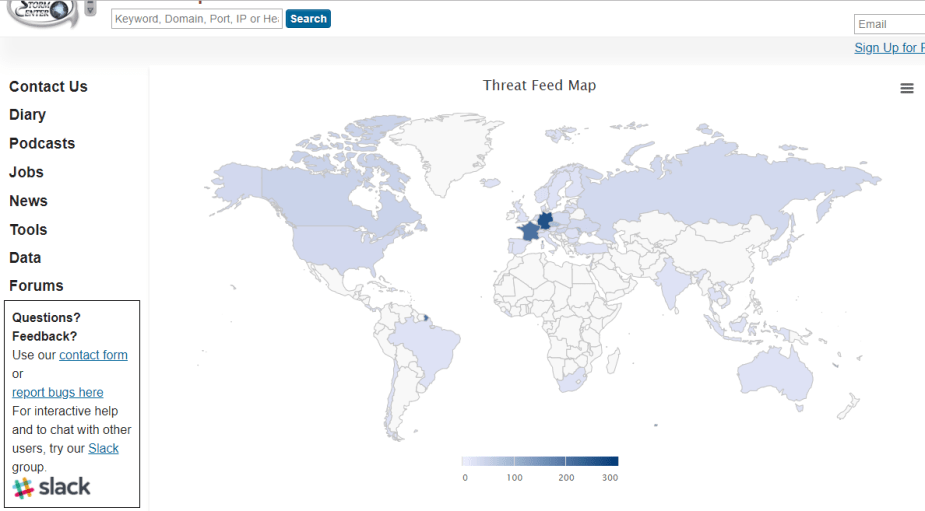
The SANS Institute Storm Center Threat Feed Map. Reprinted from the SANS Institute Storm Center
Determine the scope of the impact by evaluating the degree to which the systems were affected. This can be done by gathering information firewall logs, IDS/IPS alerts and logs, packet captures, NetFlow analyzers, file-integrity checks, wireless scans, systems logs, SIEM logs, all of which are great sources of information. Your organization should also already have a set MTD, which is the “Maximum Tolerable Downtime.” The MTD is the maximum amount of downtime the organization is willing to accept before total failure, which could range from minutes or hours to 30 days; it all depends on the organization’s type of business. Importantly, the organization should set a Recovery Time Objective (RTO) for systems and processes affected by the incident, which should be communicated to senior leaders.
How critical is the impact? Was the confidentiality, integrity, or availability compromised? How about all three? If organizations are prepared and already following the guidelines established in FIPS 199, then their critical assets would already have a security categorization to determine the criticality of the incident. For example, a security categorization for a bank’s electronic storage of payment card information would be Confidentiality = High; Integrity = High; Availability = High. This is because a compromise in the confidentiality, integrity, or availability of payment card information would result in a severe degradation in the bank’s mission to perform its primary function, financial loss, reputational damage, and a potentially serious financial harm to customers effected by the breach. That’s why we have the Payment Card Information Data Security Standard (PCI DSS) to regulate any entity that stores payment card information.
With that being said, to determine the impact of an incident, the organization should know the types of data involved. Whether it’s personal health information, personal identifiable information, or payment card information, there is a regulatory body overseeing protection of this information. In which case, the organization may be legally required to inform its customers and stakeholders. Obviously, data types such as these are more severe. If, however, the breach or incident doesn’t involve these types of aformentioned data types, then the organization may not be legally required to respond in a certain way. There’s also intellectual property, such as patents, copyrights, trademarks, and trade secrets. A data leak of an organization’s trade secret, for example, would definitely have an adverse effect on the organization. Likewise, the unauthorized disclosure of a company’s private or confidential information would cause more damage than a disclosure in proprietary or public information.
References
Cichonski, P., Millar, T., Grance, T., & Scarfone, K. (2012). Computer Security Incident Handling Guide (NIST Special Publication 800-61 Rev. 2). Retrieved from the National Institute of Standards and Technology Web site:https://nvlpubs.nist.gov/nistpubs/specialpublications/nist.sp.800-61r2.pdf
Maymi, F. J., Chapman, B. (2018). All-in-One CompTIA CSyA+ Cybersecurity Analyst Certification Exam Guide CS0-001. McGraw-Hill Education: New York, NY.
National Institute of Standards and Technology. (2004). Federal Information Processing Standards Publication (FIPS PUB 199). Retrieved from the National Institute of Standards and Technology Web site: http://nvlpubs.nist.gov/nistpubs/FIPS/NIST.FIPS.199.pdf
National Institute of Standards and Technology. (2014). Framework for Improving Critical Infrastructure Cybersecurity (version 1). Retrieved from the National Institute of Standards and Technology Web site: https://www.nist.gov/sites/default/files/documents/cyberframework/cybersecurity-framework-021214.pdf

