The “Federal Information Security Management Act,” or “FISMA,” is a U.S. federal law that arose from the E-Government Act of 2002. In this act, the U.S. government underlined the significance of improving the management of electronic government services and processes. FISMA provides the framework for organizations to develop and maintain the minimum security goals for protecting federal information systems and processes. This was the U.S government’s legislative approach to protecting its economic and national security interests.
However, FISMA had a major update in 2014 when President Obama signed a bill reforming FISMA into the newly reformed “Federal Information Security Modernization Act,” which is now the updated version. This “modernized” variant of FISMA comes with significant changes. For those of us who don’t know anything about FISMA, I’ll address and elaborate on its key components.
The Purpose of the E-Government Act
So, what is the E-Government Act?
The “E-Government Act of 2002” requires that all federal agencies and their senior leaders to conduct annual reviews of their information security programs. The results of these annual reviews are to be reported to the Office of Management and Budget (OMB). As an office within the Executive Office of the President of the United States, OMB’s primary responsibility is to oversee the Federal budget; however, to comply with this Act, the OMB must also collect the agency security program reviews and prepare an annual report to Congress.
The Act also seeks to promote the use of IT for the purpose of creating new opportunities for citizens seeking work in U.S. government positions. In contrast to traditional noncooperation, the Act alternatively promotes inter-agency collaboration in order to improve government functions, processes, missions, and programs. Apart from improving the flow of government operations, this Act seeks a cost-effective transformation of agency operations by utilizing best practices and guidelines established by the National Institute of Standards and Technology (NIST). And finally, the E-Government Act seeks to increase access to government information, but in a way that it reflects the current U.S. laws and regulations as they relate to privacy, national security, and so forth.
A Cheat Sheet To FISMA Compliance
FISMA is very lengthy, so I can only address so much. The 2014 update to FISMA arranges for the U.S. Department of Homeland Security (DHS) to administer the implementation of security policies for federal agencies, oversee the compliance of these policies (i.e., operational and technical assistance), and to assist the OMB. FISMA also establishes a cybersecurity information-sharing hub, which is the “National Cybersecurity and Communications Integrations Center.” In addition to the annual reports to the OMB, federal agencies must now report all computer security incidents and data breaches. To comply with FISMA, organizations have to meet the following criteria:
- Maintain an Inventory of Federal Information Systems
- Categorize each Federal Information System according to its risk level
- Establish and Maintain A System Security Plan
- Select Security Controls
- Conduct Risk Assessments
- Acquire Certification, Accreditation, and
- Continuous Monitoring
NIST SP 800-37 (Revision 1) to the Rescue!
From the requirements listed above, FISMA emphasizes a risk- and control-based approach to protecting federal information systems. Luckily, the NIST saves organizations and federal agencies a lot of time with its Special Publication 800-37 (Revision 1), a “Guide for Applying the Risk Management Framework to Federal Information Systems.” In this document, the NIST drafts a comprehensive delineation with respect to how a “Risk-Management Framework (RMF)” at an organization-wide level can be achieved by performing a 6-step process. SP 800-37 revision 1 tactically recruits the assistance of additional NIST special publications in the RMF, which just so happens to meet every top requirement necessary to comply with FISMA.

This 6-step process is simple to understand, but at the same time, it’s very impactful. The process also recruits the assistance of additional NIST special publications, such as FIPS 199/200, SP 800-60, SP 800-37, SP 800-53, SP 800-34, SP 800-61, SP 800-128, SP 800-53A, and SP 800-137. Some of these publications will already be familiar to you if you read my post, 10 Security Frameworks Every Cybersecurity Analyst Should Know. The 6 steps outlined in SP 800-37 are:
- Security categorization: With the aid of FIPS 199, organizations can categorize their federal information systems, and the information they process, store and transmit based on a Business Impact Analysis (BIA). Information systems and processes are categorized according to a specific security objective and a resulting potential impact. Information systems and the information they process are assigned 3 “security objectives,” which are confidentiality, integrity, or availability. From there, each security objective is assigned a “potential impact” of low, medium, or high depending on how severe a particular compromise might be. Together, the security objective and potential impact create a Security Categorization. Take a look at the table below to grasp a better understanding of how NIST advises organizations to categorize their information systems.

- Security control selection: The 2nd step in this process requires the selection of appropriate security controls for information systems. These security controls are organized into 18 families. Additionally, each family is classified into 1 of 3 classes, which are technical, operational, and management. Each family consists of a long list of subsidiary controls. For example, the Access Control family contains 25 controls related to its family, such as Access Control Policies and Procedures, Account Management, Access Enforcement, Information Flow Enforcement, Separation of Duties, and so forth. Security control baselines (e.g., low, medium, and high) assist in establishing these controls. Each information system must meet the minimum security requirements required in order to comply with FISMA. The minimum security requirements of the Access Control family as established in FIPS 200 are that “organizations must limit information system access to authorized users, processes acting on behalf of authorized users, or devices (including other information systems) and to the types of transactions and functions that authorized users are permitted to exercise.”

- Security control implementation: Organizations must implement the controls and document how exactly they are deployed according to the guidelines established in SP 800-34, SP 800-61, SP 800-128, etc. As a quick example, SP 800-34 is the “Contingency Planning Guide for Federal Information Systems.” In this document, organizations learn about the diverse varieties of contingency plans and control strategies for backup and recovery. However, organizations shouldn’t feel the need to implement every control. This approach is “cost-ineffective” and infeasible. Only relevant security controls are required to comply with FISMA.
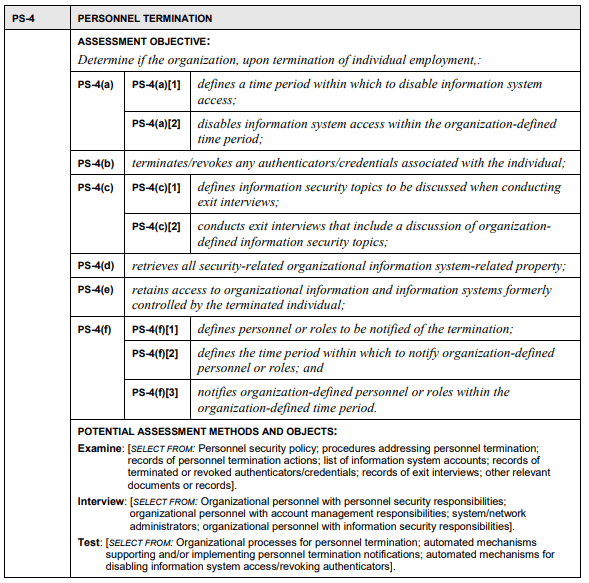
- Security control assessment: During this phase, the security controls must be assessed to confirm that they are implemented correctly and operating as intended. To do this, organizations can seek the guidance of SP 800-53A, “Assessing Security and Privacy Controls in Federal Information Systems and Organizations.” This document details the testing and assessment procedures for the 18 security control families established in SP 800-53. Below is a small snippet of the security assessment procedures for the Personnel Termination security control, which resides in the Personnel Security family.
- Information system authorization: In the fifth step, organizations must authorize the operation of the information system and address the level of risk to the organization, individuals, its dependencies, and the nation as a result of the information system and determine if this risk is acceptable. Here, the organization identifies the security categorization of the information system and the weaknesses in the security controls protecting that system. They then address these risks and propose effective mitigation strategies. A risk assessment usually guides organizations through this process. Risk assessments are a key element in FISMA compliance. At this point in the process, the security controls can now be reviewed for the certification and accreditation. The guidelines for establishing the certification and accreditation of information systems is established in SP 800-37, the “Guide for the Security Certification and Accreditation of Federal Information Systems.” To be accredited and certified, the information system must have an acceptable risk level, a desirable level of security, and a mitigation strategy to address risks and vulnerabilities.
- Security control monitoring: The final step is a unceasing process that requires organizations to continually or at least annually monitor their selected security controls for FISMA compliance. Think of it as a periodic review of the controls to address their effectiveness, their state and any changes to the controls. Organizations usually look for assistance from SP 800-137, “Information Security Continuous Monitoring (ISCM) for Federal Information Systems and Organizations.” In this document, organizations are led through establishing and implementing an “Information Security Continuous Monitoring (ISCM)” program.
Concluding Thoughts
The NIST provides standards and best practices for security of information systems, assets, and processes. The NIST SP 800-37 (Revision 1), a “Guide for Applying the Risk Management Framework to Federal Information Systems,” is a helpful life-cycle approach that assists federal agencies and organizations in understanding how they can appropriately protect their information systems.
References
Cichonski, P., Millar, T., Grance, T., & Scarfone, K. (2012). Computer Security Incident Handling Guide (NIST Special Publication 800-61 Rev. 2). Retrieved from the National Institute of Standards and Technology Web site: https://nvlpubs.nist.gov/nistpubs/specialpublications/nist.sp.800-61r2.pdf
Dempsey, K., Chawla, N. S., Johnson, A., Johnston, R. Jones, A. C., Orebaugh, A., School, M. Stine, K. (2011). Information Security Continuous Monitoring (ISCM) for Federal Information Systems and Organizations (NIST Special Publication 800-137). Retrieved from the National Institute of Standards and Technology Web site: https://nvlpubs.nist.gov/nistpubs/Legacy/SP/nistspecialpublication800-137.pdf
National Institute of Standards and Technology. (2004). Federal Information Processing Standards Publication (FIPS PUB 199). Retrieved from the National Institute of Standards and Technology Web site: http://nvlpubs.nist.gov/nistpubs/FIPS/NIST.FIPS.199.pdf
National Institute of Standards and Technology. (2014). Framework for Improving Critical Infrastructure Cybersecurity (version 1). Retrieved from the National Institute of Standards and Technology Web site: https://www.nist.gov/sites/default/files/documents/cyberframework/cybersecurity-framework-021214.pdf
Swanson, M., Bowen, P., Phillips, A. W., Gallup, D., & Lynes, D. (2010). Contingency Planning Guide for Federal Information Systems (NIST Special Publication 800-34 Rev. 1). Retrieved from the National Institute of Standards and Technology Web site: http://nvlpubs.nist.gov/nistpubs/Legacy/SP/nistspecialpublication800-34r1.pdf
Ross, R., Swanson, M., Stoneburner, G., Katzke, S., & Johnson, L. (2004). Guide for the Security Certification and Accreditation of Federal Information Systems (NIST Special Publication 800-37). Retrieved from the National Institute of Standards and Technology Web site: https://www.fismacenter.com/SP800-37-final.pdf
Ross, R., Swanson, M., Stoneburner, G., Katzke, S., & Johnson, L. (2010). Guide for Applying the Risk Management Framework to Federal Information Systems: A Security Life Cycle Approach(NIST Special Publication 800-37 Rev. 1). Retrieved from the National Institute of Standards and Technology Web site: https://nvlpubs.nist.gov/nistpubs/specialpublications/nist.sp.800-37r1.pdf
U.S. Department of Homeland Security. (2018). Federal Information Security Modernization Act. Retrieved from the U.S. Department of Homeland Security Web site: https://www.dhs.gov/fisma
U.S. Legal. (2016). E-Government Act Law and Legal Definition. US Legal, Inc. Retrieved from https://definitions.uslegal.com/e/e-government-act/

