The defense in-depth design is a security philosophy that proposes we protect our assets and networks with multiple levels of security. The idea is not strictly limited to technical security controls, as management and operational controls have their rightful place in the defense in-depth approach. However, many aspiring and enthusiastic young learners falsely attribute the defense in-depth philosophy to purely physical security devices, such as firewalls, IDS/IPS, UTMs, proxies, etc.
Firewalls appear to be excessively relied on in the defense in-depth strategy. This in turn creates an environment that lacks other well-qualified and superlative controls. Nevertheless, firewall topics are one of the first things new cybersecurity students learn about in their journey through network security. In this regard, firewalls are absolutely important, but they should not be solely relied upon.

Not all firewalls are created equal. There are many different types, as you’ll see momentarily.
Hardware vs. Software
A firewall can be a dedicated hardware-based appliance, such as the very popular Cisco firewalls or the very expensive Palo Alto Networks firewalls. These devices are usually installed on the network perimeter, either behind or in front of a router. Often times, the firewall is installed on the router itself. They are also routinely used to create demilitarized zones (DMZs), which protect the internal network from public-facing assets. There are plenty of different firewall architectures, and some of which I will cover here in this blog post.
As an alternative, firewalls can be software-based. If you’re on a Windows system, like I am, your operating system comes with a software-based firewall called the “Windows Firewall.” In Windows 10, it’s called the “Windows Defender Firewall.” Software-based firewalls don’t protect a network, but rather only the system they are installed on.
Network-based vs. Host-based
A “network-based” firewall is typically the standalone, hardware appliance discussed above. They are usually located at the gateways or perimeter of a network. They commonly filter in-bound traffic entering the internal network. Since the amount of traffic that enters a network can be vast, network-based firewalls must be able to handle high amounts of bandwidth.
On other hand, a “host-based” firewall is software-based. They are installed on a particular system, such as a desktop, laptop, or server. Again, they are only intended to protect the system they are installed on.
Firewall Policies
The “firewall policy” reveals how a firewall truly works. It is the same thing as an “Access Control List (ACL),” or a matrix identifying acceptable and unacceptable traffic flows. When a packet arrives at a firewall, it must pass through a firewall policy inspection in order for the firewall to apply an appropriate action.
An “action” is the behavior the firewall performs. Actions are typically accept, deny, or log the packet. Being an ACL, the firewall policy is simply a list of rules that consists of something called “tuples.” These tuples are what make up the fields in a firewall policy. As you can see in the image depicted below, this firewall policy has the following tuples: Protocol, Source IP address, Source Port, Destination IP address, and Destination Port. The actions are ACCEPT or DENY.
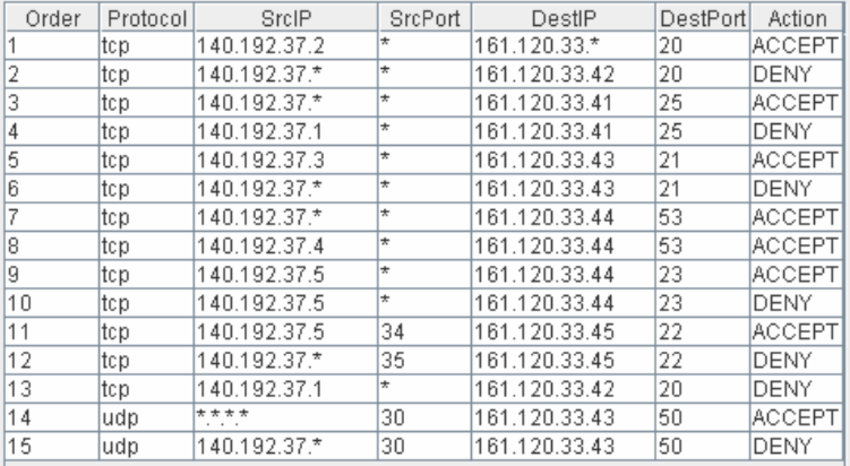
An example of a firewall policy. Reprinted from “PolicyVis: Firewall Security Policy Visualization and Inspection,” by Boutaba, R., Tung, T., & Al Shaer, E. (2007).
By all means, this is certainly not what all firewall policies look like, especially modern firewall policies. They do, however, share very common characteristics. The first rule in the firewall (order #1) accepts all TCP traffic coming from source IP address 140.192.37.2 on any source port to the destination network address 161.120.33.0 on destination port 20 (which is FTP).
Firewalls typically follow a “first-match” policy, meaning a packet is compared to each rule in the ACL until it matches the first rule in the list. For example, if a packet, doesn’t match rule #1, it will move on to rule #2. It will continue down the list until it matches a rule. Although the packet might have other sequential rules that it matches with, the firewall will only perform the appropriate action to the first rule it matches. This is in contrast to a “last-match” policy, which alternatively uses the last rule that the packet matches. Another type of policy is the “best-match” policy. This policy chooses the rule for the packet that more accurately matches the the tuples in the rule.
Unlike the firewall policy depicted above, most firewalls have an “implicit deny” rule at the bottom of the list. This is also referred to as a “catch-all,” “deny all,” or “default rule.” When you buy a firewall, they are configured to deny all traffic by default. It is only until a firewall administrator adds explicit allow/deny rules to the firewall policy that the firewall appropriately performs its duties. The implicit deny is often left at the end of the list. In this regard, any packet that has not matched to a rule will be denied and rejected. This is a safety precaution that all firewall policies should have.
Firewall Classes
There are generally 4 classes of firewalls: stateless, stateful, application-layer, and next-generation firewalls (NGFWs). In order to understand how these different classes of firewalls work, it’s important to know the Open Systems Interconnection (OSI) model and it’s 7 layers. Some classes of firewalls operate at specific layers. Refer to the image below.
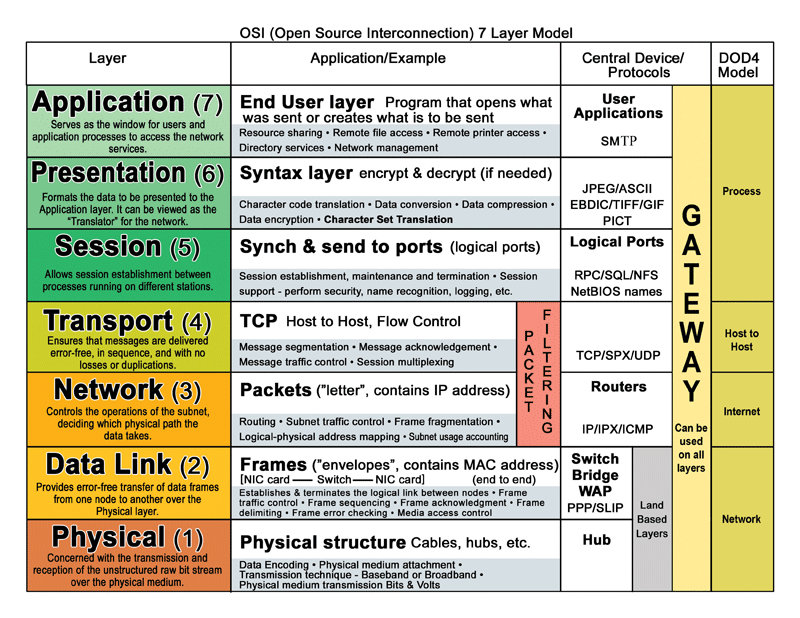
The OSI model consists of 7 layers: Physical, Data Link, Network, Transport, Session, Presentation, and Application.
Stateless Firewalls

Stateless Firewall. Reprinted from “Firewall Basics,” by Goldman, J. E., 2006
A “stateless” firewall is nothing more than a packet filter. It is said to be stateless because it is not aware of the state of a current connection. Stateless firewalls only operate at the Network layer; therefore, they only filter packets based on IP addresses, which is very similar to a router.

Because it’s very easy to spoof an IP address, stateless firewalls aren’t really used in modern network security. Stateless firewalls are primitive, and as a result, they are classified as “first-generation” firewalls.
Stateful Firewalls

Stateful Firewall. Reprinted from “Firewall Basics,” by Goldman, J. E., 2006
A “stateful” firewall works exactly the same as a stateless firewall; however, it works at the Network layer, Transport layer, Session layer, and Application layer. This allows the firewall to filter incoming and outgoing traffic based on source/destination IP addresses, source/destination port numbers, protocol, and TCP flags. This also allows them to track the state of a connection and record it in a “dynamic state table.” With stateful firewalls, we can now track the session between two communicating devices. Stateful firewalls are said to be “true” firewalls and are classified as “second-generation” firewalls.
Application-Layer Firewalls

Application-Layer Firewall. Reprinted from Reprinted from “Firewall Basics,” by Goldman, J. E., 2006
An “application-layer” firewall operates at the Application layer, which filters traffic based on the services and applications. Application-layer firewalls are capable of “Deep Packet Inspection (DPI).” This allows the application-layer firewall to examine the entire contents of a packet. This is commonly performed with the help of a proxy server. Proxy servers sit between a requesting device (client) and a servicing device (server). When a client wishes to make a request to a server, it must go through the proxy. The proxy terminates this connection and makes the request to the server on behalf of the client. This allows the proxy to inspect the contents of the packet.
“Web Application Firewalls (WAFs)” are a type of application-layer firewall, but they specifically filter web content by filtering HTTP traffic. Common WAFs include Imperva’s SecureSphere, Trustwave’s ModSecurity, and NBS System’s NAXSI. Due to their ability to inspect applications and DPI capabilities, application-layer firewalls are classified as “third-generation” firewalls.
Next Generation Firewalls (NGFWs)
The “Next Generation Firewalls (NGFWs)” can perform all of the aforementioned firewall functions, but they include important improvements, such as an IPS engine. IPS stands for “Intrusion Prevention System,” meaning NGFWs can look for indicators of an attack and prevent them from occurring. They are also commonly cloud-based, which allows for the NGFW to share signatures with other firewalls of the same vendor. NGFWs can even be used in conjunction with Active Directory and policy servers. Check Point, Cisco, and Palo Alto Networks all make great NGFWs.
Firewall Architecture
As I previously mentioned, there are many different ways to implement a firewall architecture on the network. I’m going to cover some basic designs below.
The Perimeter Firewall Architecture
This is the traditional perimeter firewall security design. All firewalling is performed at the edge of the network. In this architecture, the firewall is placed before the router. The scheme follows internal network>firewall>router. Or it can be internal network>router>firewall.
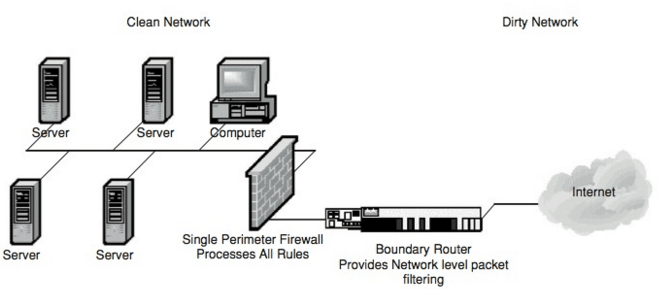
The Perimeter Firewall Architecture. Reprinted from ” Firewall Architectures,” by Goldman, J. E. (2006).
Server/Host Firewall Architecture
In this architecture, a firewall is protecting an important server. This firewall is either a dedicated hardware device or host-based, hence the name “server/host” firewall architecture. You can see that the perimeter firewall architecture is also being implemented in the network design, depicted below.
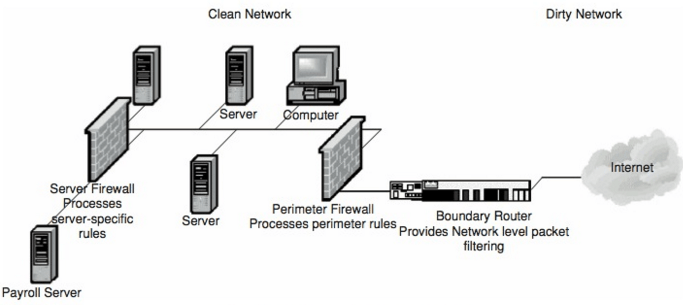
The Server/Host Firewall Architecture. Reprinted from ” Firewall Architectures,” by Goldman, J. E. (2006).
Screened Subnet Firewall Architecture
The “screened subnet” firewall architecture adds an additional firewall after the perimeter firewall. This creates a DMZ between the two firewalls where internet-based applications and services can reside (e.g., VPN server, remote access server, E-mail server, and Web server). The DMZ is protected by the perimeter firewall and the internal network is protected by the DMZ firewall. If, for example, the Web server was infected with malware, the infection would be contained inside the DMZ and not spread into the internal network.
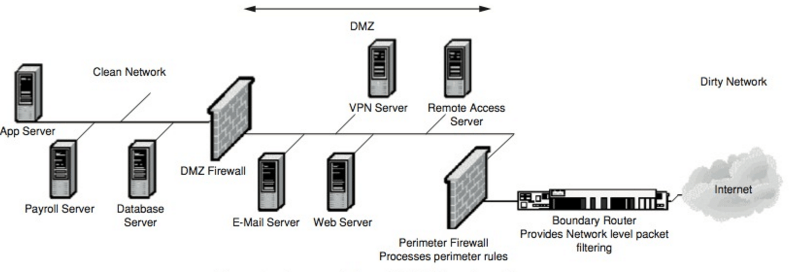
The Screened Subnet Firewall Architecture. Reprinted from ” Firewall Architectures,” by Goldman, J. E. (2006).
Multi-tiered/Distributed DMZ Architecture
The “multi-tiered/distributed DMZ” firewall architecture is used to create multiple DMZs in order of ascending security (tier 1, tier 2, and tier 3, respectively). This architecture is great for e-commerce environments. Only certain requests can travel through these firewalls. And, only very specific requests will be able to reach the Tier 3 DMZ where the transaction database servers are stored.
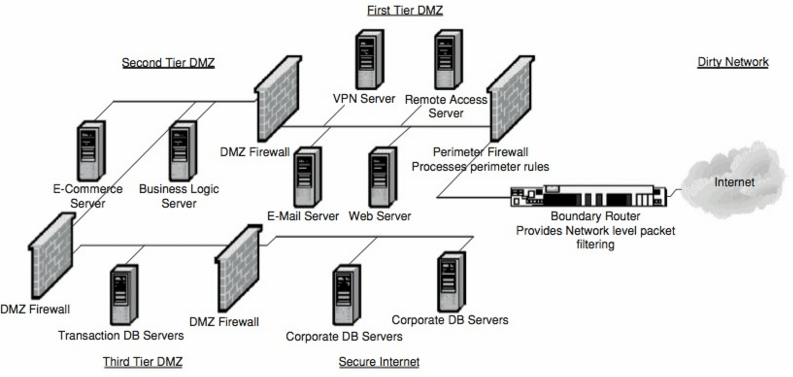
The Multi-Tiered/Distribution Firewall Architecture. Reprinted from ” Firewall Architectures,” by Goldman, J. E. (2006).
Conclusion
In general, firewalls are a great security tool to have, but to reiterate on my first point, they should not be solely relied on. This often creates a “Single Point of Failure (SPOF).” As we saw, firewall policies take a lot of configuration and misconfigurations are to be expected. Likewise, not all firewalls are built equally. It takes a particular firewall to get a job done, and some are better-suited for the task at hand.
I hope that this was a good introductory experience because there are many more things to know about firewalls. For example, there are even “virtual firewalls,” which can be used to centrally manage other distributed firewalls.
References
Fulp, E.W. (2013) Online Chapter 29: Firewalls. In Vacca, J.R. Computer Information and Security Handbook.
Goldman, J.E. (2006) Firewall Basics. In H. Bidgoli. Handbook of Information Security
Goldman, J.E. (2006) Firewall Architectures. In H. Bidgoli. Handbook of Information Security
Maymi, F. J., Chapman, B. (2018). All-in-One CompTIA CSyA+ Cybersecurity Analyst Certification Exam Guide CS0-001. McGraw-Hill Education: New York, NY.

