In this blog post, I’ll discuss the design and operation of a 4G LTE network. In hindsight, I realize topics such as these can get extremely lengthy. For that reason, I’ll limit this discussion down to only the necessary technical details required to understand these new LTE attacks, while excluding any complicating, non-essentials. These new attacks against LTE come straight from two hard-working teams of researchers, specifically, Rupprecht, Kohls, Holz, & Popper (2018) and Hussain, Chowdhury, Mehnaz, & Bertino, (2018). These researchers come from varying educational backgrounds, including Purdue University, the University of Iowa, Ruhr-University Bochum, and New York University.
In this discussion, I discuss the recent vulnerabilities and attacks against the 4G LTE network. You’ll learn some fundamentals in the LTE network architecture, attachment/detachment procedures, paging procedures, cell site anatomy, and the LTE protocol stack. And of course, I’ll be discussing the following attacks near the end:
- Identity Mapping attacks
- Web Site Fingerprinting attacks
- DNS Redirection attacks (AKA aLTEr attacks)
- Authentication Synchronization Failure attacks
- Traceability attacks
- Numb attacks
- Authentication Relay attacks
- Paging Channel Hijacking attacks
- Stealthy Kickoff attacks
- Panic attacks
- Energy Depletion attacks
- Detach/Downgrade attacks
I’ll also be discussing the practicality of these attacks as well as any available defenses.
4G LTE
When you’re at home, Wi-Fi handles all your wireless data transmission on your smartphone. But, when you’re not relying on Wi-Fi, all your mobile voice and data use traverses the wireless, cellular network instead. So, when you’re out-and-about, you can pull out your smartphone and stream music and video relatively quickly so long as you’re within range of a cell tower. How convenient is that? How different would mobile networking be today if we couldn’t access the Internet from our smartphones and other mobile devices? Have you ever even wondered how LTE works?

These days, we’re using Long Term Evolution (LTE), which is a type of 4G technology based on GSM. Since its release in 2010, it now dominates wireless services because it offers 300 Mbps of download speed and 75 Mbps of upload speed; however, practically, you won’t see such high speeds. Previously, we relied on GSM (a 2G technology), CDMA (also a 2G technology), and HSPA+ (a 3G technology). But, because LTE defined higher speeds, full-time Internet connections, and didn’t require Carriers to install a completely new infrastructure (backwards-compatibility), it is predominantly what we use today.
Unfortunately for mobile users, which is all of us, researchers have uncovered several vulnerabilities in the LTE standard that could allow sophisticated hackers, or even government agencies, to spy, modify, and re-route cellular communication. More specifically, researchers have demonstrated several attack vectors that allow them to intercept phone calls and text messages, spoof locations, re-route victims using DNS spoofing, knock devices offline, redirect data, modify data, and even send out fake emergency alerts.
But, will you really understand how these LTE attacks work if you don’t understand the LTE network architecture? I don’t think so. For that reason, here’s a short, yet impactful primer on the 4G LTE network architecture.
The LTE Network Architecture
The LTE network architecture consists primarily of 3 main components.
- User Equipment (UE): This is the cellular device, such as the user’s smartphone. Every smartphone contains a SIM card, which stands for a “Subscriber Identity Module.” Every SIM card stores a few important things other than contact information. Each SIM card has its very own “International Mobile Subscriber Identity (IMSI)” permanent number that is paired with crytopgraphic keys and an “International Mobile Equipment Identity (IMEI).” These numbers serve two important purposes. Number one, they allow your Carrier to identify who you are and, number two, they allow you to authenticate to the LTE network. Exposing the IMSI and the EMEI may leave a user susceptible to impersonation attacks, which I’ll discuss later. The UE also has a few temporary identities while it’s connected to the network, a few important ones being the “Radio Network Temporary Identity (RNTI),” the “Globally Unique Temporary Identity (GUTI),” and the “Temporary Mobile Subscriber Identity (TMSI).”

UE includes your mobile devices
- E-UTRAN: This is the radio-access network, which serves as the intermediary network between the UE and the EPC (discussed next). The E-UTRAN serves a geographical area of mobile users. LTE networks are partitioned into hexagonal cells, each serviced by a base station (e.g., cell site, cell tower, or eNodeB). These base stations service the mobile users that reside in these hexagonal cells and pass along their information to the EPC.

Each base station serves a hexagonal, geographical area.
- Evolved Packet Core (EPC): This is the core network. Cell sites contain equipment shelters that house the “Back-Haul” equipment, which serve as an intermediary link between the EPC and the landline connections. Typically, a fiber-optic line carries messages down a cell tower to a wireless access point, which then connects to a powerful multi-port switch, router, or other networking equipment. It’s usually then routed through an underground T1 or T3 line; however, it’s also possible for it to travel back up the cell tower and through a powerful microwave antenna for wireless transmission. The EPC has several components. The “Mobile Management Entity (MME)” is responsible for managing UE authentication/de-authentication and key agreement to-and-from the LTE network. It’s also responsible for tracking the user’s location. The “Home Subscriber Server (HSS)” stores the user’s identity. This would include the UE’s IMSI and EMEI, as well as any cryptographic keys. Finally, there are two gateways: the “Serving Gateway (SGW)” routes packets and the “PDN Gateway (PGW)” connects the mobile user to external packet networks.
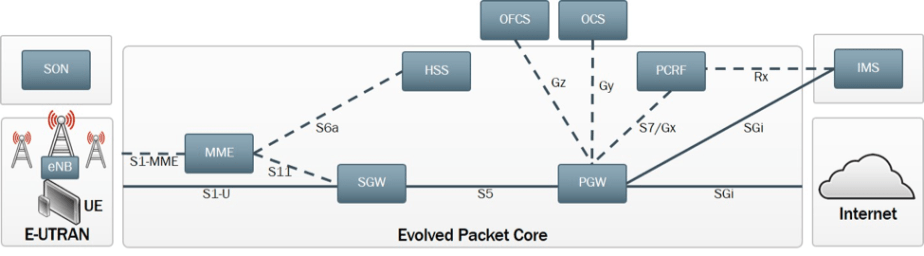
The EPC serves as the intermediary between the E-UTRAN and the Internet.
There are more, components, but they are not essential for this discussion.
Cell Site Anatomy
A “cell site” consists of a tall mass or tower, typically mounted with antennas for transmitting and receiving information from mobile devices. There could be anywhere from 3 to 18 antennas on one tower. The combination of multiple connected antennas creates an “antenna array.” Interestingly, cell sites are sometimes shared amongst different Carriers; thus, a cell tower could hold several platforms at the top of the tower, each for a specific Carrier. When you make a phone call or request to a web server, these messages hit these antennas via radio waves. There may also be a circular, microwave “back-haul antenna” at the top, which serves as a wireless intermediary between the EPC and the subnetworks.

Antenna Array. Reprinted from “Giz Explains: How Cell Towers Work,” by Rothman, W., 2009.
The antenna array are connected to either copper or fiber-optic cables, which run down the tower into the network equipment at the bottom. Your data runs down this transmission medium.

Copper and Fiber-Optic Media. Reprinted from “Giz Explains: How Cell Towers Work,” by Rothman, W., 2009.
The equipment is usually stored in a highly-protected base station or locker. Inside, are tons of rack-mounted gear to route and transmit data, such as multi-model base stations, switches, routers, radio frequency amplifiers, and other mobile Carrier equipment.
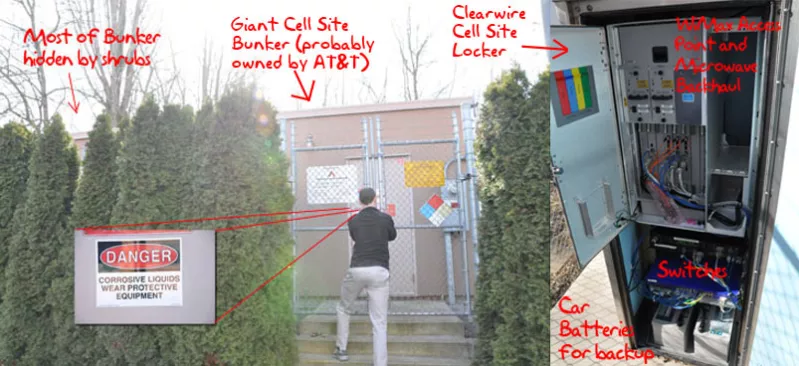
Cell Site Equipment. Reprinted from “Giz Explains: How Cell Towers Work,” by Rothman, W., 2009.
Cell sites also come with backup power supplies, including spare batteries and power generators that can keep the site running for an extra 24 hours just in case that particular region loses power for any reason.
LTE Attach/Detach Procedure
When a UE wishes to connect to the LTE network, such as when you power on your smarphone or turn off Wi-FI, the device scans for broadcast messages from surrounding base stations (AKA eNodeBs) in the area. In particular, these broadcasts are called “system_info_block” messages. After the UE determines which base station has the highest signal power, it establishes a connection with that base station. This is similar to how mobile devices connect to APs with the same SSID. Connection takes place in 4 stages:
- Identification: The UE sends an unencrypted “attach_request” message to the base station. This message contains the IMSI, EMEI, and supported cryptographic suites. This information is passed to the MME for processing and storage.
- Authentication: To verify authenticity, the HSS passes an “authentication_request” message to the MME and then forwards it to the UE. This message contains an authentication challenge to help prove the identity of the UE. The master key, stored in the UE’s SIM card, solves the authentication challenge. Upon completion, the UE replies with an “authentication_response” message
- Security algorithm negotiation: The MME chooses one of the cryptographic algorithm pairs that both the UE and MME can support and sends it in a “security_code_command” message that is integrity-protected via a Message Authenticity Check (MAC). After the UE verifies the message, the MME replies with a “security_code_complete” message. From there, the UE and MME generate cryptographic keys for protecting confidentiality and integrity of the future message exchanging.
- Secure temporary identifier exchange: In the final step, the MME sends an encrypted and integrity-protected “attach_accept” message to the UE, which that contains a “Globally Unique Temporary Identity (GUTI).” This is similar to the “Temporary Mobile Subscriber Identity (TMSI).” The GUTI is for the UE, and by using these temporary numbers for all subsequent communication, we can limit exposure of the IMSI and EMEI. After that, the UE sends an “attach_complete” message. The UE and base station then generate a pair of shared keys for encrypted communication. To detach from the base station, the UE sends a “detach_request” message and the MME should respond with a “detach_accept” message.
LTE Paging Procedure
After connection to the LTE network, the UE frequently updates the MME on its location through “tracking_area_update_request” messages. So, if you move too far, another base station can go to work. However, if no messages are being sent, the UE goes into “idle mode” in order to save energy. The UE will “wake up” upon receiving MME-initiated paging or eNodeB-initated paging
- MME-initiated paging occurs when the MME needs to locate the UE. This might happen if the MME needs to deliver an incoming call or SMS text message. The MME informs all base stations in the area (eNodeBs) to page the UE. Importantly, the paging message contains the GUTI and TMSI, but it can also contain the ISMI if there happened to be a network failure during the attach procedure. Fortunately, once a UE receives a paging message with its ISMI, it will detach itself from the network and re-connect to the LTE network, starting the attach procedure over again.
- eNodeB-initiated paging can occur without the MME when it needs to notify the UE about one of the following events: a change in the system, an emergency (e.g., amber alert), or an earthquake/tsunami warning.
The LTE Protocol Stack
The figure below displays an overview of the LTE protocol stack between the UE and the eNodeB (base station). There is a layer 1 – Physical, layer 2 – Data Link, and layer 3 – Network. They are just like the layers of the OSI model.
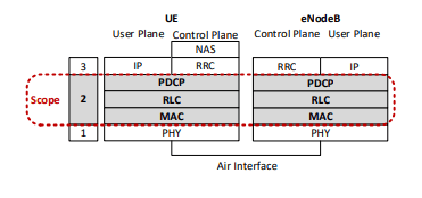
- The Physical layer: This layer is responsible for the physical transmission of data over the air using radio waves.
- The Data Link layer: Here is where most of the vulnerabilities lie. This layer Ensures a reliable message delivery in a way that provides both security and integrity of data. Just like the Data Link layer of the OSI model, the Data Link layer in the LTE protocol stack is subdivided. However, this model has three sublayers, not two. At the first sublayer, the “Medium Access Control (MAC)” protocol manages access to the radio resources of LTE. This task is accomplished using the UE’s unique RNTI. There is an inherent vulnerability in the way the RNTI is obtained, which can be used for identity mapping attacks. Number two, there is the “Radio Link Control (RLC),” which is responsible for error correction, segmentation, packet retransmission, and the assembly of data into the correct order of upper-layer packets. And, number three, the “Packet Data Convergence Protocol (PDCP)” protocol provides encryption and integrity protection for control plane messages to the Radio Resource Control (RRC) layer. Since this is the first layer where encryption begins, the payload and header information of all packets below this sublayer can be read. This can be exploited to complete a website fingerprinting attack and an aLTEr attack.
- The Network layer: This layer is similar to the Network layer in the OSI model; however, it is split into 3 sublayers. The “Non-Access Stratum (NAS)” layer is responsible for mobility with the core network. The “RRC sublayer” manages radio connections between the UE and the eNodeB. And, the “Internet Protocol (IP)” handles transmissions to overlying transport
protocols like TCP and UDP
LTE and ODFMA
LTE uses “Orthogonal Frequency Division Multiple Access (OFDMA),” a multi-user type of OFDM technology that splits one signal into multi-parallel data streams, each one on a separate frequency. OFDMA uses orthogonal sub-carriers, each spaced evenly at 15 khz. Each phone call gets its own separate frequency. Therefore, you can have thousands of phone calls served by one base station. And, because of the fact that these cub-carriers are orthogonal means that there is no cross-talk. It’s a little different than OFDM.

After spending some time explaining OFDMA, I’ve realized that you don’t actually need to know OFDMA to understand the LTE attacks. However, I’ll leave this section here anyway because it’s good to know.
LTE Attacks
The following sections discuss the vulnerabilities in the LTE network, which have allowed many teams of researchers to discover and develop multiple types of attacks that exploit these same vulnerabilities. The research comes from Rupprecht, Kohls, Holz, & Popper (2018) and Hussain, Chowdhury, Mehnaz, & Bertino, (2018).
Passive LTE Attacks
Passive LTE attacks eavesdrop on communication between the UE and the eNodeB (the base station). With passive attacks, an attacker can decode the signals being sent back and forth without any knowledge of the key material. In passive attacks, there is no interference with the LTE network; data is captured using sniffing software.
Identity Mapping Attack
This attack assumes the attacker does not know the RNTI or TSMI of the victim, but learns them through the initial radio connection establishment within the geographic boundary of the cell. During this connection establishment process, the UE sends a “Random Access Preamble (RAP)” to the eNodeB and receives back a “Cell Radio Network Temporary Identity (C-RNTI)” in the “Random Access Response (RAR).” This is a unique and temporary identifier that serves that particular radio session and it also identifies the UE on the MAC layer. After receiving the C-RNTI, the UE also sends an RRC connection request to the eNodeB, which includes the UE’s identity. This identity could be the TMSI or a random value if it does not already possess a TMSI. The connection establishment is complete when the eNodeB responds with the RRC connection setup message.

In an Identity Mapping attack, an adversary can either exploit the RRC connection request in the uplink direction or the RRC connection setup in the downlink direction. Using a sniffer, the adversary can intercept the RRC connection setup addressed to C-RNTI of the target UE that was learned from the RAR of the eNodeB. The TMSI assigned to the victim UE can also be learned from the RRC connection request. By combining both identifiers, an adversary can successfully match layer two and three identities. As long as the TMSI is valid, an adversary can specify and localize a specific user within the cell.
Web Site Fingerprinting Attacks
The researchers were also able to demonstrate web site fingerprinting attacks on LTE traffic inside an experimental network, making it more of a proof-of-concept attack rather than a practical attack. This type of traffic-eavesdropping and -analysis exploits the leakage of meta data on layer 2, specifically, at the PDCP sub-layer.

Despite the fact that the researchers were relatively successful in analyzing and guessing the traffic patterns of specific web pages, there are many limitations to this attack. The researchers grant that “our measurements are biased towards time, location, and network setup, e. g., we recorded all traces from a single position and in closed blocks with our experimental LTE network that is completely under our control.”
Active LTE Attacks
In Active LTE attacks, an adversary must inject malicious messages or signals onto the network or toward the victim.
DNS Redirection Attack (AKA aLTEr attack)
This is perhaps the most dangerous attack. A DNS Redirection attack intercepts and modifies the destination IP address of a DNS request coming from the victim. The purpose of this attack is to re-direct the original DNS request to a malicious DNS server. With a DNS server under adversarial control, victims can be re-routed to harmful web sites that install malware or phishing sites that steal login information.
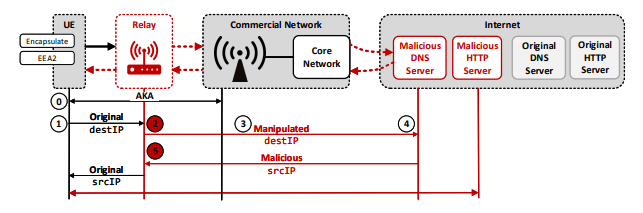
To perform this attack, an adversary sets up a MitM relay between the UE and the eNodeB. The researchers effectively use this malicious relay to cleverly emulate the eNodeB and the user simultaneously in order to intercept communications. When the victim UE sends a DNS request (e.g., when the device boots up, the user requests a web page, or an app contacts a server), the transmission is intercepted and the adversary applies a manipulation mask to change the destination IP address to that of the malicious DNS server. After that, the request is forwarded back to the victim UE on the LTE network. Keep this in mind: although the Data-Link layer of the LTE network encrypts the DNS UDP packet payload using AES in Counter mode (AES-CTR), it does NOT encrypt the destination IP address NOR keep it integrity-protected. This design flaw in LTE is why the researchers were able to perform this attack in the first place.
However, there are limitations to this attack. The researchers had to create a MitM relay that both emulated the eNodeB and the UE. In addition, they not only had to lure the victim to connect to the relay, but also ensure that there was a long-lasting, stable connection. One way to lure victims into connecting to the relay is by cranking up its transmission power in order to overpower the commercial, legitimate eNodeB for that cell. The researchers also had to somehow distinguish DNS request packets from other transmissions. Even though DNS payloads are encrypted, the researchers could overcome this limitation by identifying packets through their length. This is because DNS packets are smaller than other TCP packets. There are also IP and UDP checksum verifications that must be bypassed too.
Authentication Synchronization Failure Attack
This attack occurs during the LTE attach procedure. Specifically, it exploits the UE’s sequence number sanity check in order to cause a denial of attach or denial of service. This is done by sending successive attach_request messages that contain different cryptographic suites to the UE. This somehow interrupts the authentication process in step 2 of the LTE attach procedure in which the HSS is supposed to send an authentication_request.

In this case, the researchers state that “in accordance to subclause 5.5.1.2 of 3GPP standard, the previously initiated attach procedure is aborted and the new attach request message is processed (including, the increment of the sequence number).” Even if the EPC re-synchronizes with the UE, the adversary can simply continue repeatedly sending successive attach_request messages in order to make the UE and the HSS sequence numbers to go out-of sync again.
Traceability Attack
This attack tracks the UE by exploiting responses of security_mode_command messages. This is something I have not discussed yet, but these particular messages are exchanged during the attach procedure in order to negotiate cryptographic suites between the UE and the MME. The security_mode_command message is sent from the MME to choose a UE-supported cryptographic suite. Once that is finished, the UE responds with a security_mode_complete message.
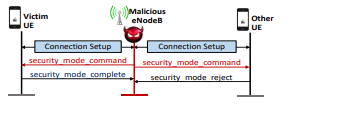
In the Traceability attack, an adversary sniffs for the previous security_command_message sent between the UE and the eNodeB during the previous attach procedure. The adversary then uses a malicious eNodeB to re-broadcast this message to all UEs in the cell. The UE should then respond back with a security_message_complete after verifying the integrity of the message; however, all other UEs in the cell should respond with a security_mode_reject due to MAC failure (integrity check failure). This attack allows the adversary to track a particular UE in the cell.
Numb Attack
This attack injects an out-of-sequence control-plane protocol message in order to disrupt the UE. This also requires that the adversary set up a malicious eNodeB. Once the UE attempts to connect, the malicious eNodeB replies with an auth_reject message to disrupt service.
Authentication Relay Attack
Another dangerous attack! The purpose of this attack is to impersonate the victim UE in order to gain unauthorized access to the EPC. This is accomplished by first setting up a malicious eNodeB with a high signal power as well as a fake UE. The next step is to kick the victim UE off the legitimate eNodeB by using a type of paging attack or detach attack (discussed later). Once the victim UE is kicked off, it will automatically attempt to connect with the malicious eNodeB because it has a higher signal strength.
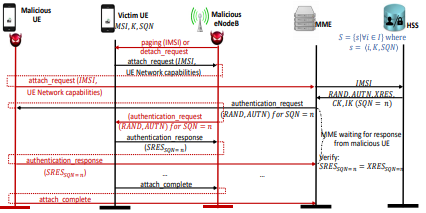
The victim UE then sends an attach_request message to the malicious eNodeB, which is then forwarded by the adversary to the fake UE. The fake UE then forwards this same attach_request message to the legitimate UE. The MME should then respond with the authentication challenge by sending it to the legitimate eNodeB and then to the fake UE.
Obviously, the fake UE cannot complete this authentication challenge; therefore, the fake UE forwards it to the malicious eNodeB, which it then forwards to the victim UE. The victim UE completes the authentication challenge and sends the correct response back to the malicious eNodeB. And finally, the malicious eNodeB forwards the response to the fake UE so it can present it to the legitimate eNodeB. This completes the authentication process.
This attack is very deceptive and truly dangerous. If successful, the adversary can poison the location history of the victim UE, compromise the confidentiality of data, cause complete or selective DoS, and profile the victim UE’s service usage.
Active LTE Paging Attacks
In Active LTE Paging attacks, an adversary somehow compromises the paging procedure. Pages are messages sent from the eNodeB or MME to the UE. The purpose of pages are for locating the UE and sending phone calls/SMS text messages.
Paging Channel Hijacking Attacks
This attack hijacks the UE’s paging channel by using a malicious eNodeB operating in the same frequency as the legitimate eNodeB. The attack is a little more complicated than simply broadcasting fake pages to the UE as a Paging Channel Hijacking attack requires the malicious eNodeB’s paging cycle to synchronize with the victim UE’s paging cycle. Also, seeing as both the legitimate and malicious eNodeB will be broadcasting pages at the same time, the adversary must ensure that his pages are broadcasted with a higher signal power. This should ensure that the paging channel is hijacked and the UE will not receive any legitimate pages from the eNodeB. Without legitimate pages to wake the UE, it will not receive phone calls or SMS text messages.
Stealthy Kick-Off Attacks
The prerequisite for this attack is to hijack the UE’s paging channel using the Paging Channel Hijacking attack. Once this is complete, the adversary sends a modified paging message that contains the UE’s IMSI. Recall that when a UE receives its IMSI during the paging procedure, it must disconnect and re-attach to the network in order to receive a temporary identity that won’t expose the IMSI.
Upon receiving the fake page with the UE’s IMSI, the UE detaches itself from the network and sends an attach_request message to the malicious eNodeB. As we can see, the Stealthy Kick-Off attack silently kicks a UE off the network.
Panic Attacks
This attack is quite simple. In a Panic attack, a malicious eNodeB broadcasts fake pages that contain emergency warnings to all UEs in the cell. This is done repeatedly to ensure that all UE’s receive the fake emergency warnings. The implication of this attack is to cause hysteria, confusion, and panic.
Energy Depletion Attack
This attack depletes the UE’s battery by forcing it to conduct exhaustive cryptographic operations. Since the majority of cryptographic operations occur during the attach procedure, it makes sense to force the UE to repeatedly perform the resource-expensive attach procedure over-and-over again.
Active LTE Detach Attacks
These are attacks that disconnect mobile users from the LTE network.
Detach/Downgrade Attack
This attack is similar to the Numb attack. It requires the setup of a malicious eNodeB and also requires that the adversary learn the IMSI of the UE. This attack is also quite simple. While the UE is connected to the malicious eNodeB, it can learn the IMSI by sending identity_request (IMSI/IMEI) message to the victim UE. The victim UE should then respond with its IMSI. The adversary then sends a fake detach_request message to the UE, which forces the UE to send a detach_accept message. This knocks the UE off the malicious eNodeB. This primarily focuses on service disruption; however, a Detach/Downgrade attack can be paired with other attacks, such as an impersonation attack.

The Practicality of These Attacks
Most of these attacks aren’t very practical for run-of-the-mill hackers. Exploiting these LTE vulnerabilities require extensive resources and many ordinary hackers haven’t spent a lot of their time studying these giant wireless networks. Therefore, only sophisticated hackers, state-sponsored hackers, and government agencies would be capable of carrying out these types of attacks.
We should also consider the fact that these attacks were tested and demonstrated in a controlled lab environment. Therefore, it would be much harder to successfully perform these attacks out in the wild. In particular, the more dangerous attacks discussed here seem much harder to perform. However, if these attacks were to be attempted, an adversary would most likely aim for high-profile targets, such as politicians or celebrities.
Defense Against LTE Attacks
Defending against these attacks will prove difficult because we’re looking at inherent vulnerabilities in the LTE protocol stack itself. Simply patching these vulnerabilities could break backwards-compatibility and lead to ineffective, temporary solutions. What will really defend against these attacks is a major infrastructural or protocol redesign that will update the specification. However, this would be extremely costly and lead to a lot of overhaul.
A more feasible alternative would just be to protect yourself from the more dangerous attacks. For example, DNS spoofing and redirection attacks will often lead victims to an unsecured site that steals login credentials. This can be avoided if users remain vigilant and periodically check the URL bar for “https,” signifying a secure SSL connection to the Web server. Web browsers and Web servers should also be supporting HSTS in order to protect against any downgrading attacks.
Likewise, as we always should be doing for open wireless networks, use a VPN. VPN tunnels add an additional layer of protection by keeping your traffic encrypted and integrity-protected on open wireless networks.
5G Complications
5G should begin the rolling out process next year, but 5G networks may also be vulnerable to the aforementioned attacks as well. What’s also troubling is that many major Carriers, such as AT&T and Verizon have already begun implementing the 5G protocol.
References
Hussain, S. R., Chowdhury, O., Mehnaz, S., & Bertino, E. (2018). LTEInspector: A Systematic Approach for Adversarial Testing of 4G LTE. 10.14722/ndss.2018.23319.
Jones, D. (2010). Evolved Packet Core. Light Reading. Retrieved from https://www.lightreading.com/document.asp?doc_id=679971
Rothman, W. (2009). Giz Explains: How Cell Towers Work. Gizmodo Media Group. Retrieved from https://gizmodo.com/5177322/giz-explains-how-cell-towers-work
Rupprecht, D., Kohls, K.,Holz, T., & Pöpper, C. (2018).Breaking LTE on Layer Two. IEEE Symposium on Security and Privacy (SP), San Fransisco, CA, US, , pp. 6.
doi:10.1109/SP.2019.00006

“Keep this in mind: although the Data-Link layer of the LTE network encrypts the DNS UDP packet payload using AES in Counter mode (AES-CTR), it does NOT encrypt the destination IP address NOR keep it integrity-protected. This design flaw in LTE is why the researchers were able to perform this attack in the first place.”
this is essential pice but false. see 3gpp 36.323 ch 5.6. the data link layer (PDCP) is ciphering whole SDU keeping only PDCP headers as unciphered. good luck with aLTEr attack…only in your lab where ciphering alg is set to NULL. please do not spread that bulshit.
LikeLike
Read the next paragraph. Thanks. Also, tell the researchers. Not me.
LikeLike