With Shodan, there’s no hiding on the Internet. Shodan is a search engine that allows users to locate devices that are connected to the Internet, such as webcams, routers, servers, traffic lights, baby monitors, SCADA systems, Internet of Things (IoT) devices, and so forth. Shodan began back in 2009 as a small project created by John Matherly, but quickly grew in popularity as an increasing number of devices and computer systems began connecting to the Internet over the years, many of which with little-to-no security. As is often the case, many of these Internet-connected devices come with a web console for login and management purposes; therefore, all that is required to access these devices is a Web browser. Furthermore, many of these devices are left online with default usernames and passwords that can be easily guessed or quickly searched for online.
How Shodan Works
Shodan crawls the Internet searching for online devices; however, it does not work by indexing “content.” Instead, it uses a process called “banner grabbing” in order to gain information about the specific device. “Banners” are nothing more than configurable, text-based information that display a whole lot of system information, including the operating system, version, services, domain names, hostnames, error messages, organizations, country, port numbers, passwords, and other parameters. Online devices advertise these banners. This information is useful for network administrators, but also useful for a hacker who’d like to discover any vulnerable software or services running on that system. For that reason, banners are often disabled or configured to provide minimal information.
That is how Shodan works. It grabs these banners by accessing all 4.3 billion IPv4 addresses and returns the results. It might seem like this is unlawful, but Shodan is frequently used by cybersecurity professionals, researchers, and law enforcement for legitimate reasons. On the other hand, Shodan is acutally used by hackers in search for online systems to exploit.
Shodan
When using Shodan, it’s better to register an account with the service. This is because users without an account will be limited to smaller search results and filters. Registration is free, but if users want the full experience of Shodan, they will have to pay a fee. This could range from $59 per month to $899 per month. However, this is not necessary for this discussion. Below is a screenshot of the Shodan homepage.

There are a few options here. Let’s go through each one of the tab options that are located to the right of the search bar. These options include, “Explore,” “Downloads,” “Reports,” “Developer Pricing,” “Enterprise Access,” and “Contact Us.” The Explore tab is the most useful tool relevant to this discussion. The other tabs are for frequent Shodan users.
Using Explore in Shodan
The Explore tab is pretty useful. By navigating to the Explore page, users can review popular searchers that other Shodan users have created. On the Explore page, users can choose among featured categories, such as ICS, databases, and video games. For instance, choosing the video game category gives Shodan users the option to analyze video game servers. This means that if a user chose Minecraft, as an example, the user could perform a quick analysis of Minecraft servers on the Internet, including which mods are installed, how many players they allow, and where they are located.

Shodan users can also review Top Voted results on the Explore page, which is usually something to do with cameras. From what we can see above, the top 3 results include Webcams, cams, and netcams. Clicking on any one of these options will bring the Shodan user to a list of online cameras, which may even allow the user to remote access.
Regardless of what the Shodan user chooses on the Explore page, there will be hundreds of results to review. I’d highly recommend picking interesting topics and just get a feel of how Shodan works.
Shodan Search Bar
Let’s try using the search bar on the Shodan home page. Shodan users have endless search options. For example, users can search for all different types of online Web servers, such as Apache, IIS, and Nginx servers. Users can also search for millions of connected routers, including the very popular Cisco routers or Netgear routers. What happens to be really popular are webcam searches. There are many Webcam manufacturers, such as Axis, Samsung, Sony, Toshiba, Vivtek, and WebcamXP.
WebcamXP webcams are often unsecured and usually come with a blank default password; therefore, accessing the web console of one of these online cameras would likely allow the user to see a live video feed. Let’s search “WebcamXP” in the search box.
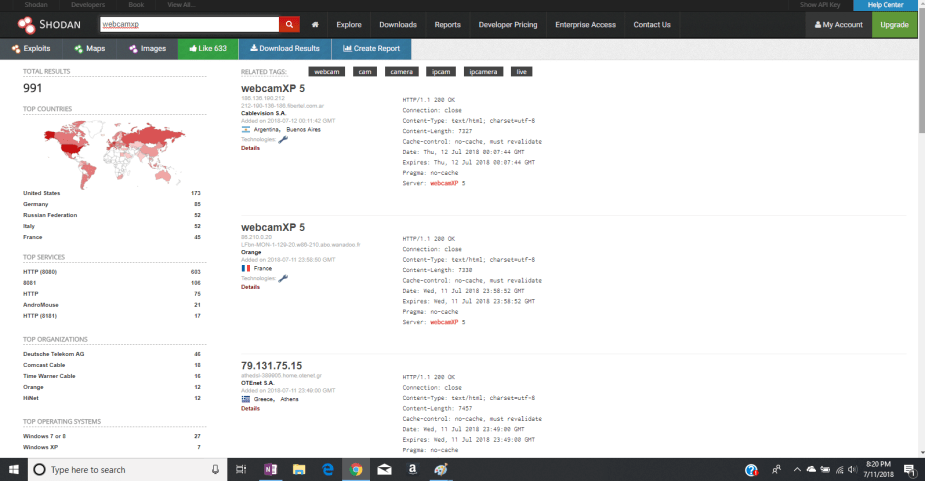
Since I’m a non-paying Shodan user, my search is limited to 991 results. Each individual result shows the banner information of the webcamXP camera, including its IP address, location, and other useful parameters. Here is an office webcam located in the United States. I’ve cropped out the city location, IP address, and banner information for privacy reasons.
With access to the Web console, a Shodan user has the ability to login to the webcam, which I’m not going to do. Shodan users can test various default login credentials in order to gain unauthorized access. Once logged in, they gain administrative privileges to move the camera, zoom-in, zoom-out, take snapshots, change the video quality, and much more.
Here is another livefeed webcam located in the United States. Again, I’ve blocked out the city location, IP address, banner information, and faces of any individuals in the feed (except for the dog of course). Speaking of dogs, are you a cat person or a dog person? Here’s a webcam that’s monitoring a dog park.
I hope this highlights the importance of securing your devices, especially when they are attached to the Internet. When someone buys a device, such as a camera or network equipment, the manufacturer installs a set of default credentials that allow the customer to login to their new device. It is up to the customer to change these default credentials soon after purchase because sticking with the defaults is bad security. Default usernames to hundreds of security camera manufacturers and brands are available at www.a1securitycameras.com.

But, remember, Shodan isn’t only good for security cameras. It’s also a place to find unprotected web servers, game servers, routers, and much more.
Search Queries
To get the most out of Shodan, it’s good to understand the search syntax. However, only registered Shodan users may use the search syntax. Paying users get to use more of these filters. These filters are extremely useful for narrowing down search results. As a paying Shodan user, there may be millions of search results! Below are some common filters to use:
- city: find devices in a particular city
- country: find devices in a particular country
- geo: you can pass it coordinates
- hostname: find values that match the hostname
- net: search based on an IP or /x CIDR
- os: search based on operating system
- port: find particular ports that are open
- before/after: find results within a timeframe
As an example, if I wanted to find webcamxp cameras in the United states and the city Indianapolis only, I would use the search string “webcamxp country:us city:indianapolis.”

These strings are really easy to use and remember. They’re nothing like Wireshark filters, which can be annoying to remember.
Using the Map
If you didn’t already notice, there is a “Maps” option underneath the search bar. Shodan users can click this to produce a helpful map of the globe or particular region they are interested in.
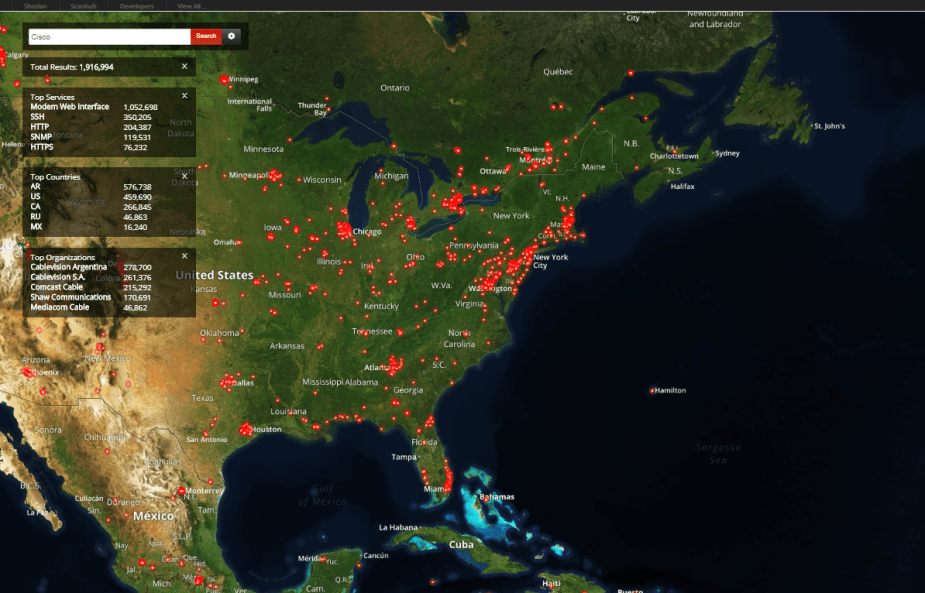
This map above shows a map of Cisco devices in North America. Realistically, there are much, much more, but I don’t have a premium account. Each one of the red dots are clickable and they will bring you to the banner information.
Shodan Exploits
Before I begin with this section, understand that accessing or manipulating systems that you do not have authorized access to is illegal. Under the search bar is an option called “Exploits.” This page will display known vulnerabilities and exploits to the system a Shodan user has searched for, such as Cisco routers. The information comes from multiple sources, such as CVE and Metasploit.

Here’s a random exploit I chose from 2002 that affects some very old Cisco routers with CVE identifier CVE-2002-2315. Because these older routers don’t limit the size of their redirect table, hackers can cause a DoS by sending a large amount of spoofed ICMP redirect messages.
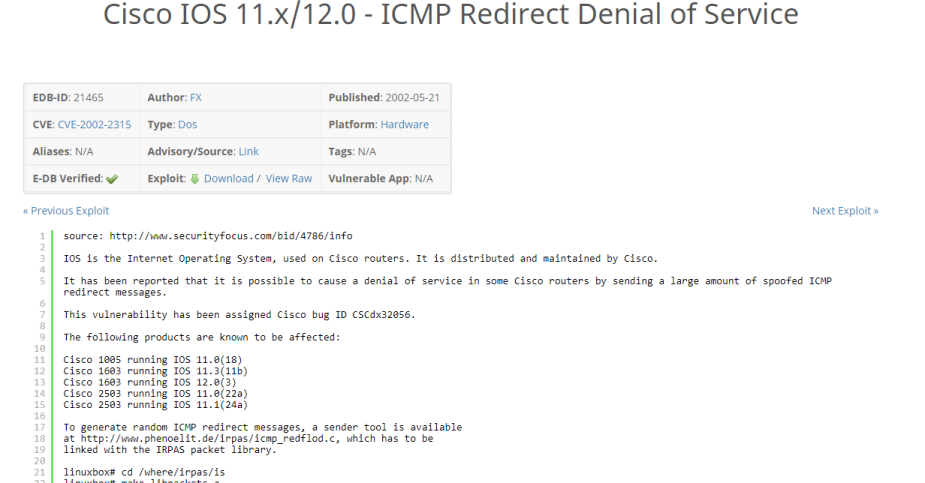
This vulnerability has likely been patched, but it wouldn’t matter anyway considering these routers are now obsolete. But, this is one of the potentials of Shodan. Users can search for these exploits and any related information, resources, or downloadable tools that will help them exploit these systems. Now, imagine using this Exploit search engine for online devices you find on a Shodan search! Remember, with Shodan, there’s no hiding on the Internet…


[…] and banners from different public sources like popular search engines, PGP key servers, and the Shodan database. This program is particularly useful during the reconnaissance phase of gathering Open […]
LikeLike