Before I start, I hope you already have a great understanding of 802.11 networks!
A “Fake Access Point (AP)” is a type of wireless network attack in which an attacker uses software to create a malicious AP that is live and broadcasting out to wireless clients. Fake APs are rogue, and often times, the Service Set Identifier (SSID) and other configurations are set to entice wireless clients to connect to it, which can be very bad. In most cases, attackers create fake APs in order to steal username and password information. Fake APs can also be supplemented with other types of attacks, such as redirection attacks that “redirect” their victims to malicious web sites. For example, it’s very easy to clone a website, such as social media and bank login pages. Normally, web browsers encrypt our web sessions using SSL/TLS; however, if connected to a fake AP, this type of protection can be downgraded if the wireless client does not pay attention.

A variant of the Fake AP attack is when the attacker mimics the settings of a legitimate AP to create a virtually identical AP, called an “Evil Twin.” The SSID of both the legitimate AP and the fake AP are exactly the same. Likewise, if the attacker knows the passphrase and encryption type, they can also be the same.
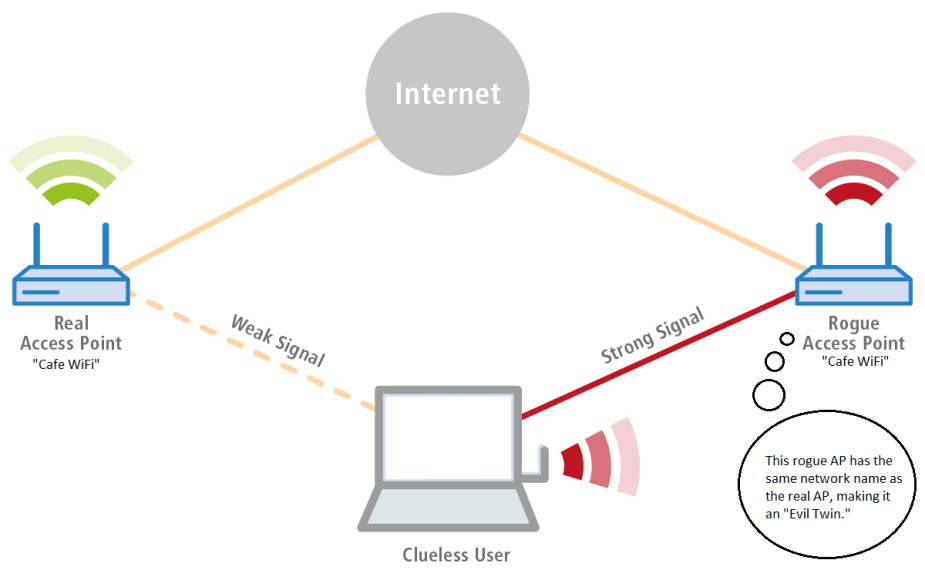
Evil Twins are particularly nasty because our operating systems “remember” previous WiFi networks we’ve connected to since they cache the SSID. Thus, if your mobile device has ever connected to a WiFi network with the SSID, “Cafe WiFi,” it will always automatically connect to any WiFi network with the same network name, regardless of whether or not they are truly the same network or not. Attackers often kick wireless clients off the legitimate AP using 802.11 deauthentication frames and increase the signal strength of their evil twin in order to force wireless clients to connect to it.
Prerequisites
For this demonstration, you’ll need to be running the latest version of Kali Linux. The second Kali Linux rolling release is 2018.2. Kali Linux is a Debian-based Linux distribution aimed at advanced penetration testing and ethical hacking. It comes pre-installed with hundreds of penetration testing programs, including aircrack-ng. Personally, I run Kali Linux on a Debian 9.x 64-bit VMware workstation.

You’ll also need a wireless network adapter that supports monitor mode. There are all sorts of network adapters out there that you can connect to your PC via USB. You can go for the adapters with the more conspicuous look (multiple big antennas) or the less conspicuous versions (USB flash stick-size). For now, I am using my Alfa AWUS036NHA.
Aircrack-ng & dnsmasq
One of my all-time favorite Wi-Fi assessment tools is Aircrack-ng. This program is a suite of wireless penetration testing tools, including airbase-ng, aircrack-ng, airdecap-ng, airdecloak-ng, airdrop-ng, aireplay-ng, airmon-ng, airodump-ng, and much more. We will be using many of these programs in this demonstration, and it’s all pretty easy. Aircrack-ng was just updated to version 1.3 this month (July 2018), so it will require an update. Here’s a list of some of the options Aircrack-ng provides.

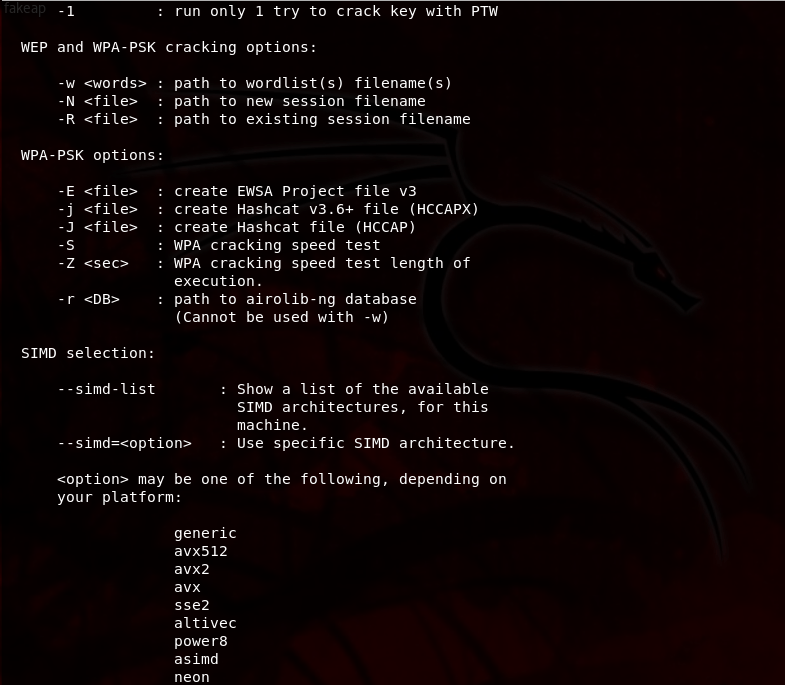

So, what exactly can we do with Aircrack-ng? Test 802.11b/g/n networks of course! If we have the correct wireless network adapter, we can eavesdrop by sniffing wireless traffic. We can crack WEP/WPA/WPA2 passphrases by performing various types of attacks, including fragmentation and dictionary attacks with assistance of packet injection techniques. We could even deauthenticate (a type of DoS) clients from the network. And, of course, we can create fake APs and evil clones. Overall, you can gather an overly-abundant amount of information on wireless networks using Aircrack-ng.
On the other hand, dnsmasq is a nifty and complex program that provides Domain Name System (DNS) forwarding. As you should already know, DNS is responsible for resolving name queries, which allows us to surf the World Wide Web (WWW) and visit Web sites. The dnsmasq program assists in providing DHCP clients access to the Internet by forwarding their DNS queries to actual DNS servers or recursive resolvers of our choosing. Speaking of DHCP, dnsmasq also supports DHCP server capabilities for both static and dynamic configurations.
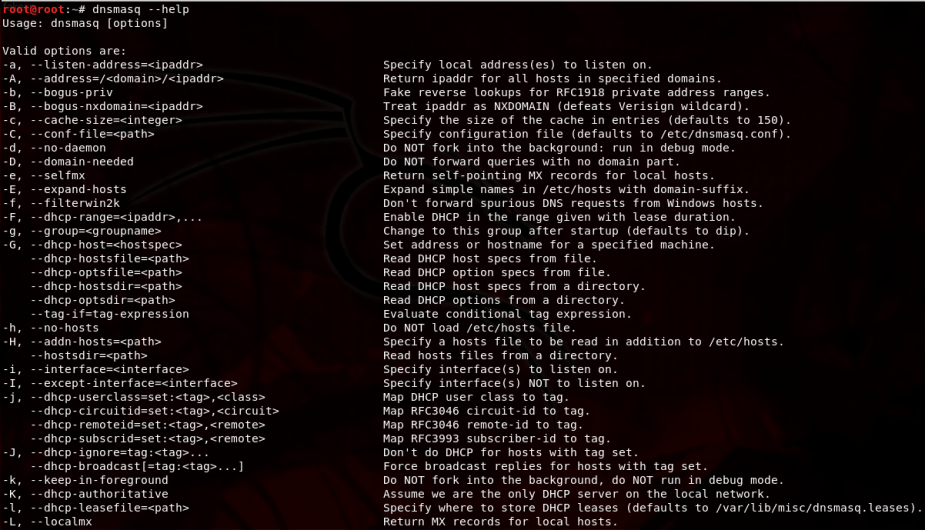


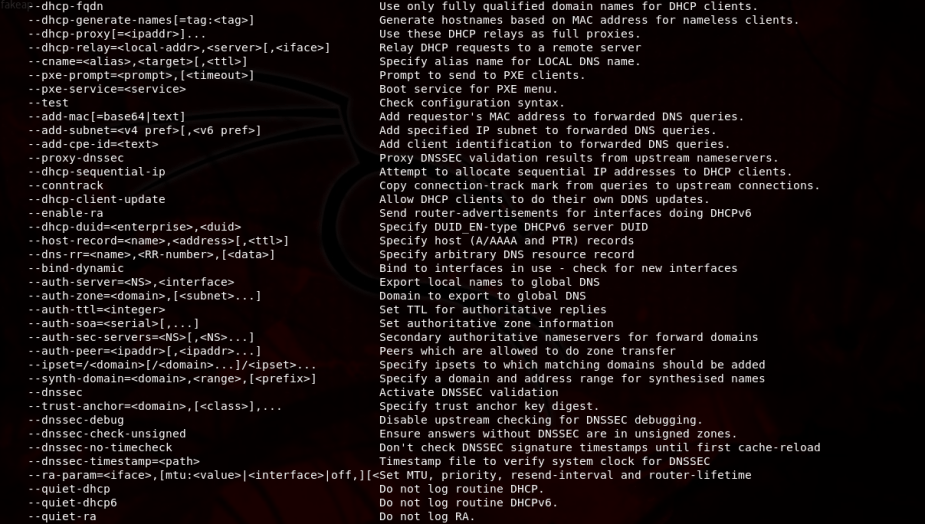

Clearly…there’s lot of configuration options. Thankfully, we don’t need to worry about that as we will only need to make a few configuration changes here-and-there. With the help of dnsmasq, clients who connect to our evil twin or fake AP will be leased an IP address and be able to use the Internet.
With the introduction covered, let’s move on to the setup.
Step 1: Update Aircrack-ng
Because Aircrack-ng, the wireless penetration testing suite, already comes pre-installed in Kali Linux, you can execute the apt-get update && apt-get upgrade command. Not only will this download package lists from the Kali Linux repositories, but it will also update them. Newer versions of the packages will also be upgraded.

The entire process can take as long as 10 minutes, but it’s entirely worth the extra time to have updated programs. The latest version of Aircrack-ng is version 1.3.
Step 2: Install dnsmasq
If you don’t already have it, the next step is to download dnsmasq. This can be accomplished using a similar apt command, apt-get install dnsmasq.

Dnsmasq comes with its own dnsmasq.conf file stored in the /etc/ folder. We can view this configuration file by executing the nano /etc/dnsmasq.conf or leafpad /etc/dnsmasq.conf command. Trust me, it’s an extremely long file, and luckily, we won’t be making any changes to this file, but we could definitely use it for this demonstration if we wanted to.
Step 3: Create an “eviltwin” Folder in Desktop
Change the current path to the Desktop using the cd Desktop command and make a new directory called “eviltwin” by executing the mkdir eviltwin command. After that, navigate to the evil twin folder by executing cd eviltwin/. The current path should now be Desktop/eviltwin/. This is where we will create and store a new dnsmasq.conf file, so let’s create this new file by executing the nano dnsmasq.conf command.

The preceding output is what you should see in the terminal. After we press [Enter], an empty GNU nano text editor file will open. Add the following parameters to this file, save it [ctrl+s], and quit [ctrl+x].
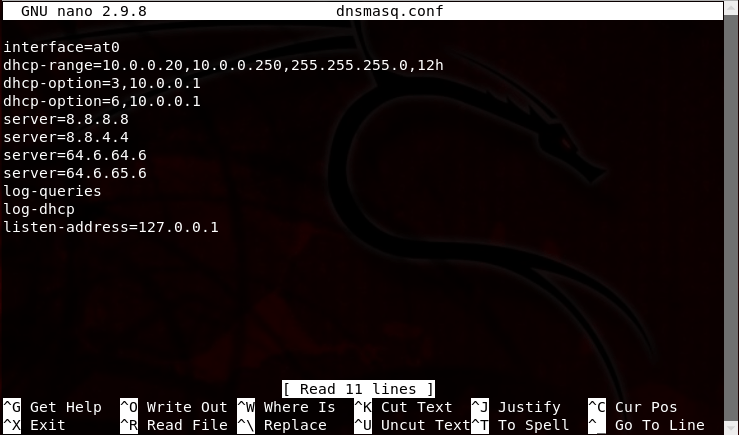
This tutorial isn’t going to be very helpful if you don’t actually know what these parameters mean. If you’re a network technician, then you probably know exactly what’s going on in this configuration file. Nevertheless, I’ll walk through what each line means.
- Interface=at0: The at0 interface is a fake interface we will bring up in step 4. Airbase-ng will use this interface to create the evil twin or fake AP.
- dhcp-range=10.0.0.20,10.0.0.250,255.255.255.0,12h: We will be using a 10.0.0.0/24 network for this demonstration (You could, however, use 192.168.1.0/24 if you wanted). A /24 means the subnet mask is 255.255.255.0 and that also means we only have 254 available host addresses that our fake DHCP server can lease out. However, I am only going to use host addresses between 10.0.0.20 through 10.0.0.254. Why? Because I want to. You can use whatever addresses you wish, but just don’t use 10.0.0.0, 10.0.0.1, or 10.0.0.255. This is because 10.0.0.0 is reserved for the network address, 10.0.0.1 will be our gateway address, and 10.0.0.255 is broadcast address (again, it helps to already have networking knowledge). Each DHCP binding will last for 12 hours
- dhcp-option=3,10.0.0.1: Enabling DHCP option 3 helps specify the gateway, which will be 10.0.0.1. That is my actual gateway address.
- dhcp-option=6,10.0.0.1: Enabling DHCP option 6 will automatically configure our DHCP clients to use the DNS servers we provide, rather than the DNS servers provided by the gateway.
- server=: On lines 5 – 8, I’ve specified several different public DNS servers here. With this configuration, dnsmasq will forward DNS requests from out clients to the following public DNS servers: 8.8.8.8, 8.8.4.4, 64.6.64.6, and 64.6.65.6. These are DNS servers provided by Google and VeriSign, respectively.
- log-queries: By logging queries, we get to see what web sites our DHCP clients are making DNS queries to. This information will appear in the terminal later on.
- log-dhcp: By logging DHCP information, we will get to see current DHCP bindings. This is helpful to see currently leased IP address information.
- listen-address=127.0.0.1. The listen-address is always the loopback address 127.0.0.1.
Now that Aircrack-ng is updated and we’ve configured our new dnsmasq.conf file in /Desktop/eviltwin/, we can now commence the attack. If you’re ready to move on, click here to move on to PenTest Edition: Creating an Evil Twin or Fake Access Point on Your Home Network Using Aircrack-ng and Dnsmasq [Part 2 – the Attack].


[…] you haven’t already begun the initial startup, you’ll need to go back to Creating an Evil Twin or Fake Access Point Using Aircrack-ng and Dnsmasq [Part 1 – Setup] and update Aircrack-ng and configure the dnsmasq configuration file. After that, you can come back […]
LikeLike