The National Institute of Standards and Technology has recently released version 1.1 of the Cybersecurity Framework (CSF), designed to improve the cybersecurity of industries, companies, and organizations that are a part of the nation’s critical infrastructure (e.g., energy, power, banking, communications, defense, etc.). The CSF is a voluntary framework that was originally developed in response to Executive Order 13636. The purpose of the CSF was not only to improve cybersecurity practices, but to also be flexible, repeatable, and cost-effective. Less than half of the organizations and industries that are a part of the critical infrastructure are complying with the CSF; however, this is expected to improve by the year 2020. The new CSF 1.1 includes updates on authentication and authenticity, self-assessments for cybersecurity risks, managing cybersecurity within the supply chain, and vulnerability disclosure.
The Framework Core
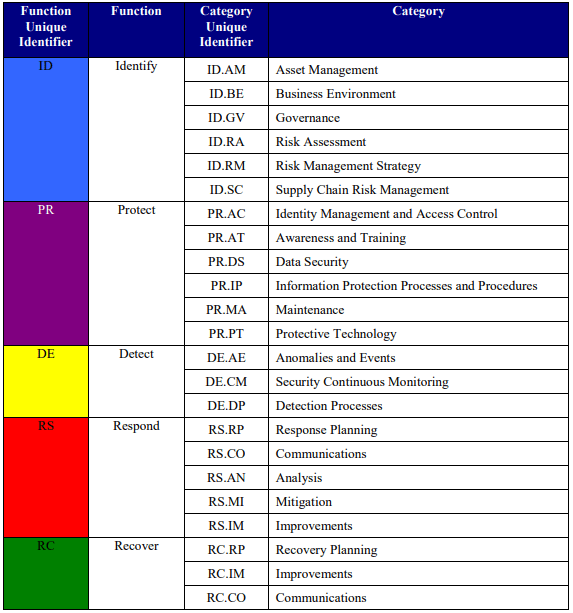
The CSF consists of a construct called the Framework Core. The goal here is to provide everyone, even those who might be technologically illiterate, with a common language to understand, manage, and express cybersecurity risks. Similar to NIST SP 800-53 and FIPS 199, the Framework Core helps organizations identify and prioritize actions for reducing risk. A “risk” is the likelihood that a vulnerability in our information systems is exploited and results in an adverse effect. The Framework Core provides organizations with a set of 5 cybersecurity functions to achieve specific outcomes, 22 categories that subdivide the 5 functions for programmatic needs and particular activities, 98 subcategories that further divide the outcomes, and informative references that assist organizations in following standards and best practices. This Framework Core structure is depicted below.

The first 5 functions of the Core Framework are as follows:
- Identify: Understand your organization’s business setting, the resources, the security controls that support critical functions, and the related cybersecurity risks of your critical and non-critical assets. This enables an organization to focus and
prioritize its efforts, consistent with its risk management strategy and business needs. - Protect: Develop appropriate security controls to safeguard and mitigate the risks you have identified to ensure business continuity.
- Detect: Develop ways to uncover and continually monitor for threats to your organization.
- Respond: Expand on your response to threats when they emerge. There is a great methodology already laid out in the guidelines established in NIST SP 800-61 (revision 2).
- Recover: Refine your recovery strategy that proves its resilience and capability to recover efficiently and in a timely manner that follows your organization’s recovery time objectives.
These are the 5 high-level functions addressed in the Framework Core, which are then subdivided into 22 Categories of different outcomes for each function. For example, if your organization wants to improve the way in which the correct employees access the correct resources in the “Protect” function, this would fit the “Identity Management and Access Control” category, to which you will then choose a fitting outcome from the 98 subcategories. The Categories are depicted below (Note “Communications” is stated twice because it is included in the “Respond” and “Recover” function):
The 98 Subcategories further divide a category mentioned above into more-specific outcomes. Therefore, a subcategory from the “Identity Management and Access Control” category might be “Access permissions and authorizations are managed, incorporating
the principles of least privilege and separation of duties.” I won’t name all 98 Subcategories! But, if you’d like to review them, you can see them in Appendix A, page 24 here.
The Informative References identifies standards, guidelines, and practices
common among critical infrastructure sectors that illustrate a method to achieve the
outcomes associated with each Subcategory. For example, if there’s specific guidelines or standards for a chosen subcategory, it would be mentioned (e.g, ISO/IEC 27001 or COBIT). Informative References are also in Appendix A, page 24. Click here.
The Framework Implementation Tiers
The Framework Implementation Tiers describe the level of meticulousness, or “rigor and sophistication,” involved in an organization’s cybersecurity risk management practices. The Tiers take a lot into consideration, such as the organization’s current risk framework, its degree of privacy considerations, threat environment, information sharing practices, mission objectives, and technical or operational constraints.
- Tier 1 = Partial: This means that the organization’s risk management practices are unofficial and informal. Tier 1 organizations really only manage risk reactively and may not be as informed about risk as they should. This may be because senior leaders are limited or uninformed about cybersecurity risks, which reflects a cybersecurity risk framework that is irregular or practiced on a case-by-case basis. Tier 1 organizations are also described as not understanding the importance of their role in protecting themselves and the other entities that depend on them (e.g, the critical infrastructure, private sector companies, stakeholders, etc.). These organizations are generally described as unaware and are not proactively seeking solutions to their cybersecurity framework. They are also unaware of their importance in the supply chain.
- Tier 2 = Risk Informed: Organizations at Tier 2 implement approved risk management practices, but needs improvement. For example, the organization has policies, processes, or programs that are intended to reduce risk, but they are not frequently enforced or implemented at an organizationally-wide level. With that being said, these organizations are certainly “risk-informed,” but could improve on the informal processes in which they share cybersecurity risk information within the organization. A Tier 2 organization incorporates risk assessments, but not on a continual basis. These organizations also collaborate with other entities for information sharing purposes, but not with others.
- Tier 3 = Repeatable: This is an organization with formally approved risk management practices that are regularly updated to reflect the ever-evolving landscape of cybersecurity, threats, technology, and the business itself. Tier 3 organizations have an organizationally-wide approach to managing risk. Policies, processes, and procedures are all clearly defined at all levels of the organization and continually monitored or reviewed. Personnel are all aware of their roles and responsibilities and communication within the organization is approved. Unlike Tier 1 and 2 organizations, Tier 3 organizations have a full understanding of their role, dependencies, and dependents in the larger ecosystem, which may contribute to the community’s broader understanding of risks.
- Tier 4 = Adaptive: Organizations at Tier 4 are extremely competent on the best cybersecurity risk practices. They are not only continually monitoring and reviewing their framework, but constantly adapting. They incorporate advanced technologies and practices into their framework at all levels of the organization. They routinely share information internally and externally and completely understand their role in the context of their dependents and dependencies. Cybersecurity risk management is reflected in their organizational culture. Basically, they get an A+.
When feasible, Tier 1 organizations should strive to move toward the higher Tier levels as their cybersecurity management framework practices are deemed subpar. The Tier level, however, does not reflect the organization’s maturity level. A Tier categorization is intended to reveal to the organization what their current priorities are and which areas could improve.
The Framework Profile
Section 2.3 of the CSF is the Framework Profile, which describes the state of the organization with regard to the Functions, Categories, and Subcategories and the organization’s business requirements, risk tolerance, and resources. The Framework Profile also describes the current status of the organization, what it could be, and how it could reach that desired status by aligning their priorities with the correct organizational goals and best practices. The organization’s Current Profile is the present status of the organization, which is the outcomes currently being achieved whereas the Target Profile is the desired status and the outcomes needed to achieve this level of risk management goals.
A comparison of an organization’s Current Profile and Target Profile will reveal gaps that need to be addressed, which can be mitigated in an action plan that identifies the categories and subcategories identified in the Framework Core. This action plan aligns with the organization’s budget and business needs, which allows the organization to identify the resources it needs to achieve its Target Profile in a cost-effective manner.
How to Use the Framework
Section 3.0 of the CSF details how to use the framework. The CSF is not designed to replace existing processes, but rather to compliment an organization’s existing cybersecurity operations. It can also be used as a foundation to improve an existing program or in creating a new program.
As previously mentioned, the CSF can be used by organizations to build a Current Profile of their cybersecurity framework and a desired Target Profile of what the organization “could be.” This will allow organizations to identify what they are currently prioritizing, and if need be, make strategic decisions regarding their cybersecurity implementations by addressing any discovered gaps or constraints to achieve the outcomes in their Target Profile.
The CSF also describes a common language in which organizations can communicate their cybersecurity requirements with stakeholders, especially in the supply chain. The supply chain itself is so complex, that the CSF created a new function called, Supply Chain Risk Management (SCRM).
Supply chains are complex, globally distributed, and interconnected sets of resources and processes between multiple levels of organizations. Supply chains begin with the sourcing of products and services and extend from the design, development, manufacturing, processing, handling, and delivery of products and services to the end user…[SCRM] is the set of activities necessary to manage cybersecurity risk associated with external parties. More specifically, cyber SCRM addresses both the cybersecurity effect an organization has on external parties and the cybersecurity effect external parties have on an organization.
Tier 3 and 4 organizations are completely aware of SCRM. The goal of SCRM is to identify and mitigate any threats discovered in the supply chain regarding the products and services that organizations produce and buy. This is important because some products could be faulty, contain a malicious functionality, or contain vulnerabilities due to poor manufacturing. For that reason, a few key SCRM activities include determining the cybersecurity requirements for suppliers, enacting these requirements through formal agreements or contracts, and verifying that the requirements are met.
Self-Assessing Cybersecurity Risk
The updated version of the CSF contains a self-assessment section, which helps organizations make informed choices regarding which Tier to target and how to evaluate their current approach to addressing cybersecurity risk by reflecting on their current Tier. Upon a thorough self-assessment, organizations can prioritize outcomes by developing their own Target Profile. Again, by addressing the gaps in their Current Profile and Target Profile, organizations can address what they need via the technical guidance of the Informative References identified in the Framework Core.
Conclusion
I think this lays out the foundation of CSF-1.1, or it’s at least a good summary. Seeing as the CSF is 48 pages, it helps to have a resource that condenses the material into its key elements.
References
The National Institute of Standards and Technology. (2018). The Framework For improving Critical Infrastructure (version 1.1). Retrieved from the National Institute of Standards and Technology Web site: https://nvlpubs.nist.gov/nistpubs/CSWP/NIST.CSWP.04162018.pdf

[…] section, which I cover here. Yesterday, I published a blog post about the new version of the cybersecurity framework. This document would also be a good resource for preparation. Even though it’s aimed towards […]
LikeLiked by 1 person